➤Summary
The Infutor data breach has surfaced as a major topic of discussion across cybersecurity communities after a post appeared on the forum breachforums.as on March 8, 2026. According to the author, known as Spirigatito, a massive dataset allegedly linked to Infutor.com has been leaked and shared online. The post claims that the breach contains the personal data of hundreds of millions of Americans, including both living and deceased individuals.
The discovery was first flagged by the Kaduu team during routine monitoring of underground communities where tech industry leaks and compromised databases frequently circulate. If the claims are accurate, the scale of this alleged Infutor data leak could make it one of the largest exposures of personal information discussed in dark web forums this year.
In this darknetsearch.com article, we examine what is currently known about the incident, what information may have been compromised, and why organizations and individuals should pay attention to this developing situation. We also explore how modern dark web monitoring solutions help security teams identify and respond to potential data exposures faster. 🔍
Overview of the Alleged Infutor Data Leak
The alleged Infutor data leak was published by a forum user named Spirigatito on the well-known breach marketplace breachforums.as. According to the post, the dataset contains a staggering 676,798,866 unique records of American citizens.
The author wrote:
“The breach includes 676 798 866 unique citizens americans (including deceased persons). Thanks to SocRadar for the article, which allowed me to download all the data.”
While the authenticity of the dataset has not yet been independently confirmed, the claim alone has sparked widespread interest among cybersecurity researchers and threat intelligence teams. Large-scale datasets appearing on such forums often trigger further investigations to determine whether the data originates from a direct breach, aggregation from multiple sources, or public records compilation.
The Kaduu team reportedly identified the database during a routine scan of underground communities. These forums are frequently monitored by analysts performing dark web search operations to detect emerging threats and exposed datasets. 🕵️♂️
What Data Is Allegedly Included
According to the forum listing, the dataset contains a broad set of personal information fields. If authentic, the data could potentially enable identity theft, fraud, or social engineering campaigns.
Below is a simplified breakdown of the fields reportedly included in the leaked database:
| Data Field | Description |
| Full Name | First and last name of the individual |
| Date of Birth | Birth date information |
| Address | Residential street address |
| City | City of residence |
| State | State of residence |
| ZIP Code | Postal code |
| Phone Number | Personal contact number |
| SSN | Social Security Number |
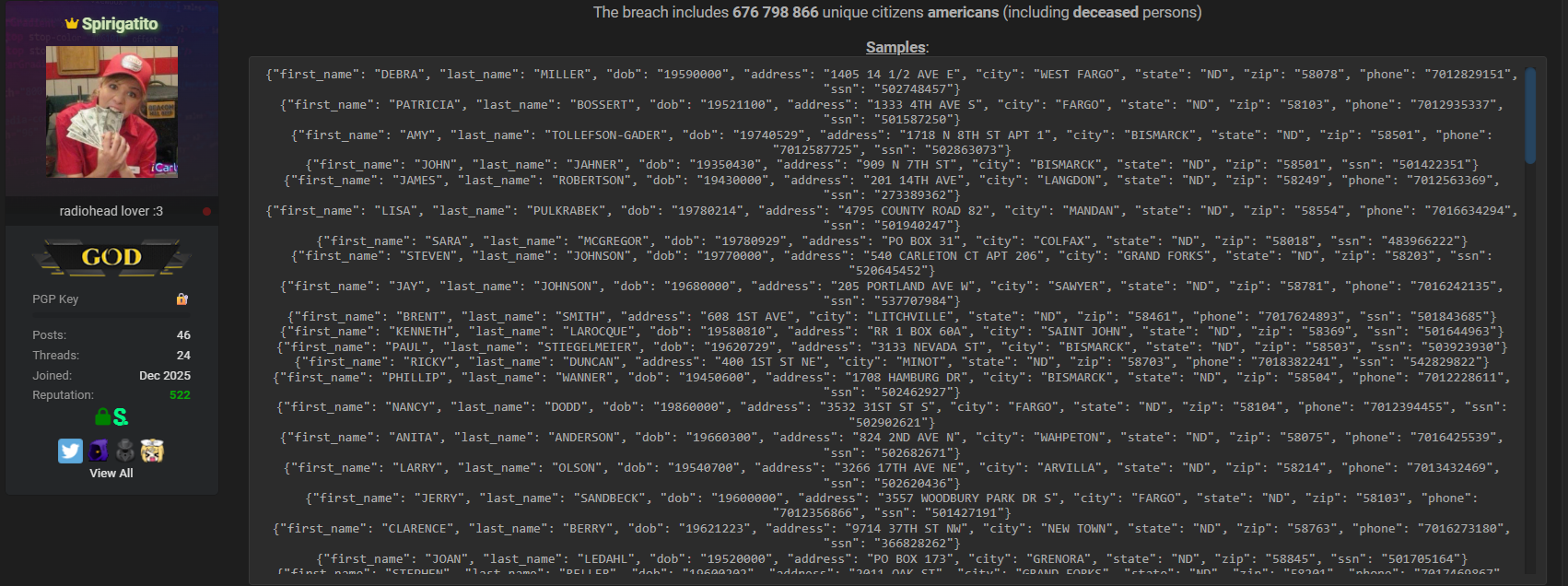
The presence of Social Security numbers significantly increases the sensitivity of the dataset. Combined with names and addresses, SSNs can enable criminals to attempt identity fraud or open fraudulent financial accounts.
Because the dataset reportedly includes both living and deceased individuals, analysts believe it may include information aggregated from multiple sources over time rather than a single transactional system compromise.
Why the Infutor Data Breach Claim Matters
Even though the alleged Infutor data breach is still under verification, the scale of the claim is notable. A dataset containing more than 676 million records would rank among the largest personal information exposures discussed online.
Large data compilations like this are often used by threat actors for activities such as:
- Identity fraud
- Phishing campaigns
- Credential stuffing preparation
- Targeted social engineering
- Large-scale spam operations
Such incidents also highlight the broader risks associated with data aggregation platforms and third-party information providers. Companies that collect and process large volumes of consumer data must maintain strong safeguards to protect sensitive records.
Increasingly strict Cybersecurity regulations in multiple regions require organizations to implement advanced data protection practices, breach reporting procedures, and risk management frameworks. 📊
How Security Teams Detected the Database
The Kaduu team reportedly discovered the dataset during routine monitoring activities across underground marketplaces and hacking forums. This type of monitoring is now considered a critical component of modern threat intelligence.
Security teams frequently track underground communities where hackers and brokers share stolen information. Early detection allows organizations to:
- Identify potential exposures quickly
- Investigate whether their systems were compromised
- Notify affected customers if necessary
- Prevent further exploitation
Organizations using specialized threat intelligence platforms can often detect leaked datasets shortly after they appear online. In many cases, security teams discover these exposures before they become widely distributed across multiple criminal communities.
Several resources, such as https://darknetsearch.com/, provide insights into how analysts monitor and track emerging threats in underground ecosystems.
Is the Dataset Authentic?
A common question among cybersecurity researchers is simple: Is the leak real?
The answer right now is uncertain.
When large datasets appear on underground forums, they typically go through several verification stages:
- Sample analysis – Security researchers analyze small samples of the data.
- Source validation – Analysts check whether the information appears legitimate or recycled from older breaches.
- Cross-referencing – Data points are compared against previously known leaks.
- Infrastructure investigation – Experts attempt to determine whether the data could originate from the claimed organization.
Until these steps are completed, the alleged Infutor data leak should be treated as a developing situation rather than a confirmed breach.
Cybersecurity researcher from https://krebsonsecurity.com/ has often emphasized that many large datasets circulating online are compilations of multiple historical breaches rather than new intrusions. This possibility remains under investigation in this case as well. 🧠
Practical Checklist: How Organizations Should Respond
Regardless of whether the incident proves to be a direct breach or a compiled dataset, organizations can use situations like this as an opportunity to strengthen their security posture.
Here is a quick cybersecurity checklist:
✔ Monitor underground forums for potential exposures
✔ Deploy automated threat intelligence tools
✔ Encrypt sensitive personal information
✔ Implement strict access controls for databases
✔ Conduct regular penetration testing
✔ Establish a rapid incident response plan
✔ Train employees to recognize phishing attacks
Proactive monitoring can help organizations detect early warning signs of potential breaches before they escalate.
The Growing Trend of Massive Data Exposures
The cybersecurity landscape has changed dramatically over the past decade. Massive data compilations involving hundreds of millions of records are no longer rare events.
Several factors contribute to this trend:
- Growth of data brokerage platforms
- Increasing number of online services storing personal information
- Expanded attack surfaces across cloud infrastructure
- Sophisticated threat actor marketplaces
As a result, organizations across industries must treat large-scale data protection as a core business priority rather than a purely technical concern.
The alleged Infutor data breach demonstrates how quickly a dataset can attract attention once it appears on a major forum.
The Role of Dark Web Monitoring
One of the most effective ways to detect potential exposures is through continuous monitoring of underground sources. Advanced threat intelligence platforms track thousands of marketplaces, forums, and encrypted channels where cybercriminals share stolen information.
These monitoring systems help organizations:
- Identify leaked credentials
- Detect employee account compromises
- Discover stolen corporate documents
- Track criminal activity targeting their brand
Businesses that deploy monitoring tools gain valuable early warnings when their information appears in suspicious environments.
Security teams can learn more about threat monitoring strategies through dark web monitoring platforms and guides explaining how cyber threat intelligence works. 🔐
What Individuals Should Do If Their Data Appears in a Leak
Large datasets involving personal information can create serious risks for individuals. If your information appears in a leaked database, it is important to take immediate precautions.
Recommended actions include:
- Monitoring bank and credit card statements
- Enabling multi-factor authentication
- Placing a credit freeze or fraud alert
- Being cautious with unsolicited phone calls or emails
- Checking identity monitoring services
These steps help reduce the chances of criminals exploiting exposed personal data.
Conclusion
The alleged Infutor data breach posted on breachforums.as has raised important questions about data aggregation, identity protection, and cybersecurity vigilance. With claims of 676,798,866 records containing sensitive personal details such as names, addresses, and Social Security numbers, the incident—if confirmed—would represent one of the largest datasets discussed on underground forums in recent years.
At the moment, the authenticity and origin of the dataset remain under investigation. However, the discovery by the Kaduu team highlights how crucial continuous threat intelligence and monitoring have become in today’s digital environment. 🌐
Organizations that proactively track underground activity can detect potential exposures earlier, protect their customers, and respond faster to emerging threats.
If you want to better understand how cyber intelligence platforms uncover breaches like this, explore advanced monitoring resources and research tools available online. 🚨
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

