➤Summary
Fake VS Code alerts have emerged as one of the most dangerous cybersecurity threats targeting developers today. A recent large-scale GitHub malware campaign exploited trust in developer tools by distributing convincing security warnings that tricked users into downloading malicious payloads. According to research highlighted by BleepingComputer, attackers automated fake discussions across thousands of repositories, generating mass notifications that appeared legitimate. This tactic demonstrates how modern threat actors increasingly weaponize collaboration platforms to bypass traditional defenses. Developers, DevOps teams, and organizations relying on open-source ecosystems are particularly vulnerable because these attacks exploit routine workflows rather than technical vulnerabilities. Understanding how fake alerts operate, why they spread so quickly, and how to defend against them is now essential for maintaining developer security and protecting software supply chains. ⚠️
How the Fake VS Code Alerts Campaign Works
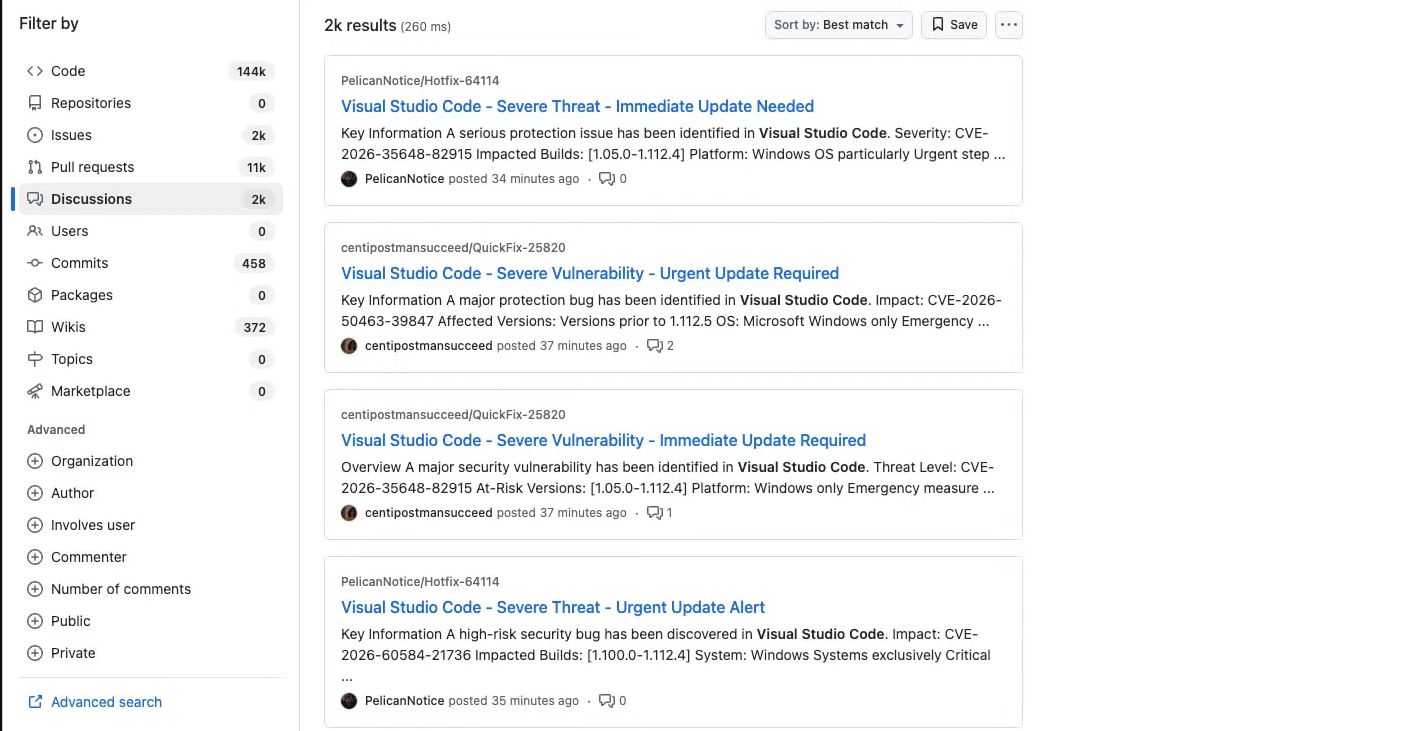
The GitHub malware campaign relies heavily on social engineering rather than complex exploits. Attackers create automated accounts and post fake warnings claiming a vulnerability exists in Visual Studio Code extensions or repositories.
As reported by BleepingComputer, “discussions are posted in an automated way from newly created or low-activity accounts across thousands of repositories within minutes,” triggering notification emails to tagged users and followers.
This approach achieves three powerful outcomes:
- Immediate visibility through GitHub notifications
- Artificial legitimacy via repository discussions
- Rapid malware distribution through trusted environments
Once developers click the provided link, they are redirected to malicious downloads disguised as patches or updates. These payloads often install information stealers, remote access trojans, or credential harvesters. 🚨
The attack succeeds because developers are trained to respond quickly to security alerts. When the message references VS Code, a widely trusted tool, suspicion drops significantly.
Why Developers Are the Primary Target
Developers hold valuable assets: API keys, cloud credentials, SSH tokens, and access to production systems. A successful phishing attack targeting a single developer can escalate into a full supply chain compromise.
Threat actors understand that:
- Developers frequently install tools and extensions
- Open-source collaboration encourages trust
- Security alerts demand fast action
This makes fake notifications extremely effective. The fake VS Code security alerts on GitHub scenario demonstrates how attackers blend into normal workflows instead of exploiting software bugs directly.
Modern malware distribution increasingly focuses on identity compromise rather than infrastructure attacks. Once access is obtained, attackers can inject malicious code into repositories or steal proprietary data.
Key Warning Signs of Fake Security Alerts
Recognizing suspicious behavior early can prevent infection. Here are common indicators developers should watch for:
| Warning Sign | Explanation |
| Newly created accounts | Attackers often use low-activity profiles |
| Urgent language | “Critical vulnerability detected” messaging |
| External download links | Updates hosted outside official sources |
| Mass tagging | Automated mentions across repositories |
| Unverified attachments | Executables disguised as fixes |
| A practical rule: legitimate VS Code alerts rarely require downloading files from unknown domains. | |
| Practical Tip ✅: Always verify alerts through official Microsoft or repository maintainers before taking action. |
The Role of Automation in Malware Spread
Automation makes this campaign especially dangerous. Bots can publish thousands of discussions within minutes, overwhelming moderation systems.
Attackers leverage:
- Scripted account creation
- AI-generated phishing messages
- Automated repository scanning
- Bulk notification triggering
This scalability transforms a simple phishing attack into a global developer threat within hours. 😨
Security researchers note that these attacks resemble marketing automation techniques—except used for malicious intent.
Real Impact on the Software Supply Chain
The consequences extend far beyond individual victims. Compromised developers can unintentionally distribute malware to users downstream.
Potential impacts include:
- Injection of malicious dependencies
- Credential theft leading to cloud breaches
- Unauthorized repository changes
- Corporate data exposure
This evolution mirrors previous supply chain attacks but introduces a new entry point: developer communication channels.
An expert cybersecurity analyst summarized it well:
“Attackers no longer break systems; they convince trusted users to open the door.”
Organizations must therefore monitor not only infrastructure but also developer ecosystems.
Why Dark Web Intelligence Matters Today
Cybercriminal campaigns rarely begin on public platforms. Planning often occurs in hidden communities where threat actors exchange tools and strategies.
This is where underground forum monitoring becomes critical. Tracking discussions on hidden marketplaces allows organizations to identify emerging attack techniques before they reach mainstream platforms.
A proactive approach combines:
- Threat intelligence collection
- behavioral monitoring
- early phishing detection
Solutions like help organizations identify leaked credentials and attacker conversations connected to active campaigns.
By correlating GitHub activity with dark web chatter, security teams gain early warning signals that traditional antivirus tools cannot detect. 🔍
How Real-Time Monitoring Prevents Developer Attacks
A modern defense strategy requires visibility beyond endpoints. A real-time dark web monitoring solution enables organizations to detect stolen credentials or discussions referencing targeted repositories.
Key advantages include:
- Early breach detection
- Continuous threat tracking
- Automated alerts for exposed data
- Reduced incident response time
When attackers prepare phishing infrastructure, traces often appear in underground channels first. Monitoring these signals provides valuable lead time.
Organizations integrating monitoring platforms such as strengthen protection against evolving malware campaigns.
Question Developers Often Ask
Can fake GitHub alerts really compromise an entire company?
Yes. A single compromised developer account can expose source code, deployment pipelines, and cloud environments. Because developers often have elevated privileges, attackers can pivot quickly across systems once access is obtained.
Checklist: How to Stay Safe from Fake Alerts
Use this quick checklist to reduce risk immediately:
✅ Verify alerts through official sources
✅ Avoid downloading patches from discussion threads
✅ Enable multi-factor authentication on GitHub
✅ Monitor unusual repository mentions
✅ Scan downloads in isolated environments
✅ Use threat intelligence and monitoring tools
Adopting these practices significantly lowers exposure to phishing and social engineering threats. 🛡️
Affordable Protection Strategies for Teams
Security solutions are often perceived as expensive, but modern platforms offer scalable protection options. An affordable dark web monitoring service allows startups and mid-size teams to access enterprise-level intelligence without large budgets.
Benefits include:
- Continuous credential leak detection
- Monitoring of malicious actor discussions
- Alerts tied to developer identities
- Simplified risk management
Organizations that invest early in monitoring dramatically reduce recovery costs after incidents.
For deeper insights, explore resources available through Darknetsearch.com, which provides guidance on identifying emerging threats affecting developers.
The Future of Developer-Targeted Cyberattacks
The rise of Fake VS Code alerts signals a broader shift in cybercrime strategy. Attackers increasingly target trust layers rather than technical vulnerabilities.
Emerging trends include:
- AI-generated phishing conversations
- impersonation of security maintainers
- malicious pull requests
- fake vulnerability disclosures
As collaboration platforms expand, attackers will continue exploiting notification systems and human psychology.
The GitHub malware campaign model will likely evolve into multi-platform attacks involving Slack, Discord, and package registries.
Conclusion: Awareness Is the Strongest Defense
The recent surge of Fake VS Code alerts highlights a critical lesson: cybersecurity is no longer just about software—it is about behavior, trust, and visibility. Developers must question unexpected alerts, organizations must monitor external threat environments, and security teams must adopt proactive intelligence strategies.
Ignoring these warning signs can lead to credential theft, supply chain compromise, and widespread malware infections. Staying informed and implementing monitoring solutions ensures threats are detected before damage occurs. 🌐
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

