➤Summary
The Penninghen data leak has surfaced as a significant cybersecurity concern after an alleged database and source code exposure appeared on a dark web forum in March 2026. According to threat intelligence monitoring, a user known as Spirigatito published claims on Breachforums.as offering access to sensitive institutional records linked to Penninghen.fr, a well-known French art and design school. The discovery was reportedly made by the Kaduu team during routine surveillance of underground cybercrime marketplaces, where stolen datasets are frequently advertised. Early descriptions suggest a large-scale compromise involving student records, administrative documents, internal communications, and even the institution’s complete software source code. While independent verification is ongoing, cybersecurity analysts warn that the scope described could represent one of the most complex education-sector exposures seen recently. 🔎
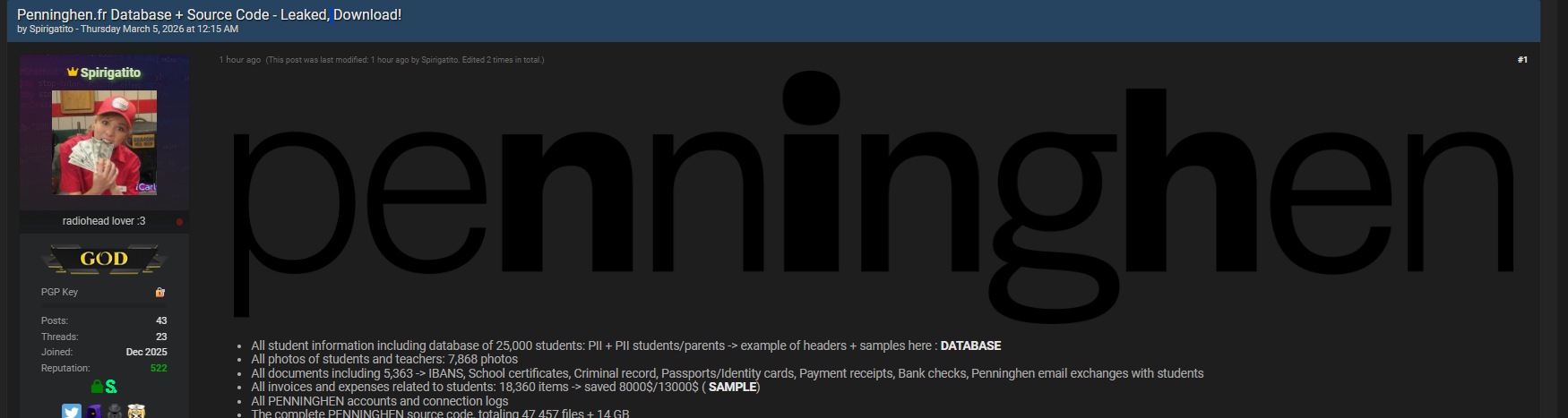
Overview of the Alleged Breach Listing
According to the forum publication dated 05 March 2026, the attacker claims to possess multiple categories of internal assets belonging to Penninghen. The listing includes references to databases, media archives, financial files, and system-level materials.
Key details from the listing:
- Forum: Breachforums.as
- Author: Spirigatito
- Publication date: 05 March 2026
- Discovery: Kaduu team via dark web monitoring
Threat analysts monitoring marketplaces such as those discussed in identified the post during routine scanning activities designed to detect newly leaked institutional datasets. Such monitoring often provides early warnings before broader cybercriminal distribution occurs. 🛡️
Scope of Compromised Data
The alleged Penninghen data leak appears unusually extensive, combining personal information, administrative documents, and proprietary technology assets. Below is a structured breakdown suitable for quick analysis.
| Category | Alleged Content | Volume |
| Student Database | PII for students & parents | 25,000 records |
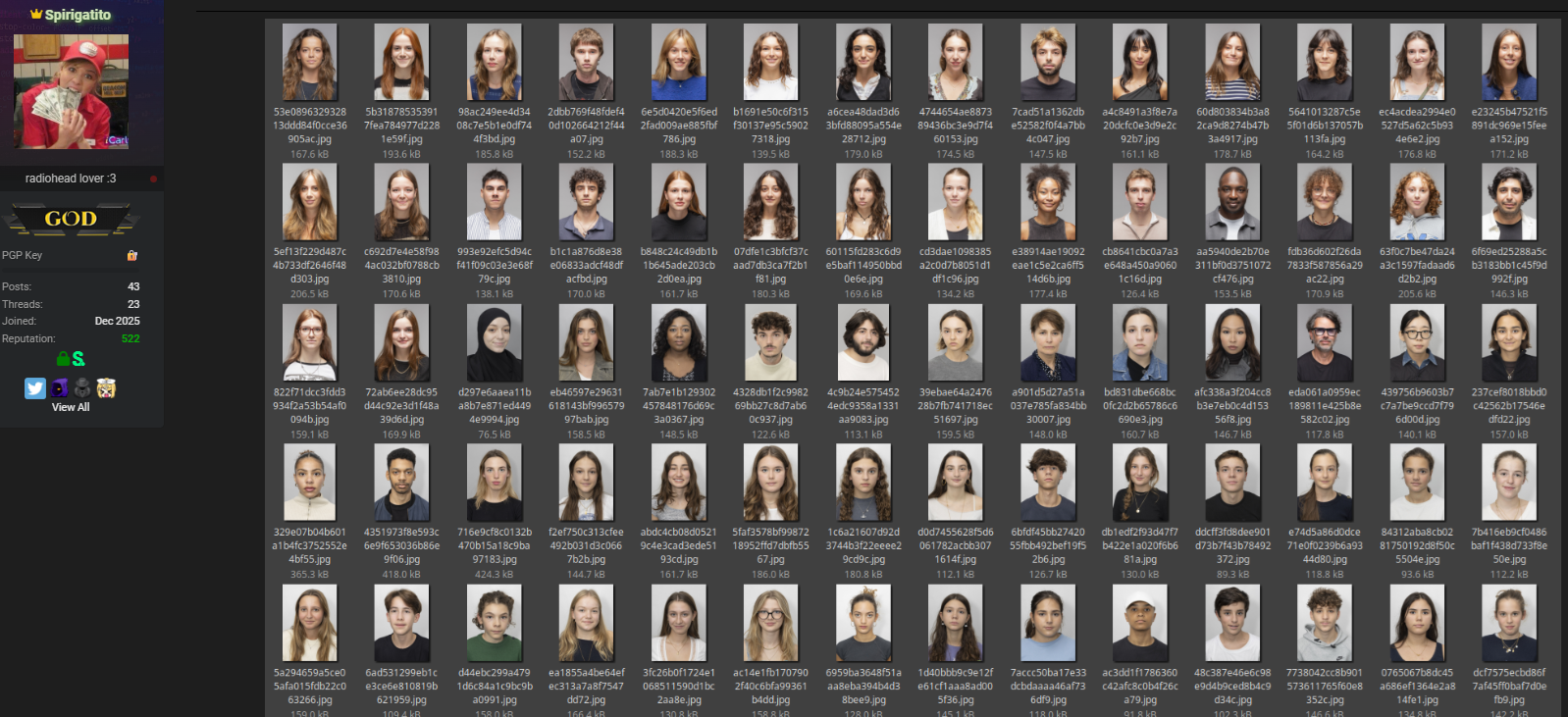
| Photos | Students & teachers | 7,868 images |
| Documents | Passports, certificates, IBANs | 5,363 files |
| Financial Records | Invoices & expenses | 18,360 items |
| Accounts | Login data & connection logs | Full access |
| Source Code | Entire platform | 47,457 files (14GB) |
Student and Parent Information
The dataset reportedly includes personally identifiable information (PII) covering both students and their parents. Exposure of combined academic and family records significantly increases identity theft risks.
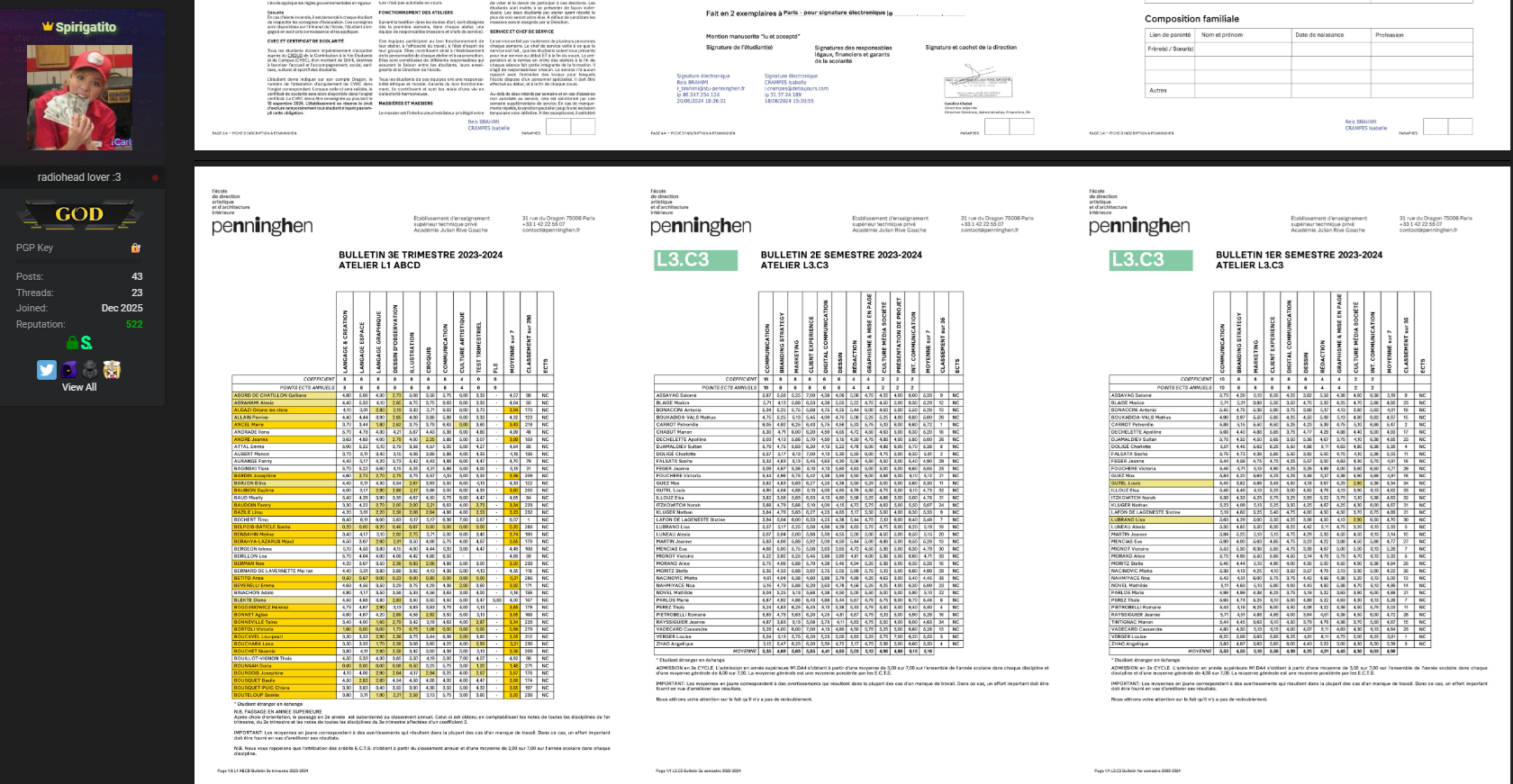
Documents and Identity Files
Leaked materials allegedly contain:
- Passports and identity cards
- Criminal record certificates
- School documentation
- Payment receipts and bank checks
- Email exchanges between students and administration
Such documentation creates long-term privacy risks because identity documents remain valid for years.
Institutional Source Code
One of the most critical elements mentioned is the complete PENNINGHEN source code, totaling over 47,000 files. Source code exposure can allow attackers to analyze system architecture and identify vulnerabilities that were previously unknown. 💻
Why Source Code Leaks Are Especially Dangerous
A database breach is serious, but a source code leak changes the threat landscape entirely. Attackers gaining access to application logic may discover authentication flaws, hidden API endpoints, or insecure integrations.
Potential consequences include:
- Creation of targeted exploits
- Persistent unauthorized access attempts
- Reverse engineering of internal systems
- Increased phishing precision
Cybersecurity experts often describe source code leaks as “blueprints” for attackers.
This makes the alleged Penninghen database breach particularly noteworthy within the education cybersecurity landscape.
How the Leak Was Discovered
The Kaduu team reportedly uncovered the listing during routine dark web monitoring activities. Analysts continuously scan underground forums using automated crawlers combined with manual verification.
Typical monitoring workflow includes:
- Detection of new listings mentioning organizations
- Collection of sample datasets
- Structural comparison with known systems
- Risk evaluation and alert generation
Resources such as explain how early discovery enables institutions to prepare mitigation strategies even before data spreads widely. 🌐
Potential Risks for Students and Staff
If validated, the alleged Penninghen data leak could expose affected individuals to multiple threat scenarios.
Primary risks include:
- Identity fraud using passport copies
- Financial scams targeting IBAN holders
- Social engineering using internal emails
- Academic impersonation attempts
- Credential reuse attacks
Because both communication records and identity documents were allegedly included, attackers may craft highly convincing phishing messages.
Question: Why are education-sector breaches attractive to cybercriminals?
Answer: Educational institutions store long-term identity records, financial details, and communication histories, creating rich datasets that enable fraud and impersonation campaigns.
The Role of Dark Web Forums in Data Distribution
Cybercrime forums act as marketplaces where hackers build reputation by releasing or selling stolen datasets. Listings often include proof samples, file counts, or screenshots to attract buyers.
Investigations covered by show that leaks may evolve through stages:
- Initial advertisement
- Private sale or sharing
- Public redistribution
- Scam exploitation phase
Even unverified leaks can trigger malicious campaigns once attackers reference them publicly. 🧠
Legal and Compliance Implications
Educational organizations operating within Europe must comply with strict privacy regulations. If confirmed, the alleged Penninghen database breach could fall under GDPR notification and investigation frameworks due to the exposure of sensitive personal and financial data.
Possible institutional obligations include:
- Notifying affected individuals
- Conducting forensic audits
- Reporting to regulatory authorities
- Implementing corrective cybersecurity measures
Compliance failures may result in reputational damage alongside regulatory penalties. ⚖️
Practical Checklist for Affected Individuals
Individuals connected to Penninghen should consider proactive security measures.
Protection Checklist
✅ Change passwords linked to school accounts
✅ Monitor bank accounts for unusual activity
✅ Enable multi-factor authentication
✅ Watch for emails referencing invoices or documents
✅ Avoid downloading unexpected attachments
Practical Tip: Attackers often wait weeks before exploiting leaked information, so continued vigilance is essential. 🔐
Indicators Institutions Should Monitor
Organizations assessing risk exposure should look for:
- Increased login attempts from unknown locations
- Unusual API traffic patterns
- Phishing emails referencing internal documents
- Attempts to access archived student portals
Monitoring these signals helps detect exploitation attempts early and reduces operational disruption.
Broader Cybersecurity Lessons
The alleged Penninghen data leak highlights recurring vulnerabilities affecting educational institutions worldwide:
- Centralized storage of identity documents
- Limited segmentation between systems
- Insufficient monitoring of access logs
- Underestimated value of academic datasets
Modern cybersecurity increasingly emphasizes continuous monitoring, zero-trust architecture, and encryption of sensitive archives.
Related LSI concepts connected to this incident include cybersecurity incident response, data exposure analysis, institutional breach investigation, identity protection strategies, cyber threat intelligence, database security practices, and digital privacy risk management.
What Happens Next?
Verification efforts typically involve analyzing database structure consistency, metadata authenticity, and file integrity samples. Investigators may compare leaked records with publicly known formats to determine legitimacy.
Even if partially accurate, exposure claims alone can create secondary risks through impersonation scams. Awareness campaigns therefore become critical during early reporting stages. 📢
Conclusion: Awareness and Preparedness Matter
The alleged Penninghen data leak demonstrates how educational institutions are increasingly targeted by cybercriminal actors seeking valuable identity and financial information. Whether fully confirmed or not, the scale described underscores the importance of proactive monitoring, rapid incident response, and user awareness. Students, parents, and administrators must remain cautious, verify communications carefully, and adopt stronger digital hygiene practices to reduce risks associated with modern cyber threats.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

