➤Summary
The Global-e breach surfaced after the Kaduu team identified an alleged dataset during routine Dark web monitoring of underground forums. The listing claims exposure of Global-e Smart Cross-Border Ledger Orders data, raising concerns for brands that rely on cross-border infrastructure to serve international customers. This darknetsearch.com article breaks down what is known, what is not, and what organizations should do next—without speculation—so decision-makers can respond with clarity and speed. 🔎
What is Global-e Smart Cross-Border Ledger Orders and why it matters
Global-e provides a platform that enables merchants to manage international sales, taxes, duties, and localized checkout experiences. The Smart Cross-Border Ledger Orders component records order activity across regions, making it a critical operational layer. An alleged exposure here matters because it aggregates customer identities, addresses, and purchase history across borders, amplifying privacy and compliance implications.
In the context of a Global-e breach, even non-financial data can be leveraged for targeted fraud and social engineering when combined with other leaks. 🌍
Discovery details and underground forum activity
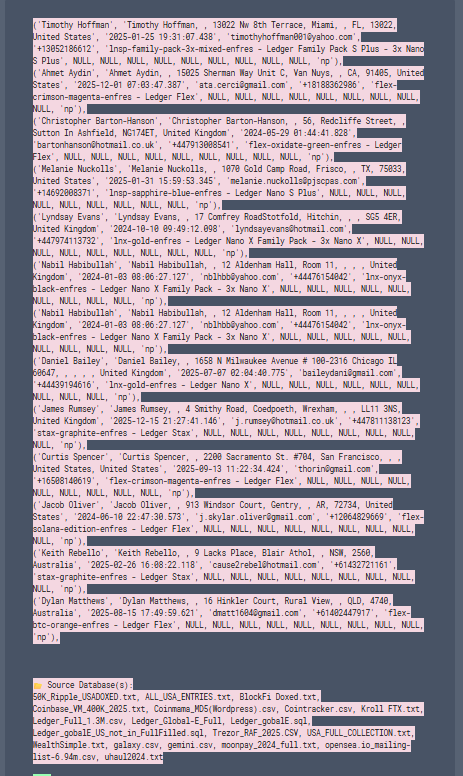
According to Kaduu, the dataset was advertised by the alias “x0mbe” on Breachforums.as on 06 January 2026. The seller claimed access to tens of thousands of records spanning the USA, UK, and Australia. Such disclosures are typically uncovered through a Dark web solution that scans criminal marketplaces for early indicators of compromise. Although underground claims can be exaggerated, analysts treat listings tied to named enterprise platforms with heightened scrutiny, especially when samples align with known schemas. 🕵️
What data was allegedly exposed
The listing states that exposed information included names, contact details, shipping addresses, and purchase history. Importantly, it explicitly excluded sensitive cryptographic data such as 24-word recovery phrases, private keys, PINs, or payment card details. This distinction reduces immediate financial theft risk but does not eliminate downstream threats.
In a Global-e breach, enriched order histories can still enable convincing phishing, account takeover attempts on related services, and business email compromise scenarios. 📦
Geographic distribution of affected records
The alleged dataset totals 49,894 records, with regional breakdowns reported as USA (30,907), UK (7,654), and Australia (11,928), plus a small number from additional countries. This distribution reflects Global-e’s core markets and underscores the cross-border nature of the exposure. For compliance teams, multi-jurisdictional impact introduces varied notification timelines and regulatory expectations, increasing response complexity. 🌐
Assessing credibility and risk signals
Is the claim credible? In this case, yes. The incident is supported by an official disclosure confirming unauthorized access to order-related data within the Global-e cloud-based information system. According to the notice, Global-e identified and investigated the issue and began notifying affected customers who made purchases on Ledger.com using its services. The exposed data included order and customer information, while payment details were explicitly not affected. This confirmation elevates the Global-e breach from an alleged listing to a verified security incident. Risk teams should therefore treat this as a confirmed data exposure, prioritize impact assessment, and review third-party risk controls rather than approaching it as speculative intelligence. ⚠️
Why this matters for merchants and consumers
Merchants using Global-e depend on trust and continuity. An exposure of order metadata can reveal purchasing patterns, high-value customers, and logistics partners. Consumers may face targeted scams referencing recent purchases. This is where data breach detection capabilities become critical, enabling faster containment and communication. The broader lesson is that operational data, not just payment data, carries material risk when leaked. 🧠
One key question—and a clear answer
Does this alleged incident expose wallets or payment cards? The answer is no, based on the seller’s description; no cryptographic secrets or card details were included. However, non-sensitive data can still be abused when combined with other sources on the dark web, so vigilance remains essential. 🔐
Practical checklist for organizations
Use the following checklist to respond effectively to signals like the Global-e breach:
- Verify logs and access controls around order and ledger systems
- Rotate API keys and service credentials associated with cross-border services
- Review third-party integrations and least-privilege access
- Prepare customer communication templates in case confirmation occurs
- Monitor underground chatter for follow-on activity using trusted intelligence feeds
This approach aligns with the CIA Triad by preserving confidentiality, integrity, and availability while investigations proceed. ✅
Strengthening defenses across the ecosystem
Preventing future incidents requires layered controls: regular audits, segmentation of order systems, anomaly detection, and vendor risk management. Continuous intelligence from platforms like dark web monitoring platforms help teams spot early warning signs, while ongoing analysis via https://darknetsearch.com/ resources supports readiness. Incorporating lessons from alleged events such as this improves resilience across global commerce operations. 🛡️
Conclusion and next steps
The Global-e breach claim, while unconfirmed, highlights the evolving risk landscape for cross-border eCommerce platforms in 2026. Order data is valuable, portable, and actionable for attackers, making early detection and disciplined response essential. Organizations should assess exposure, reinforce controls, and stay informed through credible intelligence sources. For deeper insights and proactive protection strategies, explore expert analysis on https://darknetsearch.com/ and ensure your teams are prepared for what comes next. 🚀
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

