➤Summary
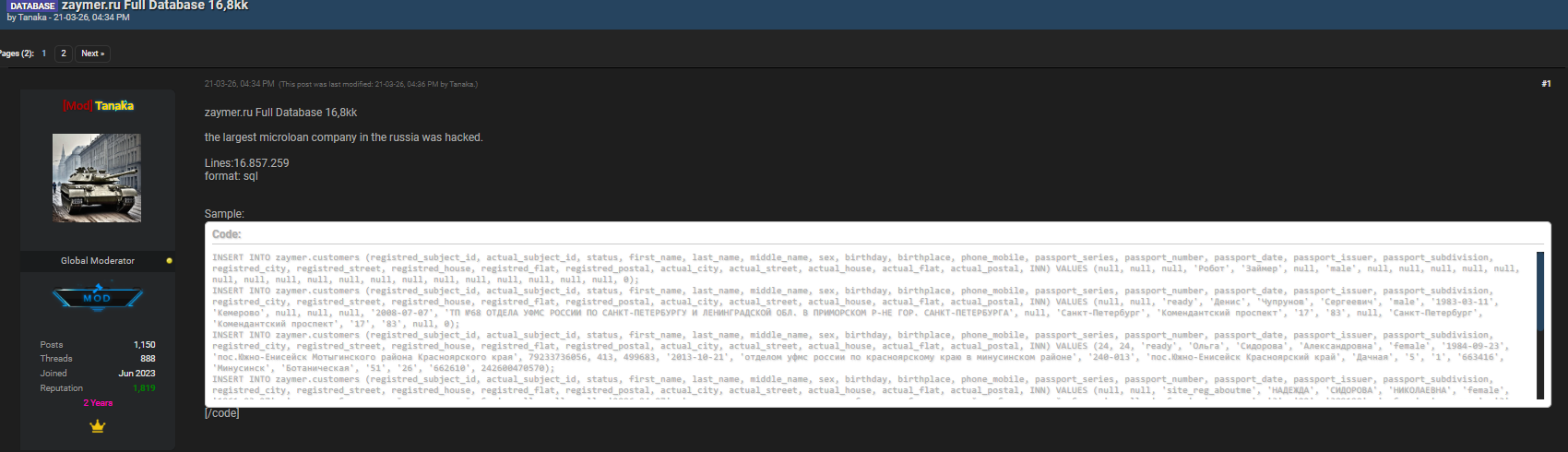
The Zaymer.ru data breach has recently surfaced following claims published on underground cybercrime forums, raising concerns among cybersecurity experts and users alike. On 23 March 2026, a threat actor known as Tanaka allegedly posted database information on the dark web forum Darkforums.su, suggesting unauthorized access to customer records linked to the Russian online lending platform.
The discovery was made during routine monitoring conducted by the Kaduu team, highlighting how proactive intelligence gathering continues to uncover hidden cyber threats before they reach mainstream awareness. While the incident remains classified as alleged, the exposure of structured database entries indicates potential risks involving sensitive personal data. Understanding what happened, what information may be affected, and how individuals should respond is essential in today’s evolving cyber threat landscape. 🔎
What Happened: Timeline of the Alleged Incident
According to available information, the breach discussion appeared publicly inside a dark web forum widely used for trading compromised databases.
Key timeline details:
- Forum: Darkforums.su
- Author: Tanaka
- Publication date: 23 March 2026
- Discovery: Identified by the Kaduu cybersecurity team during routine monitoring activities
The post allegedly contained database-related material referencing customer records from Zaymer.ru systems. Although independent verification is ongoing, the structure of the shared data strongly resembles production database schemas used by financial platforms.
Cybersecurity analysts emphasize that early reporting allows organizations and users to take precautionary measures even before official confirmations are issued. ⚠️
Overview of the Exposed Database Structure
The leaked content reportedly included a database insertion example referencing customer information fields. The exposed structure suggested storage categories typically associated with identity verification systems:
INSERT INTO zaymer.customers
(registred_subject_id, actual_subject_id, status, first_name,
last_name, middle_name, sex, birthday, birthplace, phone_mobile,
passport_series, passport_number, passport_date, passport_issuer,
passport_subdivision, registred_city, registred_street,
registred_house, registred_flat, registred_postal,
actual_city, actual_street, actual_house, actual_flat,
actual_postal, INN)
VALUES (…);
The visible sample used placeholder values such as “Робот Займер,” but the schema itself indicates potential storage of:
- Personal identification data
- Passport information
- Contact details
- Residential addresses
- Tax identification numbers
If authentic, such exposure could pose identity theft risks due to the sensitive nature of financial customer verification records.
Why This Alleged Data Breach Matters
Financial services platforms hold highly valuable information. Unlike basic account leaks, breaches involving identity documents can have long-term consequences.
Potential impacts include:
- Identity fraud attempts
- Loan application abuse
- Social engineering attacks
- Credential stuffing campaigns
- Financial impersonation schemes
A data breach investigation typically examines whether attackers accessed live production systems or outdated backups. Even partial exposure can still create risk when combined with previously leaked datasets.
Cybersecurity researchers often warn that modern cybercrime relies on combining multiple leaks to build complete victim profiles. 🧠
How the Leak Was Discovered by Kaduu Researchers
The Kaduu team identified the forum post through continuous intelligence tracking across underground marketplaces. Their approach relies on Dark web monitoring solutions, which scan hidden forums, marketplaces, and encrypted communities for emerging threats.
This monitoring process enables analysts to detect early warning signs such as:
- Database sale advertisements
- Credential dumps
- Threat actor discussions
- Proof-of-leak samples
Early detection allows organizations to begin containment assessments faster, improving incident response timelines.
Understanding the Role of Dark Web Forums in Cybercrime
Dark web forums function as underground marketplaces where cybercriminals exchange stolen data and hacking tools. Platforms like Darkforums.su often act as distribution hubs where attackers publish “proof” samples to validate claims.
These communities operate on reputation systems similar to legitimate marketplaces. Threat actors build credibility by sharing verified leaks.
A common misconception is that breaches begin on the dark web. In reality, forums are usually where stolen data appears after exploitation has already occurred.
For broader threat intelligence insights, resources such as https://en.wikipedia.org/wiki/Data_breach provide background on how breaches evolve from intrusion to public exposure.
What Information May Be at Risk
Based on the shared schema, potentially compromised data categories may include:
| Data Category | Risk Level | Possible Misuse |
| Names & identity data | High | Identity fraud |
| Passport details | Critical | Financial impersonation |
| Phone numbers | Medium | Phishing attacks |
| Addresses | Medium | Social engineering |
| Tax ID (INN) | High | Fraudulent applications |
| This type of exposure highlights why Data Protection practices remain essential for financial platforms handling regulated personal information. 🔐 |
How Users Can Check If They Are Affected
Many users ask: How can I know if my data was included in the breach?
The answer is straightforward:
You cannot rely solely on official announcements. Instead, monitor unusual account activity and watch for suspicious communications.
Recommended actions:
- Check financial accounts regularly
- Enable multi-factor authentication
- Monitor loan or credit activity
- Avoid clicking unknown links
- Change passwords proactively
Dark web monitoring platforms provides security awareness platforms through exposure indicators and tracking emerging leaks.
These services contribute to faster data breach detection, helping individuals identify risks earlier. 🛡️
Signs Your Data Might Be Misused After a Breach
Watch for these warning indicators:
- Unexpected verification codes
- Loan approvals you didn’t request
- Increased spam or scam calls
- Password reset notifications
- Unknown account registrations
If multiple signs appear simultaneously, immediate action is recommended.
Practical Security Checklist After a Data Breach
Here’s a quick response checklist:
✅ Change passwords across financial accounts
✅ Enable two-factor authentication
✅ Freeze credit reports if available
✅ Monitor SMS and email alerts
✅ Avoid sharing verification codes
✅ Report suspicious activity immediately
Following these steps reduces the chances of successful exploitation after a breach disclosure. 🚨
Expert Perspective on Modern Breach Trends
Cybersecurity analysts increasingly observe that financial platforms are attractive targets due to centralized identity databases.
An industry expert once noted:
“Data is the new currency, and identity data is its most valuable form.”
Attackers prioritize institutions storing verified customer records because such information can bypass fraud detection systems more easily.
Broader Cybersecurity Implications
The alleged Zaymer.ru data breach reflects a wider trend: attackers targeting fintech services experiencing rapid digital expansion.
Key contributing factors include:
- Large centralized databases
- Increasing online lending adoption
- Automated onboarding systems
- Cross-border cybercrime networks
Organizations must continuously strengthen monitoring and incident response frameworks to stay ahead of evolving threats.
For deeper intelligence research and breach monitoring resources, visit https://darknetsearch.com/dark-web-monitoring.
Conclusion: What This Incident Teaches About Cyber Risk
The Zaymer.ru data breach serves as a reminder that cybersecurity threats often emerge silently before becoming public headlines. Whether confirmed or still under investigation, alleged leaks should always be treated seriously because prevention is more effective than recovery.
Users must remain vigilant, organizations must invest in monitoring capabilities, and security awareness should become part of everyday digital behavior. Cyber threats evolve quickly, but informed users and proactive detection strategies dramatically reduce risk exposure. 🌐
Discover much more in our complete guide
Request a demo NOW
*Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

