➤Summary
Zealthy Healthcare data breach allegations surfaced in early 2026, sparking serious concern across the U.S. healthcare and cybersecurity landscape. According to multiple forum posts, an alleged database belonging to Zealthy Healthcare may have been compromised, affecting more than 2.1 million patients nationwide. The claims indicate that sensitive personal and medical-related data was offered for sale on underground forums, raising urgent questions about patient privacy, regulatory exposure, and identity theft risks. While the incident has not yet been formally confirmed by the organization, the scale and nature of the exposed information make this alleged breach impossible to ignore. Healthcare data is among the most valuable commodities on cybercrime markets, and incidents like this highlight why healthcare cybersecurity remains a top priority in 2026. In this darknetsearch.com article, we break down what is known so far, what data may be involved, who could be impacted, and what practical steps individuals and organizations should consider right now 🚨
What Is Allegedly Known About the Zealthy Healthcare Incident
The alleged Zealthy Healthcare data breach was first published on February 24, 2026, on the well-known hacking forum BreachForums. The forum post was authored by a user known as “2019,” a name previously associated with large-scale data leak disclosures. According to the listing, the compromised database allegedly contains records tied to over 2.1 million patients in the United States. The seller described the leak as a “one-time sale,” a tactic often used to increase perceived exclusivity and urgency among buyers 💻
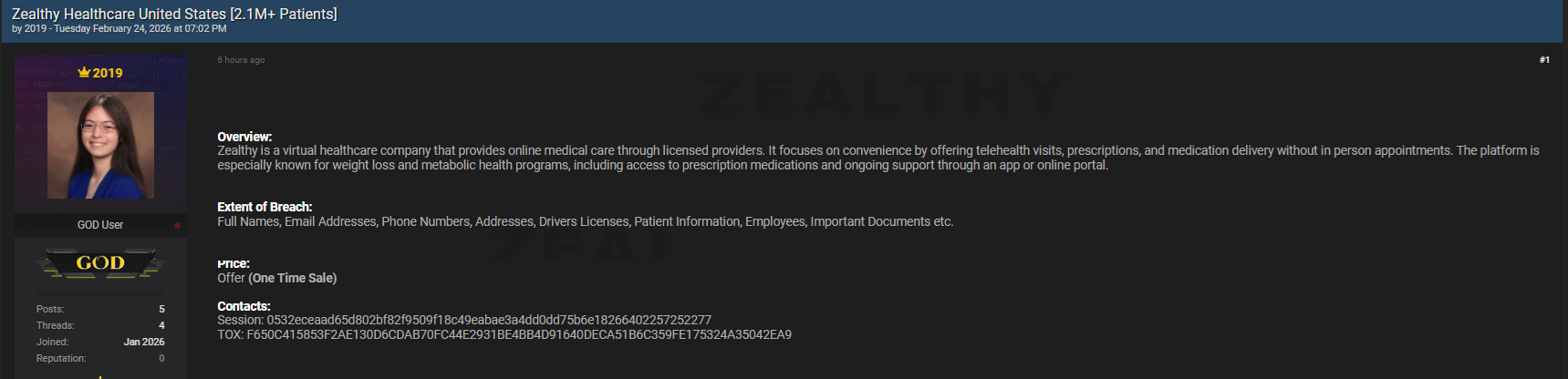
The post claims that the data originates directly from internal systems rather than scraped or aggregated public sources. While no official confirmation has been issued at the time of writing, cybersecurity analysts note that the structure and descriptions match patterns seen in previous healthcare sector leaks. Allegations of this scale typically trigger internal investigations, legal reviews, and regulatory scrutiny within days.
Types of Data Reportedly Compromised
One of the most alarming aspects of the alleged Zealthy Healthcare leak is the breadth of data reportedly included. According to the forum listing, the exposed information may contain:
• Full names and email addresses
• Phone numbers and residential addresses
• Driver’s license details
• Patient-related information
• Employee records
• Internal and important documents
This combination of personally identifiable information (PII) and patient data significantly increases the risk of identity fraud, phishing, and long-term misuse 🔐 Unlike simple email leaks, healthcare-related datasets can be exploited for years, especially when documents and ID numbers are involved.
Timeline and Disclosure Details
Understanding the timeline helps clarify why this alleged Zealthy Healthcare data breach has drawn so much attention. The seller claims the database was published on February 24, 2026, with immediate availability for interested buyers. No free sample was publicly released, which is often done to maintain exclusivity and avoid rapid law enforcement attention. The price was not disclosed publicly, but the listing clearly stated “Offer – One Time Sale,” suggesting negotiations occurred privately 💬
Historically, when healthcare leaks are posted in this manner, confirmation or denial from the affected company typically follows within one to three weeks. Until then, patients and partners are left in a state of uncertainty. This gap between alleged disclosure and official response is where misinformation often spreads, making careful analysis essential.
Why Healthcare Data Breaches Are So Valuable
Why would cybercriminals target a healthcare provider in the first place? The answer is simple and well-documented. Medical and patient data sells for significantly more than standard credentials. A single complete healthcare record can fetch multiple times the value of a credit card number 🧠
In the context of the Zealthy Healthcare leak, the inclusion of documents, licenses, and patient-related information dramatically increases resale potential. Such data can be used for insurance fraud, synthetic identity creation, and highly targeted social engineering campaigns. According to cybersecurity experts cited by the U.S. Department of Health and Human Services, healthcare remains one of the most attacked sectors due to outdated systems and high data value.
For further reading on healthcare breach reporting standards, you can consult the official HHS breach portal at hhs.gov.
Who Could Be Impacted by This Alleged Breach
If the claims are accurate, the Zealthy Healthcare data breach could affect multiple groups simultaneously. Patients are the most obvious victims, but employees and business partners may also face exposure. Individuals whose driver’s licenses and addresses were included could experience identity theft months or even years after the initial leak 📉
Here’s a clear answer to a common question:
Does an alleged breach automatically mean your data is being misused?
No. A breach means data may be exposed, but misuse depends on whether cybercriminals actually purchase, redistribute, or exploit the information. However, the risk remains real and proactive monitoring is strongly advised.
Practical Checklist: What Affected Individuals Should Do
If you believe you may be impacted by the alleged Zealthy Healthcare leak, consider the following practical steps:
• Monitor credit reports for unusual activity
• Enable fraud alerts with major credit bureaus
• Be cautious of unsolicited emails or phone calls
• Avoid clicking links claiming to reference medical updates
• Change passwords associated with healthcare portals
This checklist approach helps reduce potential damage while awaiting official confirmation or guidance 🛡️ Staying informed through trusted cybersecurity resources is also essential. Dark web monitoring platforms regularly publish updates on major data leaks and underground market activity.
The Role of Underground Forums in Data Leak Exposure
Platforms like breachforums.as play a central role in exposing alleged incidents such as the Zealthy Healthcare data breach. While these forums operate outside the law, they often serve as early indicators of large-scale compromises. Security researchers and journalists monitor these spaces to verify claims and assess potential impact.
Interestingly, not all listings turn out to be legitimate. Some are recycled, exaggerated, or entirely fabricated. However, the level of detail provided in this case has led many analysts to treat the claims seriously. Tracking marketplaces and leak forums has become a standard part of modern threat intelligence operations 📊 For ongoing analysis, check out dark web monitoring platforms that offers detailed breakdowns of similar incidents.
Regulatory and Legal Implications
If confirmed, the Zealthy Healthcare data breach could trigger significant regulatory consequences. U.S. healthcare organizations are subject to strict data protection requirements, including HIPAA. Failure to safeguard patient information can result in heavy fines, mandatory audits, and reputational damage.
Legal experts note that even alleged breaches can lead to class-action lawsuits if negligence is demonstrated. This is why transparency and rapid response are critical in healthcare cybersecurity incidents. As one industry analyst stated, “In healthcare, trust is currency. Once lost, it is extremely difficult to regain.” ⚖️
How This Incident Fits Broader Breach Trends
The alleged Zealthy Healthcare leak is not an isolated case. Over the past five years, healthcare data breach incidents have increased steadily, both in frequency and scale. Digital health platforms, telemedicine providers, and wellness startups have become attractive targets due to rapid growth and uneven security maturity.
From an analytical standpoint, this case aligns with trends involving centralized databases, third-party integrations, and credential reuse. Monitoring platforms such as https://darknetsearch.com/ help contextualize these events within the broader cybercrime ecosystem.
Conclusion and What to Watch Next
The alleged Zealthy Healthcare data breach serves as a stark reminder of how vulnerable sensitive healthcare data remains in 2026. While confirmation is still pending, the reported scale and data types warrant serious attention from patients, professionals, and regulators alike. Staying informed, practicing good digital hygiene, and following trusted breach intelligence sources are the best defenses in uncertain situations 📌
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

