➤Summary
Odido data breach allegations are circulating after a post appeared on the underground forum BreachForums on 27 February 2026. The claim, attributed to the ShinyHunters group, suggests that sensitive customer and internal corporate data from Odido, a major telecom provider in the Netherlands, may have been compromised. ⚠️
According to the forum post, the attackers had previously warned the company on 24 February 2026 before publishing their announcement. The Kaduu team reportedly identified the threat during routine monitoring of dark web forums, raising immediate concerns about potential identity theft, financial fraud, and regulatory exposure.
While the situation remains under investigation, the scale and type of exposed information described in the post signal serious cybersecurity implications.
For reference and ongoing updates, see the external coverage by Cybernews.
What We Know About the Alleged Incident
The Odido data breach claim emerged publicly on 27 February 2026. The ShinyHunters Group alleged that they gained access to databases containing customer records and internal documents. The warning reportedly sent to the company three days earlier, on 24 February 2026, indicates an attempted extortion scenario before public disclosure. 💻
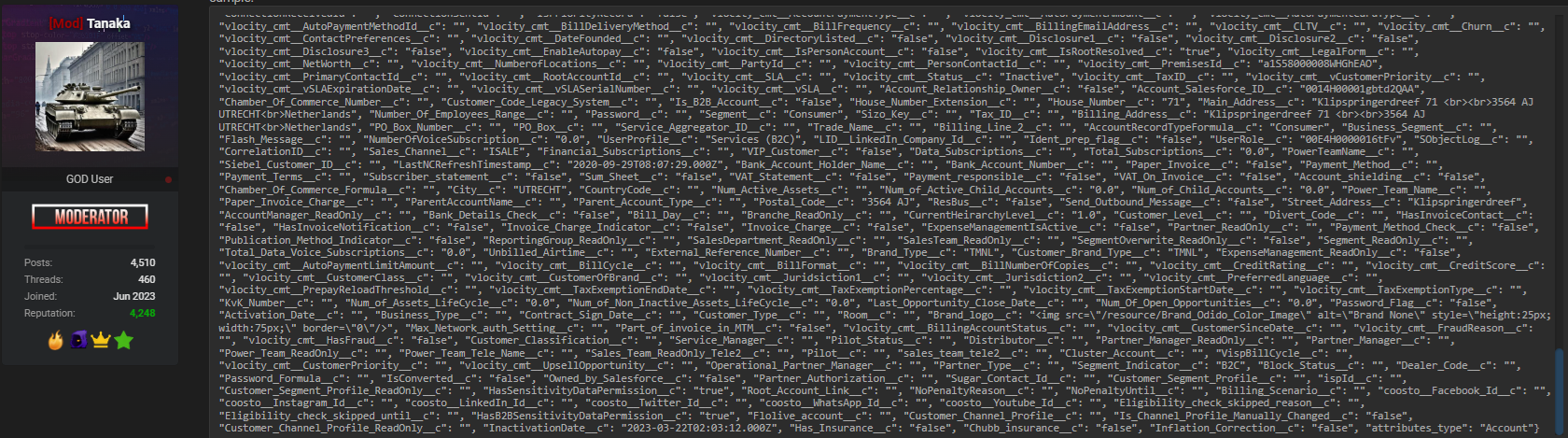
While Odido has not publicly confirmed the full scope at the time of writing, the post claims exposure of:
- Full names
- Physical addresses
- Email addresses
- Phone numbers
- Plaintext passwords
- IBAN numbers
- Passport numbers
- Driver license numbers
- Internal corporate data
If verified, this would represent a severe telecom data leak involving highly sensitive personally identifiable information (PII) and financial data.
Why This Telecom Data Leak Is Especially Concerning
Telecommunications providers store large volumes of customer data due to regulatory and operational requirements. When such data is compromised, the downstream risk multiplies quickly. 📡
The alleged Odido data breach is particularly alarming because it reportedly includes plaintext passwords and banking identifiers such as IBAN numbers. Plaintext password exposure dramatically increases the likelihood of account takeover attacks across multiple platforms due to password reuse.
Additionally, passport and driver license numbers create long-term identity theft risks that cannot be easily mitigated by simply resetting credentials.
Immediate Risks to Customers
If the claims are accurate, affected individuals could face:
- Phishing and social engineering campaigns
- Financial fraud attempts
- SIM-swapping attacks
- Credential stuffing attacks
- Identity theft
These risks are typical consequences of large-scale data exposure incidents in the telecom sector.
Timeline of Events
Here is a simplified overview of the reported timeline:
| Date | Event |
| 24 February 2026 | Hackers allegedly warn Odido |
| 27 February 2026 | Post published on BreachForums |
| Late February 2026 | Discovery by Kaduu team during routine monitoring |
| The three-day gap between warning and public disclosure suggests a pressure tactic commonly used in ransomware and extortion-driven breaches. 🔐 | |
| Attack groups often provide a deadline for payment before leaking data publicly. |
How the Odido Data Breach Was Discovered
The Kaduu team identified the threat during routine monitoring activities across dark web forums. Proactive intelligence gathering plays a key role in modern data breach detection strategies.
Security analysts regularly track underground marketplaces and cybercrime communities to identify early warning signs of potential incidents. In this case, monitoring efforts surfaced the forum listing shortly after publication.
Organizations increasingly rely on a dark web monitoring platform to detect when their brand, employees, or infrastructure appear in criminal discussions. Early detection can significantly reduce response time and minimize damage. 🕵️♂️
For more insights on proactive monitoring, visit dark web monitoring platforms to explore intelligence-driven security strategies.
What Makes ShinyHunters a Notable Threat Actor?
The ShinyHunters Group has been linked to several high-profile data leaks in recent years. They are known for targeting large organizations, extracting databases, and leveraging extortion tactics.
Their operational model typically includes:
- Database exfiltration
- Public proof-of-breach samples
- Negotiation attempts
- Forum publication if demands are unmet
Because of this history, security professionals treat such claims seriously, even before formal confirmation.
Regulatory and Compliance Implications
If confirmed, the Odido data breach could trigger investigations under European data protection laws, including GDPR. Organizations handling PII and financial data must report breaches within strict timelines. 📑
Potential consequences may include:
- Regulatory fines
- Mandatory disclosure to affected customers
- Legal claims
- Reputation damage
Telecom providers operate in highly regulated environments, making incident response transparency essential.
Practical Checklist for Potentially Affected Customers
Here is a practical action checklist:
✅ Change all passwords associated with your Odido account
✅ Enable multi-factor authentication (MFA)
✅ Monitor bank statements for unusual transactions
✅ Watch for phishing emails and SMS messages
✅ Consider credit monitoring services
A common question: Should you immediately cancel your bank account?
Not necessarily. First, monitor transactions closely and consult your bank. Cancel accounts only if fraudulent activity is detected. 🛡️
Prompt action can reduce the impact of exposed credentials.
Lessons for Telecom Providers and MSSPs
This alleged telecom data leak highlights several lessons for Managed Security Service Providers and telecom operators.
A strong Darknet Monitoring Solution
FOR MSSP environments can provide early alerts when corporate assets appear on underground forums. Combined with internal logging, threat intelligence feeds, and SIEM integration, this enhances visibility across digital assets.
Security leaders should prioritize:
- Continuous vulnerability scanning
- Access control hardening
- Encryption of stored credentials
- Regular penetration testing
- Incident response rehearsals
Proactive investment in a comprehensive dark web solution helps organizations detect early-stage exposure before it escalates.
The Broader Cybersecurity Context
The Odido data breach claim illustrates how threat actors increasingly combine extortion with public shaming tactics. 🧨
Even unverified claims can cause stock fluctuations, customer anxiety, and media scrutiny. Therefore, organizations must maintain strong crisis communication strategies.
Security experts emphasize that prevention is only part of the equation. Rapid detection, containment, and transparent communication are equally important in minimizing reputational fallout.
For additional threat analysis and breach intelligence resources, explore Darknetsearch.com platform to stay updated on emerging risks.
Conclusion: Vigilance Is the Only Sustainable Defense
The alleged Odido data breach underscores the evolving nature of cyber threats targeting telecom providers. With claims of exposed PII, financial data, and plaintext passwords, the potential impact could be significant if verified. 🚨
The timeline—from the 24 February warning to the 27 February forum post—demonstrates how quickly incidents can escalate in today’s digital threat landscape.
Organizations must strengthen data breach detection capabilities, invest in proactive intelligence, and integrate monitoring across their entire security stack. Customers, meanwhile, should remain alert and take immediate precautionary measures if notified.
Cyber risk is no longer hypothetical—it is operational. Staying informed and prepared is the only sustainable defense strategy. 🔎
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

