➤Summary
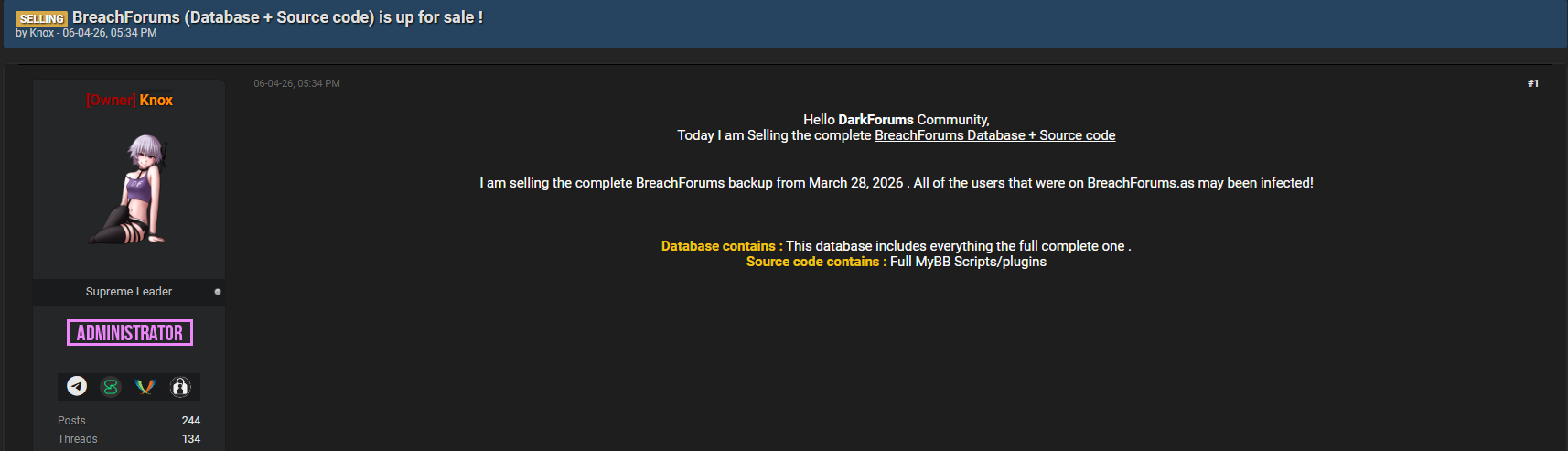
Dark web surveillance is once again in the spotlight after reports that a figure known as Knox is allegedly selling a complete backup of BreachForums dated March 28, 2026. This incident has sparked serious concerns across the cybersecurity community, as BreachForums has historically been one of the most notorious hubs for leaked databases, stolen credentials, and cybercriminal collaboration.
The potential exposure of such a massive dataset could have far-reaching consequences for individuals and enterprises alike. From identity theft monitoring challenges to the growing demand for an affordable dark web monitoring service, the implications are significant. In this darknetsearch.com article, we break down what this leak means, how hacker marketplace monitoring plays a role, and how you can check if your data is on the dark web before it’s too late 🔍.
What Happened: The Alleged BreachForums Backup Sale
Reports suggest that Knox, the alleged owner of DarkForums, is offering a full database backup of BreachForums. This includes:
- User accounts and credentials
- Private messages between members
- Marketplace listings
- Potentially sensitive leaked data archives
BreachForums has long been associated with high-profile leaks, making this backup extremely valuable in cybercriminal circles. If verified, this dataset could provide unprecedented insight into hacker operations and expose millions of users.
According to cybersecurity discussions, such backups are often sold on underground forums or through private channels, making hacker marketplace monitoring essential for early detection.
Why This Leak Matters More Than Others
Not all breaches are equal—and this one stands out.
Here’s why:
- BreachForums was a central hub for cybercrime activity
- It contains aggregated data from multiple breaches
- It may include both victims and threat actors
- The scale could impact global users 🌍
This means the risk is not limited to a single company or region. Anyone whose data was ever shared or traded on BreachForums could be affected.
For individuals wondering how to check if my data is on the dark web, this incident highlights the urgency of proactive monitoring.
The Role of Hacker Marketplace Monitoring
Hacker marketplace monitoring is a critical component of modern cybersecurity. It involves tracking underground platforms where stolen data is bought and sold.
In this case, monitoring tools can:
- Detect listings of the BreachForums backup
- Identify data exposure early
- Alert affected users or organizations
- Provide intelligence on threat actors
Platforms like Darknetsearch.com help organizations perform real-time monitoring of these environments ⚠️.
How Cybercriminals Exploit Leaked Data
Once a dataset like this is released, it doesn’t stay in one place.
Cybercriminals use it for:
- Identity theft monitoring evasion
- Credential stuffing attacks
- Phishing campaigns
- Financial fraud
- Social engineering operations 🎯
This creates a ripple effect where one leak leads to multiple attack vectors.
An expert from Cybersecurity and Infrastructure Security Agency warns: “Data aggregation significantly increases the impact of breaches, amplifying downstream risks.”
How to Check If Your Data Is on the Dark Web
One of the most common questions people ask is:
How to check if my data is on the dark web?
Here’s a clear answer:
You need a combination of automated tools and dark web surveillance solutions.
Quick Checklist:
✔ Use an affordable dark web monitoring service
✔ Enable identity theft monitoring alerts
✔ Scan email addresses across breach databases
✔ Monitor hacker forums and marketplaces
✔ Set up real-time alerts for new exposures
Services like https://darknetsearch.com/provide actionable insights and alerts when your data appears in underground markets 🔔.
Practical Tip: Strengthen Your Defense Strategy
A single tool is not enough. You need a layered approach.
Best Practices:
- Combine dark web surveillance with identity theft monitoring
- Use strong, unique passwords
- Enable multi-factor authentication
- Regularly audit your digital footprint
- Invest in hacker marketplace monitoring solutions
This proactive strategy significantly reduces your exposure risk 🛡️.
The Rise of Affordable Dark Web Monitoring Services
As threats grow, so does the demand for accessible solutions.
Affordable dark web monitoring services are now available for both individuals and enterprises, making it easier to:
- Detect data leaks early
- Monitor underground activity
- Protect sensitive information
These services are no longer a luxury—they are a necessity in today’s threat landscape.
Can You Prevent Identity Theft After a Leak?
Short answer: Yes, but only with fast action.
While you cannot undo a leak, you can minimize damage by:
- Activating identity theft monitoring immediately
- Changing compromised credentials
- Monitoring financial accounts
- Using dark web surveillance tools
The faster you act, the lower the risk of long-term consequences.
The Bigger Picture: A Growing Cybercrime Ecosystem
The alleged sale of the BreachForums backup by Knox highlights a broader issue: the professionalization of cybercrime.
Today’s threat actors operate like businesses, with:
- Structured marketplaces
- Customer support systems
- Subscription-based data access 💼
This evolution makes hacker marketplace monitoring and brand protection more critical than ever.
Conclusion: Act Before It’s Too Late
Dark web surveillance is no longer optional—it’s essential. The potential exposure from the BreachForums backup could impact millions, making proactive defense strategies critical.
By investing in identity theft monitoring, using an affordable dark web monitoring service, and leveraging hacker marketplace monitoring, you can stay ahead of threats and protect your digital identity.
👉 Discover much more in our complete guide
👉 Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

