➤Summary
Zambia data leak allegations surfaced in February 2026 after a forum post on BreachForums claimed that a massive database linked to the Government of Zambia had been compromised. Published on 20 February 2026 by a user known as Spirigatito, the post describes one of the most extensive public-sector exposures in Southern Africa, affecting roughly 15 million individuals and more than 34.1 million records. According to the disclosure, the leaked dataset weighs approximately 500 GB and contains deeply sensitive personal, household, and financial information.
This alleged Government of Zambia data breach has sparked intense discussion among cybersecurity professionals, civil society groups, and Threat Intelligence Analysts, as the scale and granularity of the information raise serious concerns about citizen safety, fraud, and long-term national security implications 😟.
What We Know About the Alleged Government of Zambia Data Breach
The Zambia data leak was reportedly advertised on BreachForums, a notorious underground marketplace for stolen data. The author claims the data originates from social protection and beneficiary management systems, suggesting a breach of centralized government infrastructure. While officials had not publicly confirmed the incident at the time of publication, the consistency of the fields, timestamps, and geographic markers has led many researchers to treat the alleged Government of Zambia data breach as highly credible.
Types of Data Allegedly Exposed
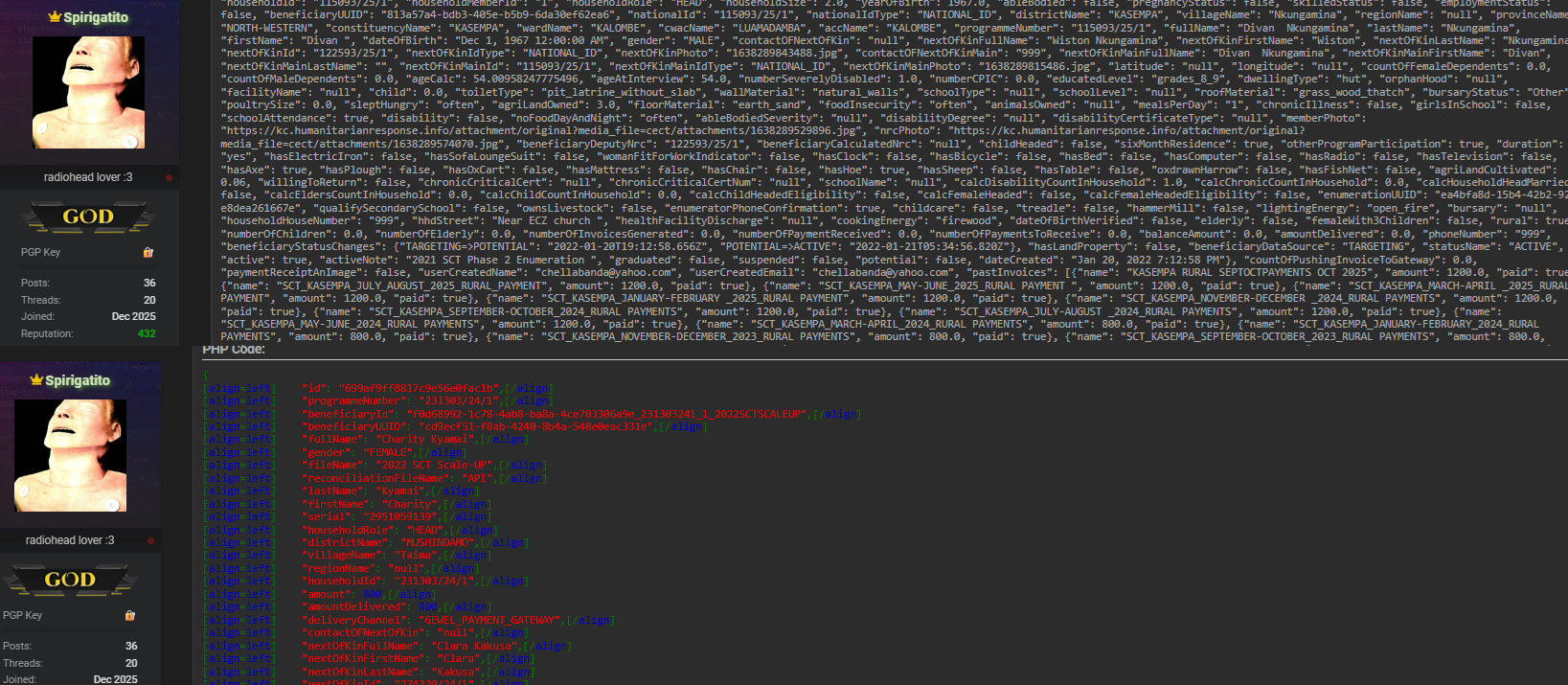
According to the forum description, the Zambia data leak includes a remarkably comprehensive profile of affected individuals:
- Full name, date of birth, gender, national ID, beneficiary ID
- Phone numbers, emails, and full physical addresses down to village and ward level
- Household data including size, roles, number of children and elderly members
- Disability status, education level, dwelling type, and housing materials
- Utility and lifestyle indicators such as toilet type, cooking and lighting energy
- Asset ownership details like beds, bicycles, radios, and TVs
- Agricultural land and livestock ownership
- Programme names, beneficiary status, account names, balances, and payment histories
- GPS latitude and longitude coordinates and validation status
This breadth of information makes the alleged Government of Zambia data breach far more dangerous than typical identity leaks, as it enables profiling at both individual and community levels 📊.
Scale and Impact of the Zambia Data Leak
With 15 million people affected in a country of roughly 20 million, the Zambia data leak potentially touches the majority of the population. The 34.1 million records suggest multiple entries per person, likely spanning years of programme participation and payment cycles. From an impact perspective, this Government of Zambia data breach goes beyond financial fraud. It introduces risks of social engineering, targeted scams, political manipulation, and even physical harm, especially when GPS data and household vulnerability indicators are involved 🧭.
Why This Breach Raises National Security Concerns
One critical question arises: Why is this Zambia data leak more than just another database exposure? The answer lies in context. Large-scale public-sector leaks can be leveraged for nation-state threats, especially when they reveal socioeconomic vulnerabilities and precise locations of millions of citizens. Experts in Geopolitical Intelligence warn that such datasets can be exploited to destabilize trust in public institutions or to influence sensitive regions. Even without confirmation of foreign involvement, the potential use cases elevate this alleged Government of Zambia data breach into a strategic risk category 🛡️.
Cybersecurity Perspective and Expert Insight
A senior analyst quoted by Reuters noted that “when social protection databases are exposed, the damage persists for decades because the data rarely changes.” This observation aligns with how data breach detection teams assess long-term risk. Unlike passwords, attributes such as national ID numbers, family structure, and home location cannot simply be reset. For cybersecurity professionals monitoring the Zambia data leak, this permanence significantly increases the severity rating 🔍.
Practical Checklist for Affected Citizens and Organizations
Practical Tip – What to do after a large-scale government breach:
- Monitor financial accounts and benefit payments for anomalies
- Be cautious of calls or messages referencing specific household details
- Avoid sharing national ID information unless absolutely necessary
- Government agencies should audit access logs and isolate affected systems
- Deploy independent data breach detection and continuous monitoring tools
These steps cannot undo the alleged Government of Zambia data breach, but they can limit secondary exploitation 📋.
The Role of Monitoring and Intelligence
Security teams increasingly rely on coordinated monitoring strategies to identify early signs of misuse. While public confirmation is pending, early indicators from underground chatter show heightened interest in Zambian datasets. This is where Threat Intelligence Analysts play a key role, correlating forum claims with real-world fraud attempts. Integrating open-source monitoring with structured analysis helps institutions respond before damage escalates 🚨.
Where to Learn More About Emerging Breaches
For ongoing coverage of incidents like this Zambia data leak, readers can explore detailed investigations and threat reports in different dark web intelligence platforms. These resources provide context on underground disclosures, actor behavior, and mitigation strategies. For broader cybersecurity reporting, Reuters offers high-authority coverage of global data breaches and public-sector cyber risks.
Conclusion: Why the Zambia Data Leak Matters
The alleged Government of Zambia data breach is a stark reminder that centralized citizen databases are high-value targets with far-reaching consequences. Affecting millions and exposing intimate details of daily life, this Zambia data leak underscores the urgent need for transparency, stronger safeguards, and proactive monitoring. Whether you are a policymaker, security professional, or concerned citizen, staying informed is critical in an era where data exposure can reshape trust overnight 🌍. Discover much more in our complete guide and Request a demo NOW to understand how advanced monitoring can help detect and respond to the next major breach before it’s too late.
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

