➤Summary
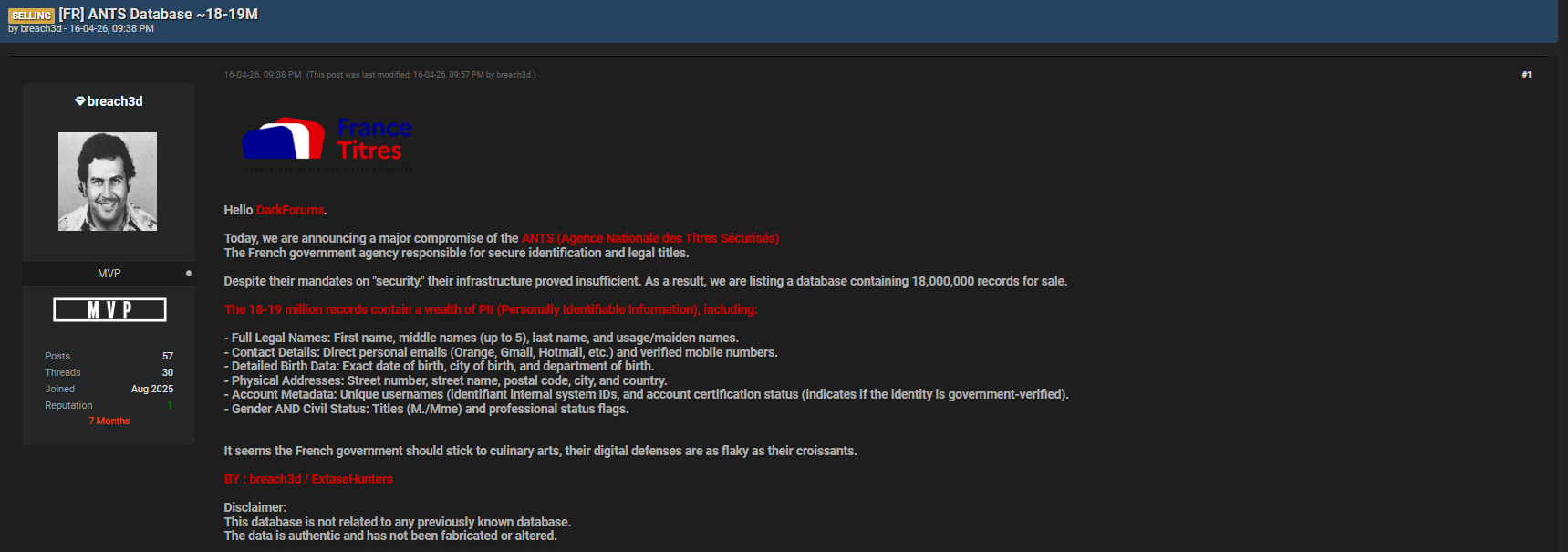
Dark web surveillance has become a critical cybersecurity practice as massive data leaks continue to expose sensitive personal information at scale. A recent case allegedly linked to Agence Nationale des Titres Sécurisés (ANTS) highlights just how dangerous these exposures can be. Reportedly shared on Darkforums by a threat actor known as breach3d, the dataset contains between 18 and 19 million records filled with highly sensitive personal data.
This incident underscores why organizations must invest in identity theft monitoring and proactive intelligence tools to detect leaks before they escalate into fraud, compliance violations, or reputational damage. In this guide, we break down how dark web surveillance works, how attackers exploit such data, and how businesses can defend themselves effectively. 🚨
Definition of Dark Web Surveillance
Dark web surveillance refers to the continuous monitoring of hidden online environments—such as underground forums, marketplaces, and encrypted networks—where stolen data is traded, leaked, or sold.
Unlike traditional cybersecurity tools that focus on perimeter defense, dark web monitoring provides visibility into what happens after a breach occurs. It enables organizations to identify exposed credentials, leaked databases, and compromised identities in real time.
In the ANTS-related case, the leaked dataset reportedly includes:
- Full legal names (including multiple middle names and maiden names)
- Email addresses and mobile phone numbers
- Date and place of birth
- Complete physical addresses
- Internal account identifiers and verification status
- Gender and civil/professional status
This level of detail makes the dataset extremely valuable for cybercriminals conducting fraud or impersonation attacks. 🔍
How Dark Web Surveillance Works
Dark web surveillance operates through a combination of automated tools, human intelligence, and advanced analytics. Here’s how it typically works step by step:
- Data Crawling: Specialized systems scan dark web forums, marketplaces, and leak sites continuously.
- Data Collection: Extracted content includes credentials, databases, and breach discussions.
- Data Matching: Information is compared against company assets such as domains, employee emails, or customer records.
- Threat Analysis: Security teams assess the severity and potential impact of the exposure.
- Alerting & Response: Organizations receive alerts and can take action immediately.
Platforms like DarknetSearch.com provide this capability at scale, enabling businesses to detect leaks like the ANTS dataset before they are widely exploited.
How Attackers Use Leaked Data
Once data appears on underground forums like Darkforums, it becomes a resource for multiple types of cybercrime. Attackers can:
- Launch phishing campaigns using real personal details
- Perform identity fraud and account takeovers
- Conduct SIM swapping attacks using phone numbers
- Build synthetic identities for financial fraud
- Target individuals with social engineering
For example, combining birth data, addresses, and verified account status allows attackers to bypass identity verification systems. This is particularly dangerous in government-related datasets like ANTS, where records are often considered highly trustworthy. ⚠️
A confirmed report about the breach context can be found here:
🔗 https://www.bleepingcomputer.com/news/security/french-govt-agency-confirms-breach-as-hacker-offers-to-sell-data/
Business Risks of Data Exposure
The exposure of millions of records is not just a privacy issue—it creates significant business risks:
- Regulatory penalties: Violations of GDPR can lead to heavy fines
- Reputation damage: Loss of customer trust can be long-lasting
- Financial fraud: Increased risk of fraudulent transactions
- Operational disruption: Incident response and remediation costs
- Legal liabilities: Potential lawsuits from affected individuals
Organizations relying on government data or identity verification services face even higher risks due to the sensitivity and accuracy of the information.
💡 Expert insight: “The real danger is not the breach itself, but how quickly attackers weaponize the data afterward.”
Detection and Mitigation Strategies
To protect against threats revealed through dark web surveillance, organizations should adopt a multi-layered approach:
- Implement identity theft monitoring for employees and customers
- Use threat intelligence platforms like DarknetSearch
- Enforce multi-factor authentication (MFA)
- Regularly audit data storage and access controls
- Monitor unusual login or transaction behavior
Practical Checklist ✅
- Monitor dark web forums daily
- Scan for exposed credentials and PII
- Enable real-time alerts for leaks
- Educate employees on phishing risks
- Test incident response plans regularly
These steps help reduce the time between detection and response, which is critical in limiting damage. 🛡️
Real-World Example: ANTS Data Leak Impact
The alleged ANTS dataset demonstrates how large-scale identity data can be exploited:
- Verified identities increase fraud success rates
- Detailed personal data enables targeted attacks
- Government-linked datasets carry higher trust value
Question: Why is government-related data more dangerous when leaked?
Answer: Because it is often verified and trusted, making it easier for attackers to bypass security checks and impersonate individuals successfully.
Why Identity Theft Monitoring Matters
Identity theft monitoring is no longer optional—it is a core component of modern cybersecurity. It allows organizations to:
- Detect compromised identities early
- Prevent fraud before it escalates
- Protect customers and employees
- Maintain compliance with data protection laws
When combined with dark web surveillance, it provides a complete view of both internal and external threats. 🔐
Conclusion: Turning Intelligence into Action
The ANTS-related data exposure is a powerful reminder that no organization is immune to large-scale breaches. The real differentiator is how quickly and effectively companies respond. By leveraging dark web surveillance and identity theft monitoring, businesses can move from reactive defense to proactive threat intelligence.
See if your company is exposed
→ Start Free Trial 🚀
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

