➤Summary
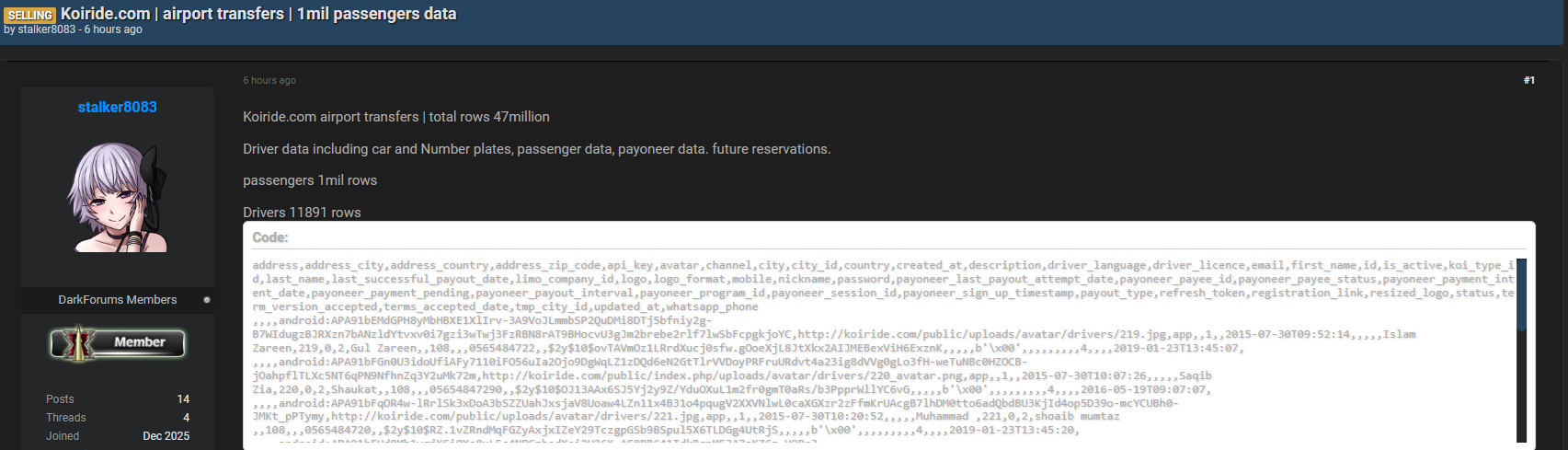
Data breach alert: an alleged leak involving koiride.com has surfaced on a dark web forum, raising serious concerns about the security of millions of users. Posted on March 17, 2026, by a user known as “stalker8083” on Darkforums.st, the database reportedly contains a massive 47 million rows of sensitive information. According to findings from the Kaduu team, discovered during routine monitoring, this breach includes both passenger and driver data, as well as financial details linked to payout systems. If verified, this incident could represent a significant cybersecurity failure in the transportation sector, emphasizing the growing need for data breach detection and advanced dark web solutions 🚨.
What We Know About the Koiride Leak
The alleged Koiride data breach involves a large-scale dataset reportedly extracted from the company’s systems. The data is said to include airport transfer service records, covering passengers, drivers, and operational details.
According to the forum post, the database contains:
- 47 million total rows
- 1 million passenger records
- 11,891 driver records
Additionally, the dataset is being sold for $1,000, making it accessible to a wide range of threat actors. The relatively low price increases the likelihood of misuse and exploitation 💻.
The Kaduu team identified this exposure through continuous monitoring, highlighting the importance of real-time data breach detection in identifying threats early.
Types of Compromised Data
The scope of this alleged leak is extensive, covering personal, operational, and financial data. Below is a simplified breakdown:
| Category | Data Included |
| Personal Info | First name, last name, email, phone, address |
| Location Data | City, country, zip code |
| Driver Details | License info, language, car data, number plates |
| Account Data | Passwords, API keys, tokens |
| Financial Info | Payoneer IDs, payout data, transaction timestamps |
| System Data | Registration links, session IDs, metadata |
This level of exposure significantly increases the risk of identity theft, financial fraud, and targeted cyberattacks 🔐.
Why This Incident Is Critical
Unlike smaller leaks, the Koiride data breach allegedly includes highly sensitive elements such as API keys, authentication tokens, and payout information. These details can be exploited to:
- Hijack user accounts
- Access financial systems
- Launch phishing campaigns
- Perform unauthorized transactions
Question: Why are API keys and tokens dangerous in a data breach?
Answer: Because they can provide direct access to systems without needing passwords, allowing attackers to bypass traditional security measures.
The Role of Dark Web Solutions in Detection
This case highlights the importance of dark web intelligence and monitoring tools. The Kaduu team’s discovery demonstrates how proactive surveillance can uncover threats before they escalate.
Organizations should invest in advanced dark web solutions that offer:
- Continuous monitoring of underground forums
- Automated alerts for leaked credentials
- Data breach detection capabilities
- Threat intelligence analysis
These tools help businesses track compromised data and respond quickly to incidents 🕵️♂️.
Cybersecurity Risks for Users and Businesses
The alleged data breach alert raises serious risks for both individuals and organizations:
For users:
- Identity theft and fraud 💳
- Unauthorized account access
- Exposure of personal travel data
- Phishing and social engineering attacks
For businesses:
- Regulatory penalties
- Loss of customer trust
- Operational disruption
- Brand reputation damage
According to IBM’s Cost of a Data Breach Report, the average cost of a breach continues to rise, making prevention and detection critical (https://www.ibm.com/security/data-breach).
Retail Cybersecurity and Transportation Platforms
Although Koiride operates in transportation, the incident reflects broader challenges in retail cybersecurity. Platforms handling transactions, user profiles, and payment systems share similar vulnerabilities.
Key lessons for retail cybersecurity include:
- Securing payment integrations
- Encrypting sensitive data
- Monitoring API usage
- Implementing zero-trust architectures
These measures are essential to protect both customer data and business operations 🛡️.
Practical Checklist: Protecting Against Data Breaches
Here’s a practical checklist to enhance security:
- Enable multi-factor authentication (MFA)
- Regularly update passwords and tokens
- Monitor accounts for unusual activity
- Use data breach detection tools
- Implement dark web solutions
- Secure APIs and access keys
- Educate users about phishing risks
💡 Practical tip: Automate monitoring systems to detect leaked credentials and suspicious activity in real time.
Expert Insight
Cybersecurity experts often emphasize the importance of proactive defense. As one industry analyst notes:
“Organizations must assume breaches will happen and focus on rapid detection and response rather than prevention alone.”
This mindset is critical in today’s evolving threat landscape.
What Should Companies Do Now
If the allegations are confirmed, immediate steps should include:
- Conducting a full security audit
- Notifying affected users
- Revoking compromised credentials
- Strengthening infrastructure
- Partnering with cybersecurity experts
Transparency and swift action are key to minimizing damage and restoring trust.
Conclusion
The alleged Koiride data breach serves as a powerful reminder of the importance of cybersecurity in data-driven industries. With millions of records potentially exposed, the incident highlights the urgent need for data breach detection, robust dark web solutions, and stronger retail cybersecurity practices. Organizations must act proactively to safeguard their systems and protect user data from evolving threats ⚠️.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

