➤Summary
The EVCDE data leak has emerged as a serious cybersecurity concern after an alleged dataset linked to evcde.com, operated by EndoVascular Consultants – Vascular Specialists of Delaware, appeared on a dark web forum. According to a listing on Breachforums.as published by a user known as iProfessor, the database reportedly contains sensitive patient information and medical documents totaling approximately 13 GB. The dataset allegedly includes admission records, clinical photographs, insurance documents, and highly sensitive personal identifiers such as Social Security numbers and dates of birth. The Kaduu team discovered the listing during routine monitoring of underground cybercrime forums where stolen databases are frequently advertised or sold. Although the authenticity of the leak is still under investigation, the potential scope and nature of the records raise serious privacy concerns and highlight the growing risk of healthcare sector cyber incidents. 🔎
Overview of the Alleged Breach Listing
According to the forum post, the dataset was advertised for sale with the following details:
Forum: Breachforums.as
Author: iProfessor
Breach Date: February 2026
Total Data Size: Approximately 13 GB
Data Type: Documents and photographs
Price: $4,000 USD
Threat intelligence analysts monitoring underground communities identified the post while scanning cybercrime marketplaces for newly leaked databases.
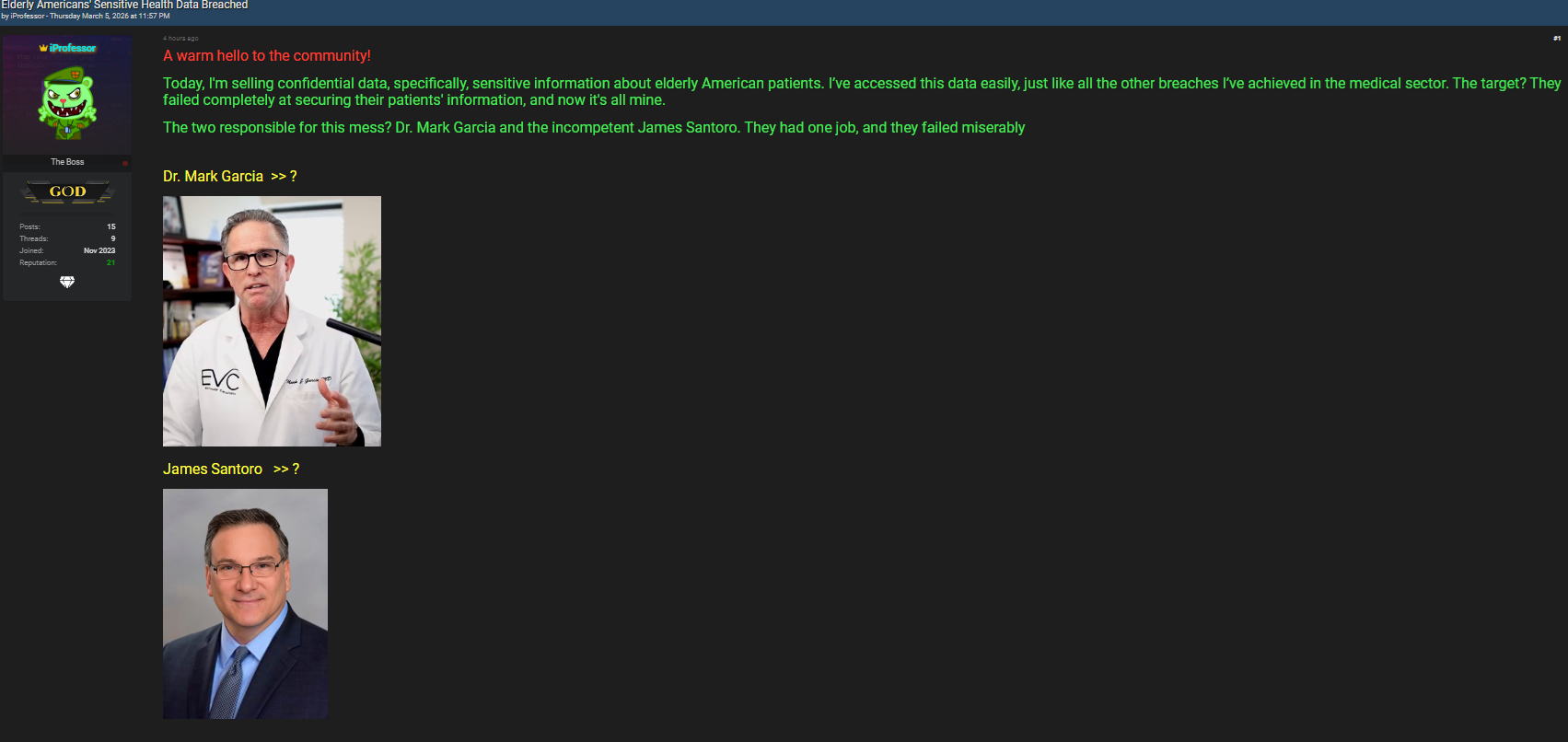
The listing suggests that the dataset may include a wide range of medical and administrative files connected to patients treated by the vascular specialists clinic.
Types of Information Allegedly Exposed
The alleged EVCDE data leak appears to involve multiple categories of highly sensitive healthcare records. If confirmed, the exposed files could reveal both personal identity information and detailed medical histories.
Personal Patient Information
The dataset reportedly contains core identity records, including:
- Patient names and contact information
- Social Security numbers (SSN)
- Dates of birth (DOB)
- Home addresses and phone numbers
Exposure of these elements significantly increases the risk of identity theft and financial fraud.
Medical Documentation
Another major category involves clinical documentation and healthcare records such as:
- Admission forms and patient registration documents
- Full medical reports and diagnostic records
- Insurance documentation
- Emergency contact details
Medical files are among the most sensitive forms of personal data because they reveal health conditions, treatment histories, and personal identifiers.
Photographs and Identity Scans
The dataset allegedly also contains visual and scanned materials:
- Clinical photographs of patients
- Scans of identification documents
- Uploaded administrative paperwork
Such materials can be particularly dangerous if exploited by criminals attempting impersonation or blackmail. 💻

Why Medical Data Is Highly Valuable on the Dark Web
Healthcare records are considered some of the most valuable data sold on cybercrime forums. Unlike credit card numbers, which can quickly be canceled, medical records contain long-term personal information that remains useful to criminals for years.
Common reasons hackers target healthcare institutions include:
- Rich identity data contained in patient files
- Insurance and billing information
- Long-term medical history records
- Weak cybersecurity infrastructure in some healthcare systems
Because of this value, healthcare databases frequently appear in underground markets. Monitoring platforms such as track these listings to help organizations detect potential breaches early. 🌐
What Makes Medical Breaches Especially Dangerous
A typical financial data breach may expose payment details, but healthcare leaks involve deeply personal information. If the alleged EVCDE data leak proves legitimate, the exposure could lead to multiple risks for affected patients.
Potential consequences include:
- Identity theft using SSN and personal details
- Fraudulent medical insurance claims
- Targeted phishing campaigns
- Privacy violations involving medical history
In many cases, criminals combine medical information with other leaked datasets to create detailed identity profiles. Such records can be used for advanced social engineering campaigns designed to trick victims into revealing additional confidential information. 🔐
How the Dataset Was Discovered
The Kaduu team reportedly identified the dataset during routine scanning of dark web forums. Threat intelligence teams frequently monitor these platforms because hackers often advertise stolen data before distributing it widely.
Typical detection workflow includes:
- Monitoring underground forums and marketplaces
- Identifying posts referencing organizations
- Collecting sample records or metadata
- Alerting researchers and affected entities
This proactive monitoring process is part of modern healthcare data breach detection strategies that aim to identify threats before widespread exploitation occurs. 🧠
Possible Regulatory and Legal Implications
Healthcare organizations operate under strict privacy frameworks designed to protect patient data. If verified, the alleged EVCDE data leak could raise significant compliance concerns.
Healthcare institutions may need to:
- Conduct a forensic cybersecurity investigation
- Notify affected patients
- Report incidents to regulators
- Implement stronger security measures
Guidelines from authorities such as explain the responsibilities organizations face when patient data is compromised. ⚖️
Globally, many jurisdictions have adopted privacy frameworks inspired by universal healthcare regulations that emphasize strict protection of sensitive medical information.
Potential Risks for Patients
If the alleged EVCDE data leak is confirmed, affected patients could face several serious risks.
Major Threats
- Identity theft using SSN and personal details
- Fraudulent medical billing schemes
- Phishing emails referencing medical treatment
- Insurance claim manipulation
Because medical data often includes multiple identifiers, criminals may attempt complex fraud schemes rather than immediate financial theft.
Question: Why do hackers sell medical databases instead of using them immediately?
Answer: Medical datasets can generate long-term profit when sold repeatedly to different criminal groups who use the information for identity theft, fraud, and phishing operations. 📊
Checklist: How Patients Can Protect Their Information
Individuals who believe their data may be affected should take precautionary steps to reduce potential harm.
Patient Security Checklist
✅ Monitor credit reports regularly
✅ Review insurance statements for suspicious claims
✅ Avoid responding to unexpected medical billing emails
✅ Enable identity theft alerts with credit agencies
✅ Contact healthcare providers directly to verify communications
Practical Tip: Fraudulent messages often reference real medical providers, so always verify communications using official contact channels rather than links in emails.
Indicators Healthcare Providers Should Monitor
Healthcare institutions investigating potential incidents should watch for warning signs that leaked data may be exploited:
- Sudden spikes in phishing attempts targeting patients
- Unusual login attempts on patient portals
- Unauthorized access to archived medical records
- Patient reports of suspicious insurance activity
Early detection can significantly reduce the impact of data exposures.
Broader Cybersecurity Lessons for Healthcare
The alleged EVCDE data leak highlights broader challenges in healthcare cybersecurity. Medical organizations manage extremely sensitive information but often operate complex IT environments that include legacy systems and multiple data storage locations.
Key security improvements include:
- Stronger encryption for stored medical files
- Multi-factor authentication for staff accounts
- Continuous monitoring of network activity
- Improved incident response planning
LSI concepts related to this incident include medical data privacy, patient record protection, cyber threat intelligence monitoring, identity theft prevention, healthcare cybersecurity risk management, and digital health record security.
What Happens Next?
When leaked databases appear in underground forums, investigators usually conduct technical analysis to determine whether the claims are genuine. This process may involve examining sample records, verifying metadata, and comparing data formats with known system structures.
If validated, the alleged EVCDE data leak could trigger formal investigations and regulatory scrutiny. Even if the dataset proves incomplete or outdated, criminals may still attempt to exploit the information for phishing or fraud campaigns. 📢
Conclusion
The alleged EVCDE data leak demonstrates the growing cybersecurity risks facing healthcare institutions and the severe consequences of medical record exposure. While verification is ongoing, the appearance of such datasets on cybercrime forums illustrates how valuable healthcare information has become in underground markets. Protecting patient data requires continuous monitoring, rapid incident response, and strong security practices across the entire healthcare ecosystem. Patients, healthcare providers, and cybersecurity professionals must work together to ensure that sensitive medical information remains protected in an increasingly digital healthcare environment. 🚨
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

