➤Summary
The NSP data leak has emerged as one of the most discussed cybersecurity incidents circulating across dark web communities in early 2026. According to dark web monitoring reports, an alleged compromise involving India’s National Scholarships Portal (nsp.gov.in) surfaced on a well-known cybercrime forum, raising concerns about large-scale exposure of student and financial records. The dataset was reportedly identified by the Kaduu team during routine surveillance of underground marketplaces where stolen databases are often traded or shared. While official confirmation remains pending, cybersecurity researchers are treating the situation seriously due to the sensitivity of the information involved and the scale suggested by forum posts. This darknetsearch.com article examines what is known so far, what data may have been exposed, potential risks, and how individuals and institutions can respond responsibly to such incidents. 🔎
Overview of the Alleged Incident
The alleged NSP data leak was posted on the forum breachforums.as by a user identified as SORB. According to the listing:
- Date of hacking: 15 February 2026
- Date published: 05 March 2025 (as claimed in the forum listing)
- Discovery: Kaduu team during dark web monitoring
The post reportedly advertised access to a database associated with the National Scholarships Portal, a government platform used by students across India to apply for scholarship programs and financial aid. Monitoring analysts discovered the listing while scanning cybercriminal marketplaces, similar to investigations documented on platforms like. The appearance of such listings does not automatically confirm authenticity, but cybersecurity experts treat them as early indicators requiring verification and investigation. 🛡️
What Data Was Allegedly Compromised
The forum post claims the database contains multiple categories of sensitive records, suggesting a broad personal information exposure. Below is a structured overview suitable for quick reference.
Student Information
- student_name
- gender
- aadhaar number
- mobile phone
- full address
- admission_year
- educational district details
- school and university names
- institute_name and institute_district_name
Parental Information
- FatherName
- MotherName
- ParentMobileNo
- FamilyAnnualIncome
- parent_income records
Financial and Banking Data
- account_no
- bank_name
- ifs_code
- payment history fields
- scholarship payment account details
Web Account Details
- username
- password hash
- registered mobile number
Payment Dataset Fields
- yyyymm transaction dates
- student_id
- amount transferred
- paid_account_holder_name
- paid_aadhaar_number_as_per_bank
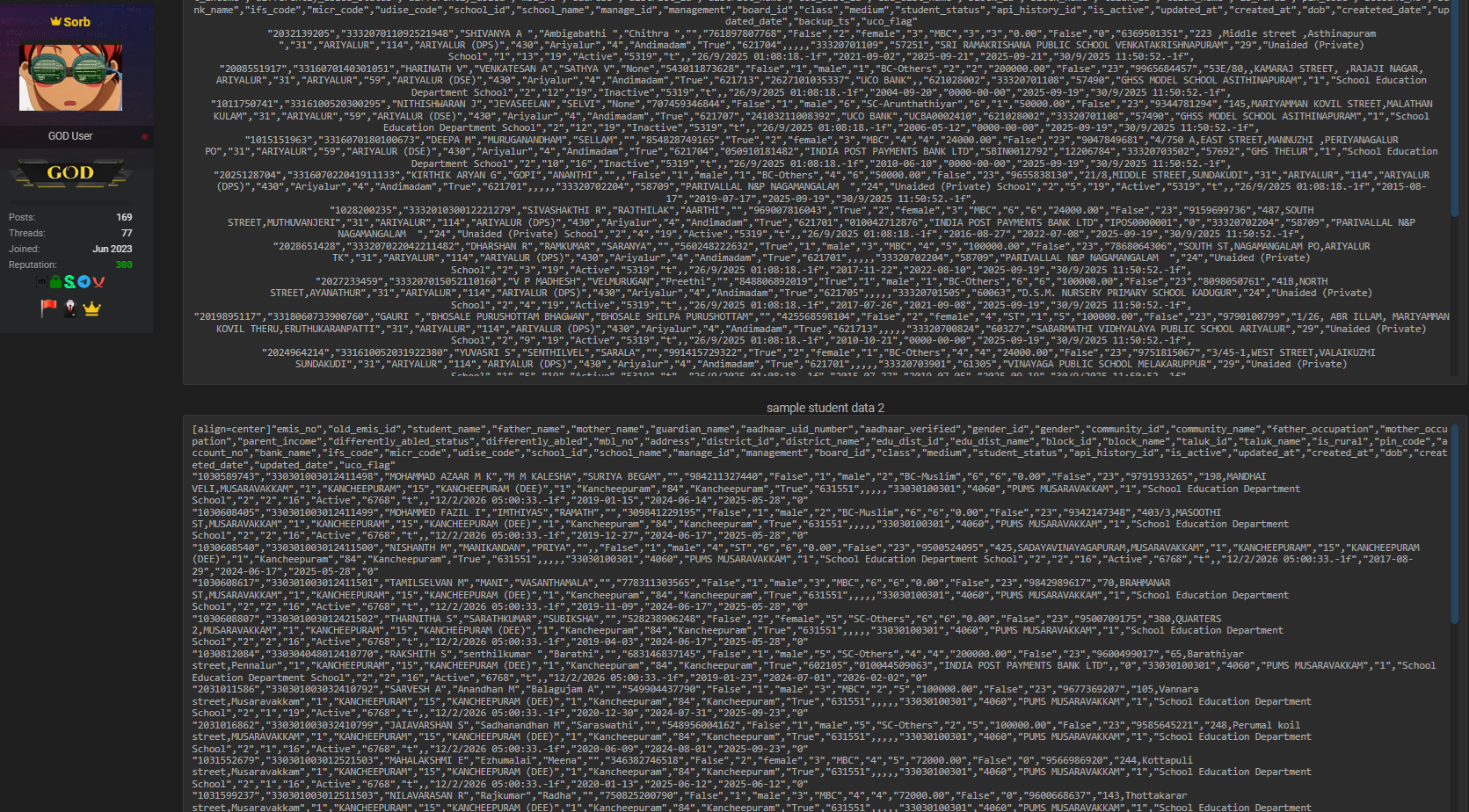
The combination of identity and banking elements makes the alleged National Scholarships Portal breach particularly concerning because attackers could theoretically correlate multiple identity layers within a single dataset. 💻
Why This Alleged Database Matters
Educational portals contain highly concentrated identity profiles. Unlike isolated leaks, scholarship systems often combine academic, financial, and demographic information. This increases the value of such data in cybercriminal ecosystems.
Potential consequences include:
- Identity theft risk through Aadhaar misuse
- Targeted phishing campaigns against students
- Financial fraud attempts using banking metadata
- Social engineering attacks against families
Cybersecurity analysts emphasize that breaches involving educational systems frequently affect younger populations who may have limited awareness of online privacy risks. As one cybersecurity analyst noted:
“Student databases are uniquely sensitive because they connect identity, education history, and financial aid in one place.”
The alleged NSP data leak therefore represents more than a technical issue—it could impact trust in digital public services if confirmed.
How the Database Was Discovered
The Kaduu team reportedly identified the dataset during routine scanning of dark web forums, a process widely used in proactive threat intelligence. Investigators often rely on automated crawlers combined with human analysis to detect new postings advertising stolen data. Tools discussed in research sections of help analysts identify keywords, database samples, and seller reputation scores.
Typical monitoring workflow includes:
- Tracking new marketplace listings
- Verifying sample records
- Comparing leaked structures with known systems
- Alerting affected organizations
This process is a core component of modern data breach detection practices, allowing early warning before widespread exploitation occurs. 🧠
Key Risks for Students and Families
If the alleged National Scholarships Portal breach proves authentic, affected individuals could face several real-world risks.
Primary threats include:
- Fraudulent bank account verification calls
- Scholarship scam messages
- SIM swap attempts using leaked identifiers
- Credential stuffing attacks on other platforms
Because the dataset reportedly contains both Aadhaar and banking references, cybercriminals may attempt layered fraud schemes rather than immediate financial theft.
Question: Can leaked scholarship data actually lead to financial fraud?
Answer: Yes. Even partial financial metadata combined with identity details can enable social engineering attacks that trick victims into revealing additional credentials.
The Role of Dark Web Forums in Modern Cybercrime
Dark web forums serve as marketplaces where hackers showcase stolen databases to build reputation or sell access. Listings often include:
- Sample rows of data
- Screenshots
- Claims about record counts
- Cryptocurrency pricing
Researchers at explain that many postings exaggerate claims, making independent validation essential. However, even unverified leaks can trigger copycat scams once criminals begin referencing them publicly. 🌐
Legal and Compliance Considerations
Large-scale exposure of personal data raises regulatory questions worldwide. Although the portal operates within India, international standards such as GDPR influence global expectations regarding user privacy and accountability. Institutions managing student systems increasingly adopt principles aligned with student data protection to prevent misuse and ensure responsible data handling.
Organizations facing alleged leaks typically must:
- Conduct forensic investigations
- Notify stakeholders where required
- Implement remediation controls
- Strengthen monitoring systems
For authoritative cybersecurity guidance, readers can consult , a widely cited resource explaining incident response best practices. ⚖️
Checklist: How Individuals Can Protect Themselves
If you believe your information might appear in the alleged NSP data leak, follow this practical checklist:
✅ Monitor bank account statements weekly
✅ Avoid clicking scholarship-related links from unknown senders
✅ Enable two-factor authentication on email accounts
✅ Change passwords reused across platforms
✅ Verify calls claiming to represent government agencies
✅ Report suspicious activity immediately
Practical Tip: Never share OTPs or Aadhaar details over phone calls, even if the caller claims to verify scholarship payments.
Indicators Organizations Should Watch
Educational institutions and administrators should monitor signs suggesting misuse of exposed records:
- Increased phishing emails referencing scholarships
- Unauthorized login attempts from unusual regions
- Sudden password reset spikes
- Student complaints about scam messages
These indicators help security teams determine whether a database breach is actively being exploited.
Broader Cybersecurity Lessons
The alleged NSP data leak highlights recurring issues in public digital infrastructure:
- Centralized databases attract attackers
- Legacy security configurations increase risk
- Identity aggregation magnifies consequences
Cybersecurity maturity now depends heavily on continuous monitoring rather than periodic audits. Governments worldwide are investing in zero-trust architecture and improved encryption practices to reduce exposure risks.
LSI concepts frequently associated with incidents like this include cybersecurity incident response, database breach analysis, cybercriminal marketplace activity, identity protection strategies, financial data compromise prevention, and proactive threat intelligence.
What Happens Next?
At the time of writing, independent verification remains ongoing. Authorities and cybersecurity researchers typically analyze:
- Database structure authenticity
- Record formatting consistency
- Hash algorithm validity
- Overlap with previously known leaks
Only after technical validation can investigators determine whether the alleged National Scholarships Portal breach represents a genuine compromise or a recycled dataset.
Public awareness still plays a crucial role. Even unconfirmed leaks can lead to scams exploiting fear and confusion among students and parents. 📢
Conclusion: Awareness Is the First Line of Defense
The alleged NSP data leak demonstrates how quickly sensitive information can surface within underground communities and spread globally. Whether confirmed or disproven, the incident underscores the importance of vigilance, responsible data governance, and early threat monitoring. Students, institutions, and policymakers must treat digital identity protection as a shared responsibility in an increasingly connected educational ecosystem. By staying informed and adopting proactive cybersecurity habits, individuals can significantly reduce exposure risks and prevent attackers from turning leaked information into real-world harm. 🔐
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

