➤Summary
A smishing campaign recently shook the Philippines after thousands of motorists reportedly received alarming SMS messages claiming unpaid traffic violations issued by the Land Transportation Office. According to reports shared by the Visor Community on Facebook, the messages looked official and urgent, pushing recipients to immediately settle fines through suspicious links. Many Filipinos, fearing penalties and license suspension, paid without verifying the source. This smishing campaign demonstrates how cybercriminals exploit authority and urgency to manipulate victims, especially in mobile-first countries like the Philippines. 📱⚠️ The incident highlights a growing wave of SMS-based fraud that blends social engineering with digital deception, leaving financial and emotional damage in its wake.
What Is a Smishing Campaign and Why Is It Effective?
A smishing campaign is a form of phishing conducted via SMS, designed to trick recipients into clicking malicious links or sharing sensitive information. Unlike email phishing, smishing leverages the immediacy of text messages and the trust people place in mobile alerts. Cybercriminals craft messages that appear to come from legitimate institutions, such as banks or government agencies, and often include deadlines or threats to provoke quick action. In the LTO fraud alert scam, the attackers used official-sounding language and realistic reference numbers to boost credibility. The effectiveness lies in timing and fear: when a message warns of legal trouble, many people respond instinctively rather than rationally. 😟📩
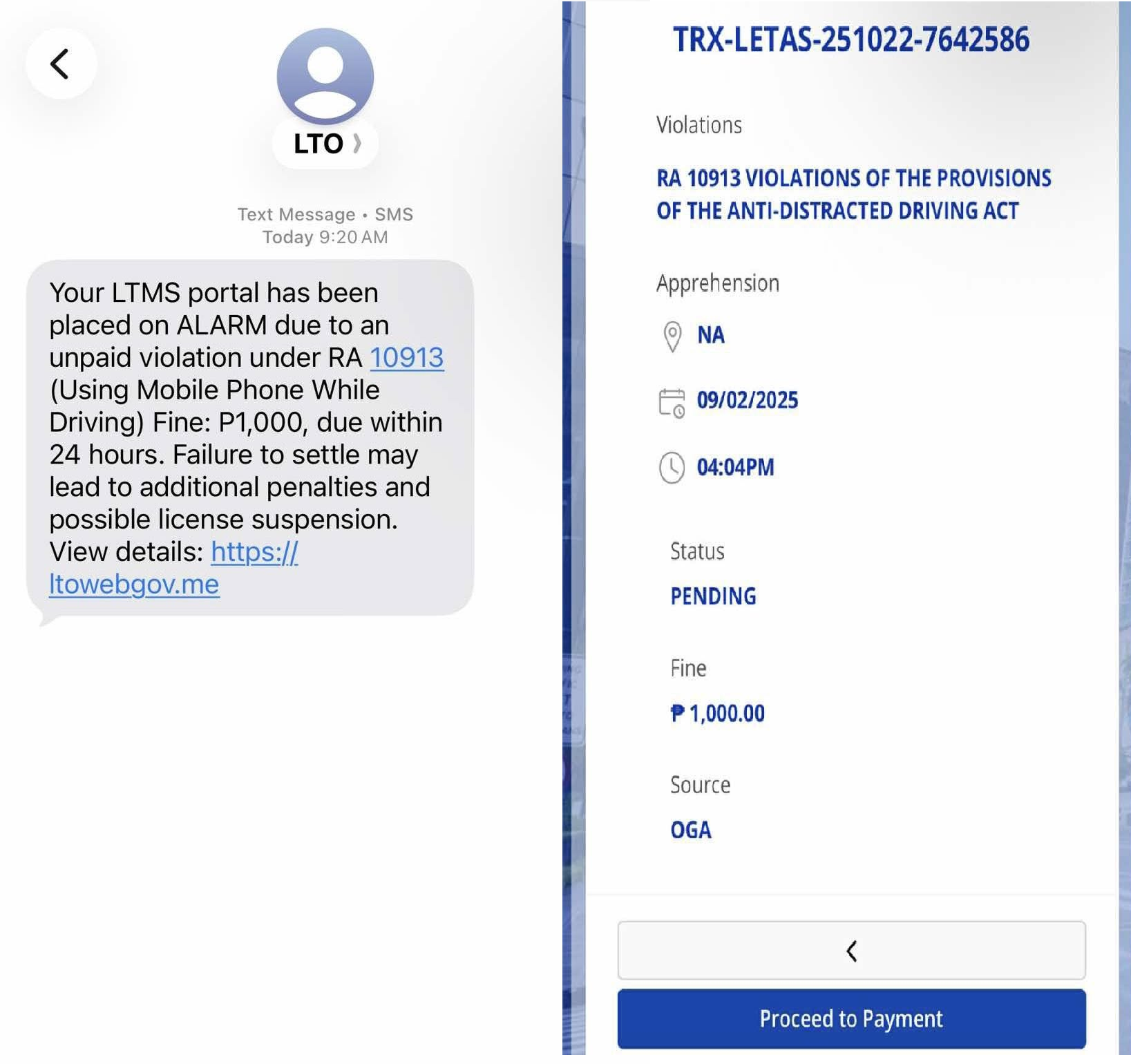
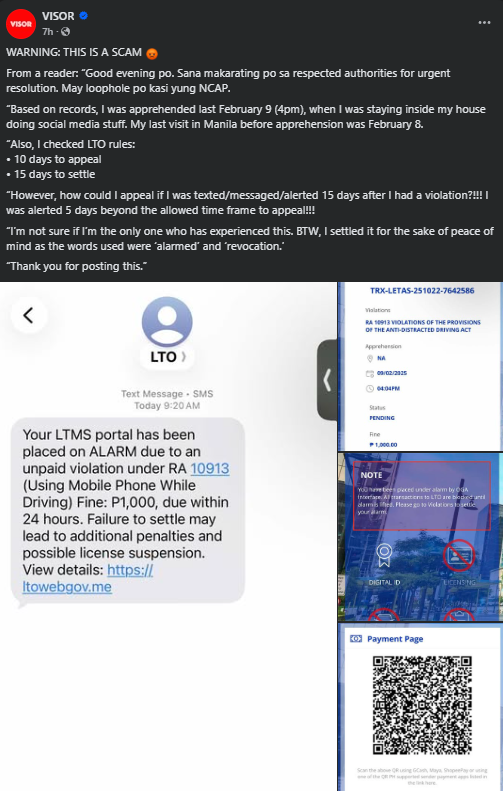
Inside the LTO Fraud Alert Scam That Fooled Thousands
The fraudulent messages claimed that recipients had committed traffic violations and needed to pay fines immediately to avoid penalties. Links embedded in the SMS redirected users to fake payment portals mimicking government pages. This smishing campaign reportedly succeeded because it coincided with heightened public awareness of traffic enforcement. Victims who entered their payment details unknowingly handed over sensitive financial information.
According to Visor Community discussions, some motorists later discovered unauthorized transactions or data misuse. The scam spread rapidly, showing how a single smishing campaign can scale nationwide within hours when combined with automated messaging tools. 💸🚗
The Psychological Triggers Used by Cybercriminals
Why did so many people fall for the trap? The answer lies in psychology. Cybercriminals rely on fear, authority, and urgency. By impersonating the LTO, they exploited institutional trust. By setting short payment deadlines, they limited the time victims had to think or verify.
This smishing campaign also preyed on social proof, as recipients saw others online discussing similar alerts, which made the scam seem legitimate. Understanding these triggers is essential to building resistance against future attacks. 🧠🔐
Real Impact on Filipino Motorists and Digital Trust
The financial losses from this smishing campaign are only part of the damage. Victims reported stress, embarrassment, and declining trust in legitimate digital services.
Some now hesitate to open real government notifications, potentially missing important updates. This erosion of trust affects not only individuals but also public institutions striving to digitize services. When scams masquerade as official communications, the entire digital ecosystem suffers. 🇵🇭💔
How Authorities and Platforms Responded
Following the spread of the scam, the LTO issued public advisories clarifying that it does not send payment links via SMS. Cybersecurity advocates urged the public to report suspicious messages and avoid clicking unknown links. Social media platforms helped amplify warnings, but experts agree that reactive responses are not enough. Proactive measures such as Domain monitoring, typosquatting, and spoofing prevention must be part of a broader defense strategy to stop fake sites before they go live. 🛡️📢
Practical Checklist: How to Spot and Avoid Smishing Attacks
Here is a simple checklist to protect yourself from the next smishing campaign:
• Check the sender’s number and look for irregularities
• Never click links in unsolicited messages claiming urgency
• Verify claims through official websites or hotlines
• Watch for spelling errors or generic greetings
• Use mobile security tools that flag malicious URLs
• Report scams to authorities and your telecom provider
This checklist can significantly reduce your risk and empower you to respond calmly rather than react emotionally. ✅📋
One Common Question Answered Clearly
Question: Should you ever pay traffic fines through links sent by SMS?
Answer: No. Legitimate government agencies do not request payments via random SMS links. Always access official portals by typing the address yourself or using verified apps.
Learning from the Incident: What Comes Next?
This smishing campaign serves as a wake-up call for individuals, institutions, and businesses. As mobile payments and digital services expand, attackers will continue refining their tactics. Continuous education, real-time threat intelligence, and collaboration between public and private sectors are critical. Resources like Spoofguard.io help track emerging fraud trends, while insights from cybercrime analysis and threat research can strengthen preparedness. For broader guidance on staying safe online, Google offers comprehensive security advice at Google Safety. 🌐🔍
Conclusion: Stay Alert, Stay Informed
The LTO fraud alert scam proves that a well-crafted smishing campaign can deceive even cautious individuals. Awareness is your strongest defense. By recognizing red flags, verifying sources, and staying informed through trusted platforms, you can protect yourself and others from falling victim. Digital safety is a shared responsibility, and every informed user weakens the power of cybercriminals. 🚨💡 Discover much more in our complete guide and take control of your online security today. Request a demo NOW to see how proactive monitoring can safeguard your digital presence.
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

