➤Summary
Credential exposure risks are once again in the spotlight as the recent compromise of the Bitwarden CLI tool emerges as part of a broader supply chain campaign linked to Checkmarx. This incident highlights how even trusted security tools can become attack vectors when dependencies are poisoned. For organizations relying on developer tools and automation pipelines, the implications are serious—especially in an era where dark web surveillance and underground forum monitoring are essential for early threat detection. 🚨
What happened
The incident centers around a malicious supply chain attack targeting the Bitwarden CLI, as detailed in official statements and reporting from Bitwarden Community Forum and The Hacker News. Attackers reportedly leveraged a compromised dependency within the development ecosystem, allowing them to inject malicious code into the CLI tool used by developers for secure credential management.
This attack is part of a wider campaign attributed to the Checkmarx supply chain incident, where attackers targeted widely used development tools and libraries. By infiltrating trusted software pipelines, they effectively bypass traditional perimeter defenses.
The malicious package was capable of exfiltrating sensitive information during runtime, particularly when developers executed commands involving secrets or authentication tokens.
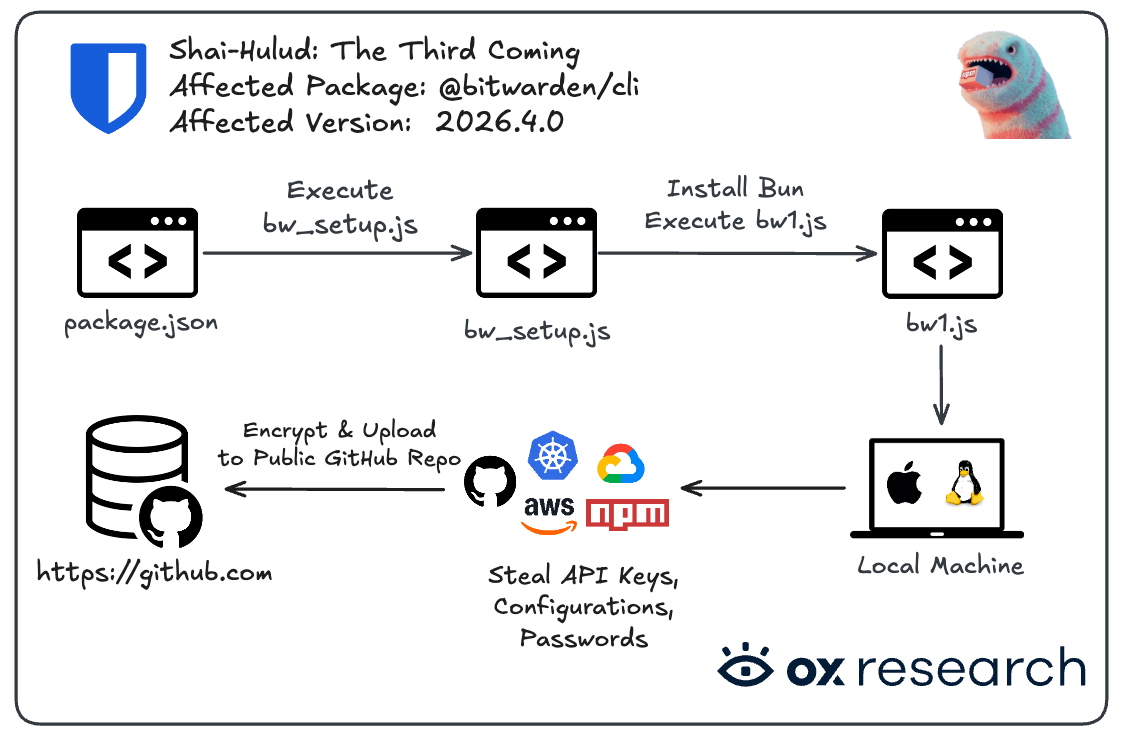
Bitwarden CLI Attack Chain | Source: OX Security
This kind of attack underscores the growing sophistication of adversaries exploiting open-source ecosystems.
Data exposed
While Bitwarden clarified that its core infrastructure remains secure, the compromised CLI tool may have exposed:
- User credentials accessed via CLI commands
- API keys and authentication tokens
- Environment variables used in development pipelines
- Potential vault access metadata (depending on usage)
This type of exposure is particularly dangerous because it targets highly privileged users—developers and DevOps engineers—who often have elevated access across systems. 🔐
From a dark web surveillance perspective, such credentials can quickly surface on underground marketplaces or private leak forums. Attackers often monetize these assets within hours, making underground forum monitoring critical for early detection.
Notably, even limited exposure can cascade into larger breaches if attackers pivot using stolen credentials.
Why dangerous
Supply chain attacks are uniquely dangerous because they exploit trust. Instead of attacking an organization directly, adversaries compromise the tools it depends on.
Here’s why this incident matters:
- Stealthy infiltration: Malicious code is executed within trusted environments
- Wide impact: A single compromised dependency can affect thousands of users
- Difficult detection: Traditional security tools may not flag trusted packages
- Privilege escalation: Developers’ credentials often grant deep system access
This is why dark web surveillance has become a cornerstone of modern cybersecurity strategies. Organizations can no longer rely solely on prevention—they must assume exposure and monitor continuously.
Additionally, underground forum monitoring helps identify whether stolen credentials or tokens are being traded or discussed in real time.
💡 Expert insight: “Supply chain attacks are no longer edge cases—they are becoming the default attack vector for sophisticated threat actors.”
Who is at risk
The scope of risk extends beyond Bitwarden CLI users. The following groups are particularly vulnerable:
- Development teams using CLI-based credential management
- Organizations with CI/CD pipelines relying on third-party packages
- Companies lacking visibility into software dependencies
- Enterprises without dark web surveillance capabilities
- Startups and SMBs with limited security resources
A key question arises: Can a single compromised tool really lead to a full breach?
Answer: Yes. If that tool handles authentication or secrets, attackers can gain footholds that lead to lateral movement across systems.
This is where solutions like DarknetSearch come into play, offering proactive underground forum monitoring to detect early signs of compromise before attackers escalate access. 🕵️♂️
How to prevent
Preventing supply chain attacks requires a layered approach combining prevention, detection, and response.
Here’s a practical checklist organizations should follow:
- Verify all dependencies and use signed packages
- Implement least privilege access for CLI tools
- Rotate credentials frequently and automatically
- Monitor logs for unusual CLI activity
- Deploy dark web surveillance tools to detect leaks early
- Integrate underground forum monitoring into threat intelligence workflows
- Use secure secrets management solutions
- Conduct regular security audits of development pipelines
Practical tip: Always isolate development environments and avoid storing sensitive credentials in plaintext or environment variables whenever possible.
Organizations looking for the best dark web monitoring tools should prioritize solutions that combine automation, real-time alerts, and deep coverage of underground sources.
Why dark web surveillance is critical in 2026
The Bitwarden CLI incident reinforces a critical reality: breaches are no longer a matter of “if” but “when.” What matters is how quickly organizations detect and respond.
Dark web surveillance enables:
- Early detection of leaked credentials
- Identification of targeted attacks
- Monitoring of threat actor activity
- Rapid incident response
Meanwhile, underground forum monitoring provides visibility into closed communities where attackers trade and discuss stolen data.
Together, these capabilities form a proactive defense strategy that complements traditional security controls.
Conclusion
The Bitwarden CLI compromise is a stark reminder that even security tools can become liabilities when supply chains are compromised. As attackers continue to exploit trusted ecosystems, organizations must evolve their defenses beyond traditional measures.
Dark web surveillance and underground forum monitoring are no longer optional—they are essential components of a resilient cybersecurity posture. By combining proactive monitoring with strong internal controls, companies can significantly reduce their exposure and respond faster to emerging threats. 🔍
DarknetSearch provides advanced capabilities to track leaked data, monitor underground activity, and alert organizations before incidents escalate. In a landscape defined by supply chain attacks, visibility is your strongest defense.
👉 Is your company exposed to similar risks?
→ Start Free Trial
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat intelligence sources. Inclusion does not imply confirmed compromise.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

