➤Summary
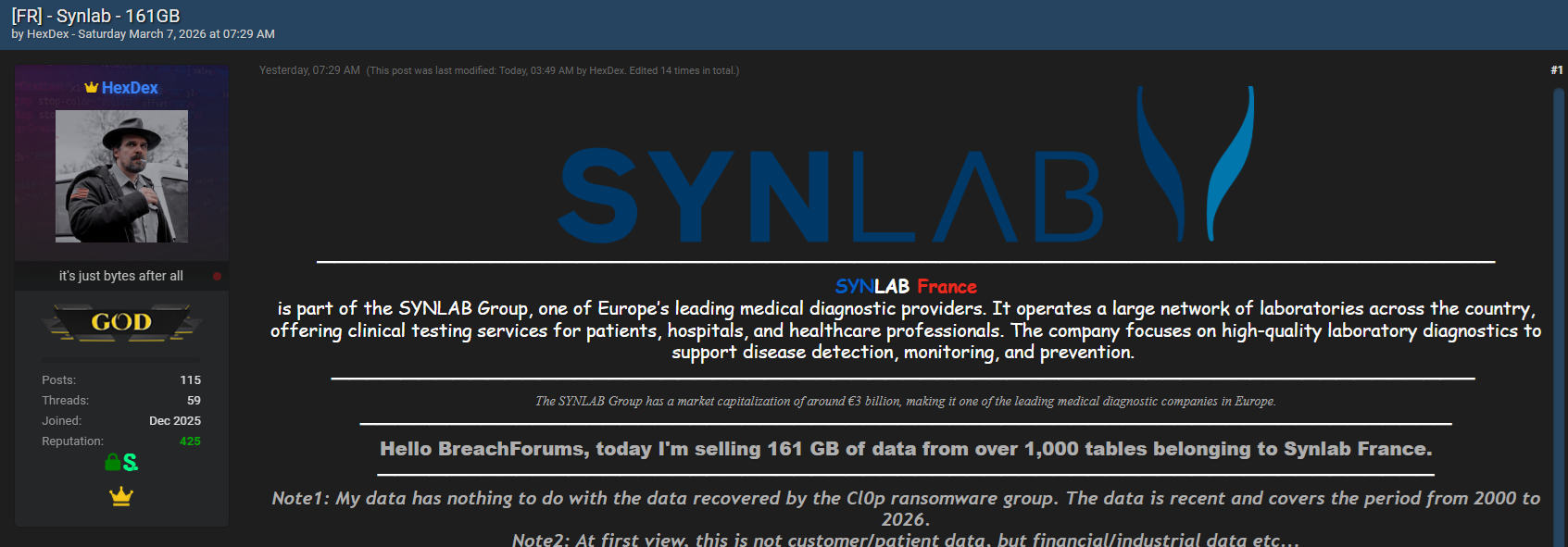
The SYNLAB data leak has recently drawn attention within cybersecurity circles after a threat actor published a post on the underground forum breachforums.as on March 7, 2026. According to the author, known as HexDex, the dataset contains approximately 161 GB of information extracted from more than 1,000 database tables linked to Synlab France.
The discovery was initially flagged by the Kaduu team while conducting routine surveillance across underground communities where leaked corporate databases frequently appear. The post claims the data spans from 2000 to 2026 and includes internal records rather than patient information. While the authenticity of the dataset has not yet been independently verified, the alleged exposure raises concerns about enterprise security practices and the growing risks of large-scale corporate data leaks.
This incident highlights the importance of proactive monitoring, especially for organizations in critical sectors such as healthcare and laboratory diagnostics. As cyber threats continue to evolve, security teams increasingly rely on advanced intelligence methods to identify emerging risks before they escalate. 🔍
Overview of the Alleged SYNLAB Database Leak
According to the forum listing, the dataset was posted by a user named HexDex, who claims to be selling access to a 161 GB database allegedly belonging to Synlab France, a subsidiary of the European medical diagnostics company SYNLAB Group.
The author wrote in the forum thread:
“I’m selling 161 GB of data from over 1,000 tables belonging to Synlab France.”
The post also included an additional clarification:
“Note1: My data has nothing to do with the data recovered by the Cl0p ransomware group. The data is recent and covers the period from 2000 to 2026.”
“Note2: At first view, this is not customer/patient data, but financial/industrial data etc…”
If accurate, the dataset may represent a large repository of internal corporate information rather than sensitive medical records. However, corporate operational data can still pose major risks when exposed publicly, especially if it contains authentication credentials or financial details.
The Kaduu team reportedly identified the listing during ongoing monitoring operations designed to detect potential data exposures and underground marketplace activity. Analysts conducting dark web search operations often uncover such leaks before they reach broader criminal marketplaces. 🕵️♂️
What Data Is Allegedly Included in the Leak
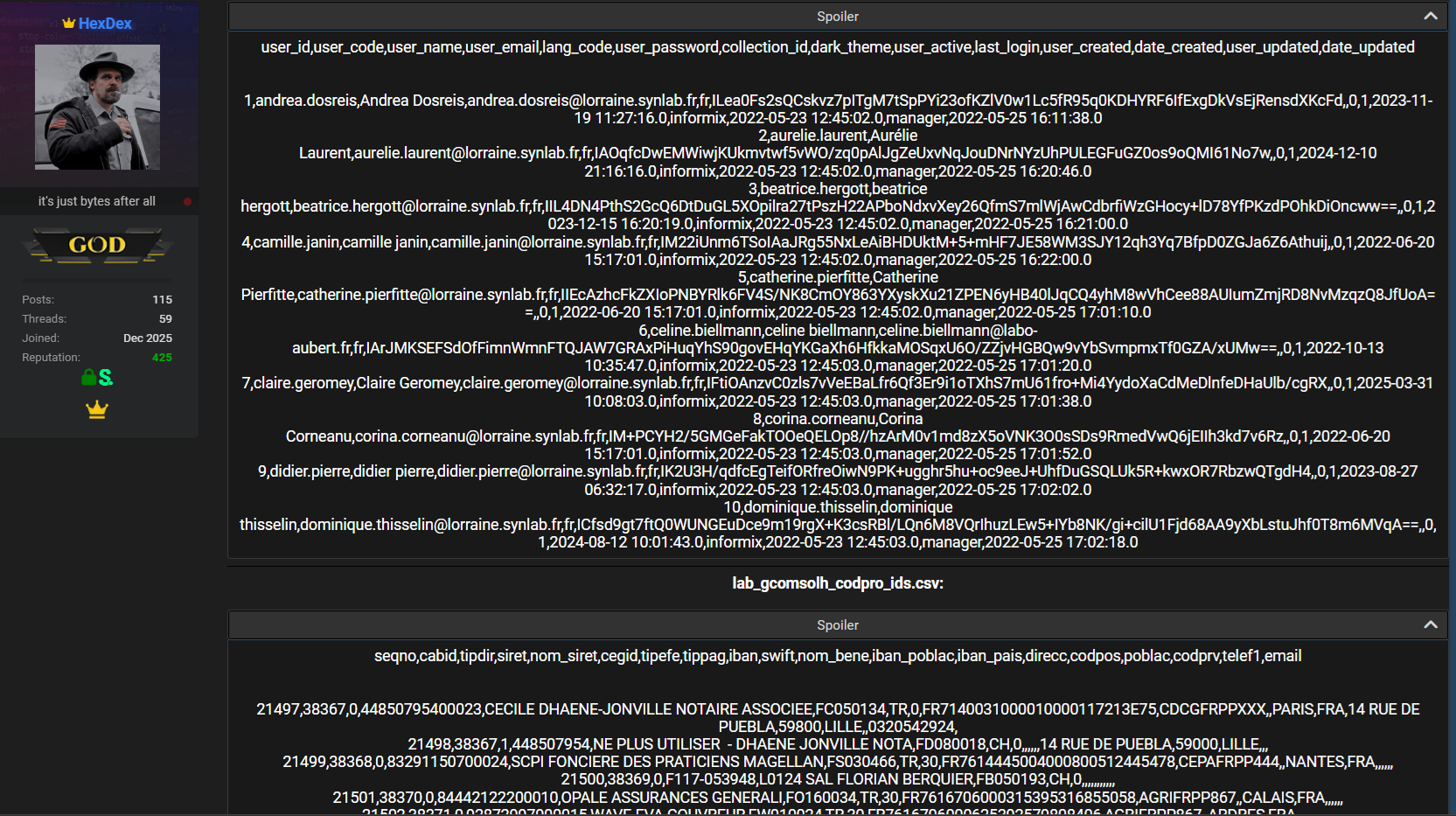
The forum post provides sample database structures indicating the type of records allegedly contained in the dataset. While the full database has not been publicly released, the shared schema suggests multiple categories of corporate data.
The first dataset appears to include user account and system configuration records.
| Field Name | Description |
| user_id | Internal user identifier |
| user_code | System code for user |
| user_name | Username |
| user_email | Email address |
| lang_code | Language preference |
| user_password | Password field |
| collection_id | System reference identifier |
| dark_theme | Interface configuration |
| user_active | Account activity status |
| last_login | Last login timestamp |
| user_created | Account creation reference |
| date_created | Creation date |
| user_updated | Last update reference |
| date_updated | Update date |
A second structure in the dataset appears to contain financial or operational information linked to corporate transactions or vendor details.
| Field Name | Description |
| seqno | Sequence identifier |
| cabid | Internal record ID |
| tipdir | Directory type |
| siret | French company identifier |
| nom_siret | Registered company name |
| cegid | Financial system reference |
| tipefe | Financial classification |
| tippag | Payment category |
| iban | Bank account number |
| swift | Bank identifier code |
| nom_bene | Beneficiary name |
| iban_poblac | Bank location |
| iban_pais | Country |
| direcc | Address |
| codpos | Postal code |
| poblac | City |
| codprv | Province code |
| telef1 | Phone number |
| Contact email |
The presence of financial records, internal identifiers, and authentication credentials could still present serious cybersecurity risks.
Why the Alleged SYNLAB Data Leak Matters
The potential SYNLAB data leak highlights a broader issue affecting many large organizations: the exposure of internal enterprise systems.
Corporate datasets often include sensitive operational information that can be valuable to cybercriminals. When such records appear on underground forums, they may be used for activities such as:
• Financial fraud
• Corporate espionage
• Targeted phishing attacks
• Credential reuse attacks
• Supply chain compromise attempts
Even internal data without customer information can provide attackers with insights into how an organization operates. This type of intelligence can help cybercriminals plan more sophisticated attacks.
The incident also reflects the growing importance of strong Cybersecurity regulations, particularly in sectors that handle critical data and financial infrastructure. 📊
Detection of the Database on Underground Forums
The Kaduu team reportedly identified the dataset during ongoing monitoring of cybercrime forums and data trading communities. Security researchers frequently track these platforms to identify potential threats to organizations and institutions.
These monitoring activities help detect leaks at an early stage, sometimes before the affected organization is even aware of the exposure.
Organizations that implement proactive monitoring strategies are better positioned to respond quickly when suspicious activity appears online.
Several cybersecurity research platforms provide tools and intelligence resources that help analysts monitor underground environments. For example:
darknetsearch.com provides insights into emerging threats and leaked data trends.
Security teams also rely on advanced dark web monitoring solutions to automatically track mentions of company names, domains, or leaked credentials across thousands of sources. 🔎
Is the Leak Connected to Previous Attacks?
One key element of the forum post is the author’s claim that the dataset is not related to the Cl0p ransomware group.
Cl0p has previously targeted multiple organizations through large-scale supply chain attacks. By explicitly distancing the dataset from that group, the seller suggests the information may originate from a different compromise or internal source.
However, it is important to note that claims made by threat actors on underground forums are not always accurate. Security researchers must analyze the dataset carefully before confirming its origin.
In many cases, databases sold online turn out to be compilations of older leaks or partially fabricated records.
Experts from organizations like the European Union Agency for Cybersecurity (ENISA) emphasize the importance of verifying the source and authenticity of leaked datasets before drawing conclusions about a breach.
The Growing Risk of Enterprise Data Exposure
Large corporate datasets appearing online have become increasingly common over the past decade. Several factors contribute to this trend:
• Complex cloud infrastructures
• Expanding digital supply chains
• Insider threats
• Misconfigured databases
• Vulnerabilities in enterprise applications
When attackers gain access to internal systems, they often exfiltrate large amounts of data before detection. These datasets are later sold or shared on underground marketplaces.
The healthcare and diagnostics sector is particularly attractive to cybercriminals due to the volume of sensitive data processed by laboratories and healthcare providers. As a result, healthcare data breach detection has become a major focus for cybersecurity teams working in medical organizations. 🧠
Practical Checklist for Organizations
To reduce the risk of large-scale data exposures, companies should adopt a proactive cybersecurity strategy.
Here is a simple checklist that organizations can implement today:
✔ Monitor underground forums for potential data leaks
✔ Implement strong password hashing and authentication policies
✔ Limit access to sensitive databases
✔ Conduct regular vulnerability assessments
✔ Encrypt financial and operational records
✔ Establish an incident response plan
✔ Train employees on phishing awareness
Proactive monitoring and strong internal security controls are critical for preventing corporate datasets from being exposed online.
What Should Companies Do If Their Data Appears Online?
Organizations that discover their data on underground forums should act quickly.
The first steps typically include:
- Verifying the authenticity of the dataset
- Identifying the systems involved
- Containing any ongoing breach activity
- Notifying relevant authorities if required
- Informing affected partners or customers
Rapid response can significantly reduce the impact of a potential breach and help organizations regain control of their systems.
The Importance of Threat Intelligence
Threat intelligence plays a crucial role in modern cybersecurity operations. By collecting and analyzing data from underground communities, security teams can identify emerging threats before they cause widespread damage.
Resources such as:
https://darknetsearch.com/
help researchers track leaked databases, cybercrime discussions, and emerging attack techniques.
Continuous monitoring enables organizations to detect risks earlier and strengthen their defenses against sophisticated cyber threats. 🌐
Conclusion
The alleged SYNLAB data leak posted on breachforums.as raises important questions about the security of large corporate databases. With claims of 161 GB of information from more than 1,000 tables, the dataset could contain significant operational and financial records if confirmed authentic.
Although the seller states that the data does not include patient information and is unrelated to previous ransomware incidents, the exposure of internal enterprise records still represents a serious cybersecurity concern.
The discovery by the Kaduu team demonstrates how continuous monitoring of underground communities can help identify emerging threats before they escalate into larger incidents. 🚨
Organizations that invest in proactive monitoring, strong security frameworks, and rapid response strategies are better equipped to manage the growing risks of data exposure in today’s digital environment.
If you want to learn how advanced monitoring platforms help detect emerging threats, explore intelligence resources and cybersecurity guides available online.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

