➤Summary
The Ochsnersport data leak has recently gained attention after an alleged dataset linked to Ochsnersport.ch appeared on a well-known cybercrime forum. According to a post published on Breachforums.as on 05 March 2026, a user identified as Araknise claimed to possess a database containing customer information associated with the Swiss sports retailer. The listing reportedly includes various personal and transactional records such as emails, phone numbers, purchase histories, and delivery tracking information. The Kaduu team discovered the database while conducting routine monitoring of dark web communities where cybercriminals often advertise stolen datasets. Although the authenticity of the information remains under investigation, cybersecurity specialists are treating the situation seriously due to the scope and sensitivity of the alleged records. The Ochsnersport data leak highlights ongoing concerns about e-commerce platform security and the risks posed when customer data circulates in underground marketplaces. 🔎
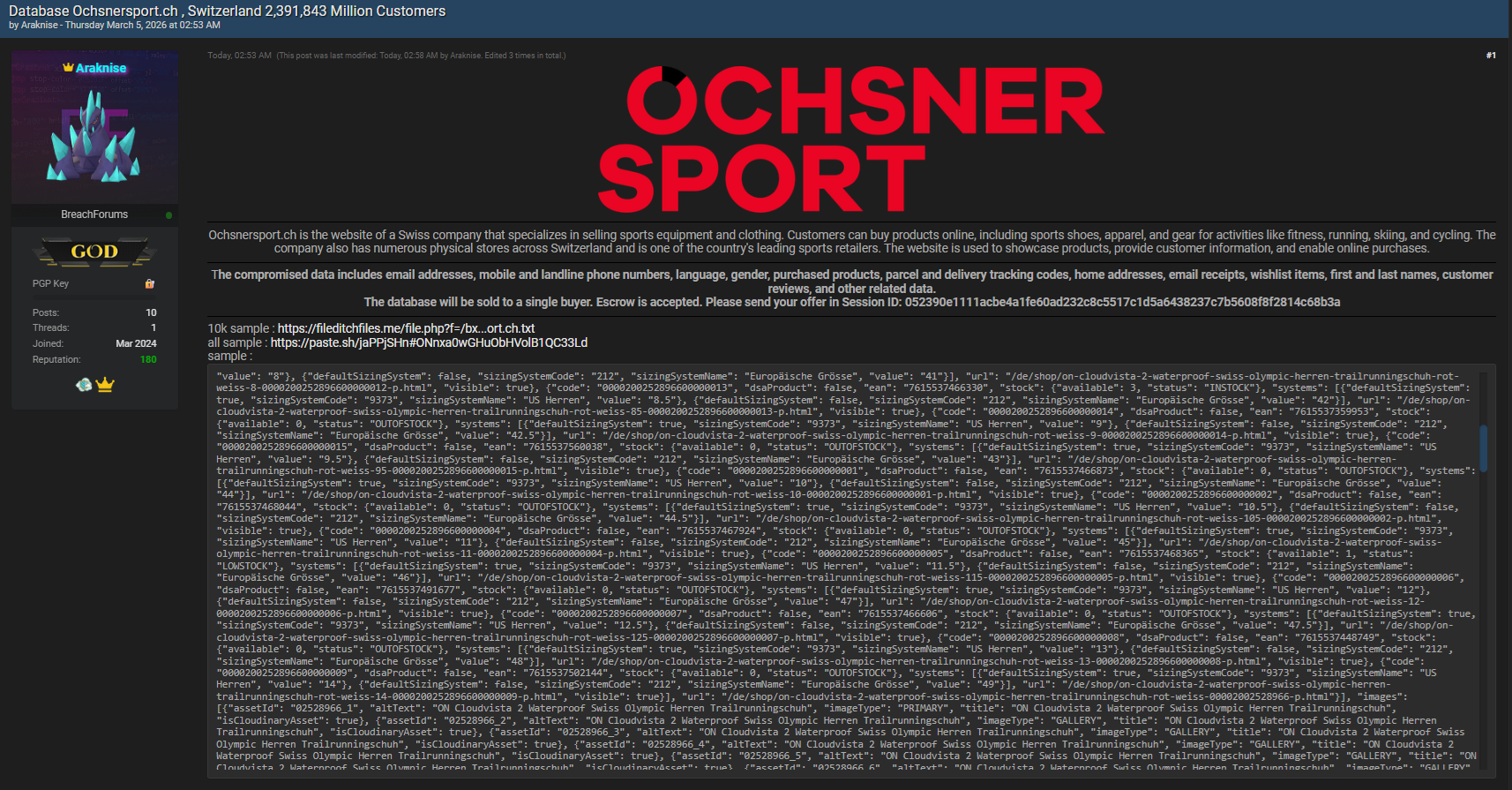
Overview of the Alleged Breach Listing
The alleged dataset was reportedly posted on Breachforums.as with the following details:
- Forum: Breachforums.as
- Author: Araknise
- Publication date: 05.03.2026
- Discovery: Identified by the Kaduu team during dark web monitoring
Threat intelligence analysts often track such listings to identify potential cybersecurity incidents early. Platforms dedicated to monitoring underground activity, such as resources discussed on , regularly detect new database postings that may impact organizations worldwide. 🛡️
While some forum claims can be exaggerated, the presence of detailed data categories in this case has prompted further analysis from cybersecurity professionals.
Types of Customer Information Allegedly Exposed
According to the forum description, the Ochsnersport data leak may involve several categories of consumer information commonly stored by online retail platforms.
Personal Details
The compromised data reportedly includes identifying information such as:
- First and last names
- Email addresses
- Gender and language preferences
- Home addresses
- Mobile and landline phone numbers
Exposure of these details could allow cybercriminals to construct accurate customer profiles for phishing or social engineering campaigns.
E-commerce Transaction Data
In addition to identity information, the listing allegedly contains transactional records, including:
- Purchased products
- Email purchase receipts
- Wishlist items
- Customer reviews
Such records reveal buying habits and consumer behavior patterns, which attackers can exploit to create highly convincing scams. 💻
Delivery and Logistics Data
Another critical component of the alleged leak involves delivery information:
- Parcel tracking numbers
- Shipment codes
- Delivery addresses
Delivery information is particularly sensitive because criminals sometimes use tracking details to impersonate courier services or send fraudulent shipping notifications.
Why Retail Databases Are Valuable to Cybercriminals
Retail databases are among the most sought-after assets in cybercrime markets. They combine personal identity information with purchasing behavior, creating datasets that can be monetized through several methods.
Common uses include:
- Targeted phishing campaigns
- Credential-stuffing attacks
- Fraudulent marketing scams
- Reselling customer data to other criminal groups
Cybersecurity experts note that stolen retail databases often circulate multiple times in underground markets. Even when companies mitigate initial exposures, datasets can continue to appear in secondary leaks months or years later.
The alleged Ochsnersport database breach therefore illustrates the long-term risks associated with customer data exposure.
How Dark Web Monitoring Detected the Listing
The Kaduu team reportedly discovered the dataset while scanning dark web forums where hackers advertise stolen information. Threat intelligence teams frequently use automated tools and manual analysis to track suspicious posts and verify leaked content samples.
The monitoring process usually includes:
- Detecting newly published listings on cybercrime forums
- Collecting metadata or data samples
- Comparing records with known datasets
- Alerting organizations potentially affected
Guides such as those available on explain how this monitoring helps detect breaches earlier than traditional reporting channels.
This process is widely considered a key component of modern data breach detection practices. 🌐
Potential Risks for Affected Customers
If the alleged Ochsnersport data leak is confirmed, customers whose information appears in the dataset could face several cybersecurity risks.
Main Threats
- Phishing emails referencing recent purchases
- Fake delivery notifications using real tracking numbers
- Identity-based scams using leaked contact details
- Account takeover attempts through credential reuse
Because the dataset reportedly includes purchase histories, attackers may craft highly convincing messages impersonating retailers or delivery services.
Question: Can purchase data really lead to fraud?
Yes. When criminals know what products someone bought and when they were delivered, they can create personalized scams that appear legitimate, significantly increasing the likelihood that victims will trust the message. 📦
The Importance of Brand Monitoring and Digital Security
For companies operating online retail platforms, incidents like the alleged Ochsnersport database breach demonstrate the importance of continuous monitoring of digital environments. Cybersecurity programs increasingly integrate proactive monitoring systems that track mentions of corporate data across underground forums and marketplaces.
Effective brand protection strategies typically include:
- Dark web surveillance
- Credential leak monitoring
- Threat intelligence analysis
- Rapid incident response protocols
Organizations that detect leaks quickly can reduce reputational damage and limit exploitation by cybercriminals.
Legal and Privacy Implications
If verified, a customer database exposure involving Swiss users could raise significant privacy and regulatory concerns. Organizations operating in Europe must comply with strict data protection frameworks designed to safeguard personal information.
These obligations may include:
- Conducting a forensic investigation
- Notifying affected individuals
- Reporting incidents to relevant authorities
- Implementing stronger cybersecurity controls
According to guidance published by , proactive monitoring and transparency are essential components of effective breach response strategies. ⚖️
Practical Checklist for Customers
Individuals who suspect their information might appear in the alleged Ochsnersport data leak should take precautionary steps to protect themselves.
Customer Protection Checklist
✅ Change passwords associated with retail accounts
✅ Enable two-factor authentication when available
✅ Monitor bank statements and purchase confirmations
✅ Ignore suspicious shipping notifications
✅ Verify emails claiming to represent retailers
Practical Tip: Attackers often impersonate courier services, so always verify tracking links directly on official delivery websites rather than clicking email links. 🔐
Indicators Companies Should Watch
Retail companies investigating potential breaches should monitor several indicators that may signal misuse of leaked data:
- Increased phishing campaigns referencing products
- Unauthorized login attempts from unusual regions
- Spikes in password reset requests
- Customer reports of suspicious emails
Early identification of these signals helps organizations respond quickly and protect their customers.
Broader Cybersecurity Lessons for E-Commerce
The alleged Ochsnersport data leak illustrates broader cybersecurity challenges facing online retailers. E-commerce platforms process large volumes of personal information, making them attractive targets for cybercriminals.
Common vulnerabilities in retail environments include:
- Weak password policies
- Insufficient monitoring of login attempts
- Poor segmentation between systems
- Inadequate encryption of stored data
Improving these areas can significantly reduce the risk of future data exposures.
LSI concepts connected to this incident include customer privacy protection, cybersecurity incident response, identity theft prevention, dark web intelligence monitoring, database security practices, and online retail security strategies.
What Happens Next?
When datasets appear on underground forums, cybersecurity researchers typically analyze them to determine authenticity. This process involves examining database structure, verifying sample records, and identifying overlaps with previously leaked data.
If the alleged Ochsnersport database breach proves genuine, investigators may work with affected organizations to assess the scope of exposure and mitigate further risk.
Even if the dataset is incomplete or outdated, criminals may still exploit the information to launch scams or phishing attacks. Awareness therefore remains a crucial defense.
Conclusion
The alleged Ochsnersport data leak highlights the growing risks faced by online retailers and their customers in today’s digital economy. Whether confirmed or not, the appearance of such datasets on cybercrime forums demonstrates how quickly personal information can circulate within underground markets. For customers, vigilance and strong cybersecurity practices remain essential to preventing fraud. For organizations, proactive monitoring, incident response planning, and transparent communication are critical steps toward maintaining trust in the digital marketplace. 📢
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

