➤Summary
The Videnov.BG database breach has emerged as an alleged cyber incident after the Kaduu team identified a large dataset being advertised during routine Dark web monitoring on underground forums. According to the listing, the data originates from Videnov.BG and includes millions of transactional and personal records. While the claims remain unverified at the time of writing, the scale and detail described have raised immediate concerns among security researchers and eCommerce operators alike. This darknetsearch.com article examines the available information, the potential impact on customers and businesses, and the steps organizations should take now. By understanding how an alleged data breach of this magnitude unfolds, decision-makers can better prepare to reduce risk and respond decisively. 🔎
What is known about the alleged Videnov.BG incident
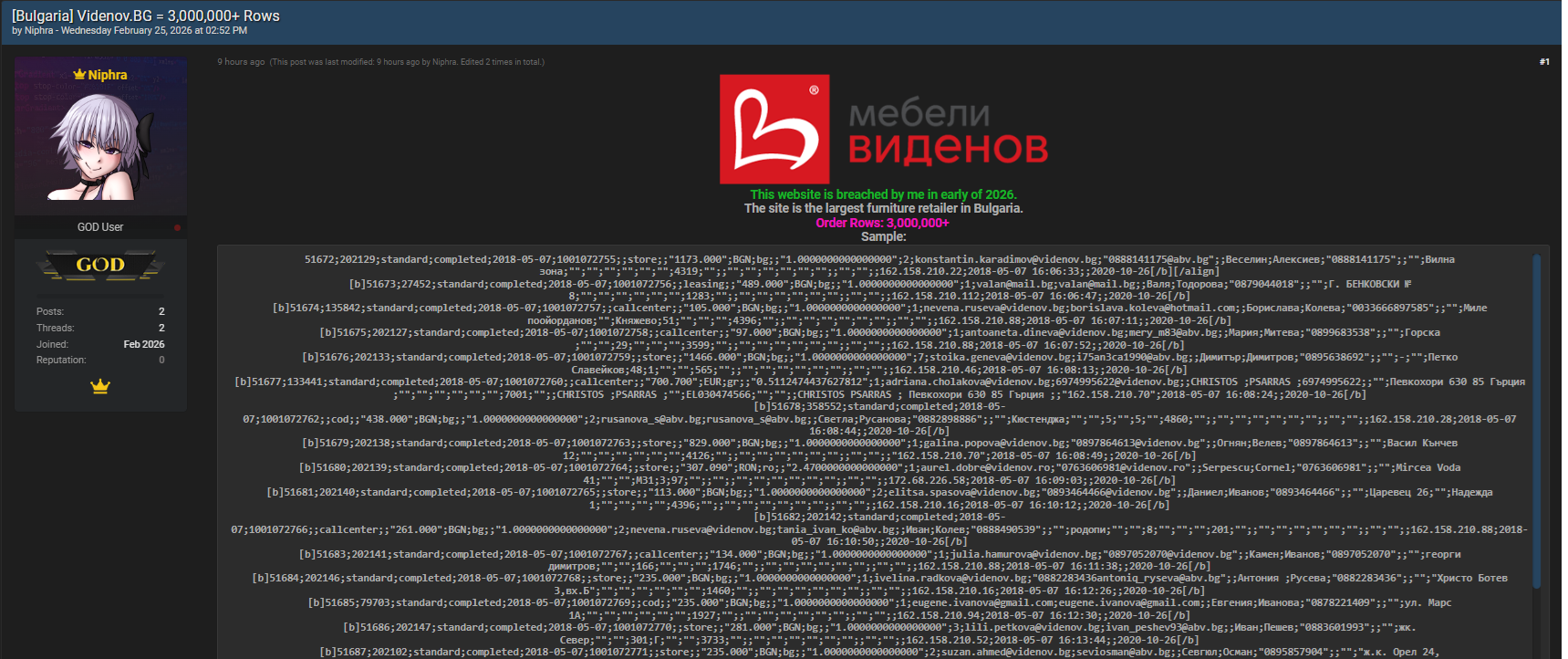
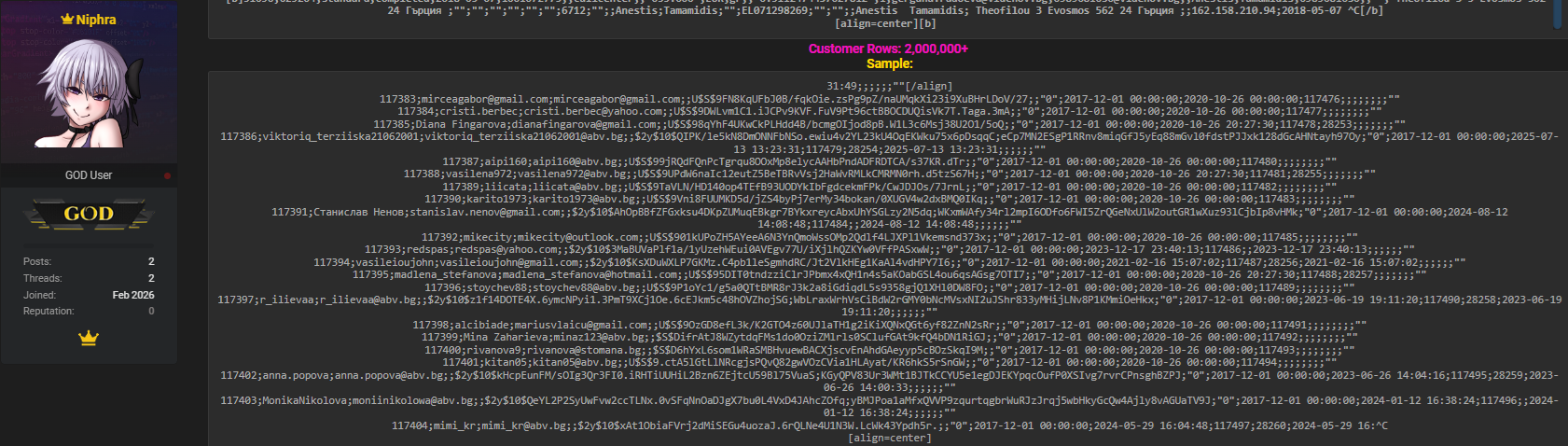
The post discovered by Kaduu attributes the dataset to a compromise of Videnov.BG systems, allegedly offering access to more than three million records for sale. The seller, using the alias “Niphra,” advertised the database on Breachforums.as with a price tag of $3,000 USD. If accurate, the Videnov.BG database breach would rank among the larger retail-related leaks in the region, due to the depth of order and contact information included.
It is important to stress that no official confirmation has been issued by the affected company, and investigations are ongoing. Nevertheless, cybersecurity analysts treat such disclosures as credible signals that warrant immediate scrutiny. ⚠️
Compromised data fields and why they matter
The allegedly exposed database contains a wide range of sensitive fields tied to eCommerce operations. These reportedly include order_id, customer_id, order_type, order_status, order_date, order_number, invoice_number, source, payment_method, total_amount, currency, language, coupon_code, exchange_rate, shipping_method_id, billing_email, contact_email, company, first_name, last_name, phone, fax, multiple address lines, city_id, ip_address, created_at, updated_by, and updated_at. When combined, this information can enable identity correlation, targeted phishing, and account takeover attempts.
In the context of an alleged data breach, such datasets are particularly valuable to threat actors because they allow highly personalized social engineering. 📂
Timeline and discovery on underground forums
The Kaduu team encountered the listing while scanning criminal marketplaces and discussion boards. Their discovery did not stem from customer reports but from proactive intelligence collection focused on early warning signals. This process, often supported by a Dark web solution, aims to identify leaked credentials and databases before they are widely exploited. The seller’s claim of freshness and exclusivity increased attention around the Videnov.BG database breach, prompting further validation efforts. While the dark web often exaggerates, historical patterns show that many similar listings have proven accurate after disclosure. 🕵️♂️
Potential impact on customers and businesses
If the claims are substantiated, affected individuals could face risks ranging from spam and fraud to more serious financial scams. Transaction histories and contact details are frequently reused by criminals to craft believable lures. Businesses connected to the supply chain may also be impacted, as leaked operational data can reveal pricing structures and logistics workflows. This alleged data breach also highlights the broader issue of loyalty account leaks across retail platforms, where repeat customers become prime targets. The Videnov.BG database breach narrative underscores how a single exposure can ripple through an entire ecosystem. 💥
How organizations should respond to alleged breaches
When confronted with reports like this alleged data breach, organizations should follow a clear response framework. First, initiate an internal investigation to verify whether systems were accessed without authorization. Second, rotate credentials and audit access logs for anomalies. Third, prepare transparent communications for users if exposure is confirmed. A practical checklist includes: reviewing database permissions, enforcing multi-factor authentication, scanning for malware, and engaging external incident responders. These steps reduce uncertainty and demonstrate accountability. ✅
One key question everyone asks—and the answer
Is customer payment data exposed in the alleged Videnov.BG incident? Based on the advertised fields, no full card numbers or CVV details are explicitly mentioned; however, payment_method metadata can still be misused for fraud profiling. This distinction matters because it shapes regulatory and notification obligations. 🔐
Broader lessons for eCommerce security
Cases like the Videnov.BG database breach reinforce the importance of continuous monitoring and layered defenses. Retailers should invest in threat intelligence, regular penetration testing, and employee security training. Industry experts, including those cited by reputable outlets such as Krebs on Security , consistently emphasize that early detection shortens breach lifecycles. Integrating insights from https://darknetsearch.com/ into security operations can further enhance visibility into emerging threats, as can periodically reviews of underground chatter on platforms tracked by Darknetsearch.com. 🧠
Conclusion and next steps
Although still alleged, the Videnov.BG database breach serves as a timely reminder that no organization is immune to exposure. Whether you are a business leader or a concerned customer, staying informed and proactive is essential. Continuous assessment, responsible disclosure, and user education remain the cornerstones of resilience in today’s threat landscape, especially as activity on the dark web continues to evolve. To deepen your understanding and strengthen your defenses, explore expert resources on https://darknetsearch.com/ and stay ahead of emerging risks. 🚀
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

