➤Summary
The Credilink data breach has surfaced as a major cybersecurity discussion following claims posted on underground forums alleging that hundreds of millions of Brazilian citizen records were exposed online. According to a threat actor using the alias Blastoize, a dataset linked to credilink.com.br containing approximately 243 million records was published on March 21, 2026, on Darkforums.su. While the breach remains unconfirmed at the time of writing, early analysis suggests the dataset may contain extensive personally identifiable information (PII), financial indicators, and demographic attributes.
If validated, this alleged data exposure would rank among the largest Brazilian data leaks ever reported, raising serious concerns about identity theft, fraud risks, and large-scale privacy violations. Cybersecurity researchers and threat intelligence analysts are closely monitoring the situation as organizations assess potential impact and verification efforts continue. 🔎
Overview of the Alleged Incident
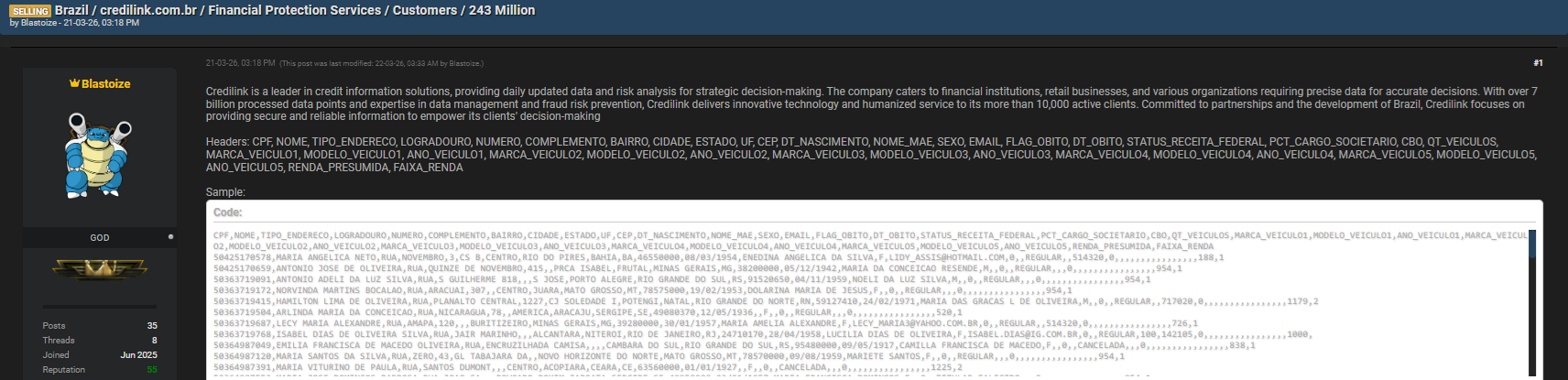
The alleged Credilink data breach was first advertised on Darkforums.su, a well-known cybercrime forum used for trading stolen databases and sharing breach announcements. The actor “Blastoize” claimed possession of a massive dataset tied to Brazilian individuals and financial profiling information.
Key reported details:
- Forum: Darkforums.su
- Threat Actor: Blastoize
- Publication Date: March 21, 2026
- Affected Records: 243 million entries
- Status: Alleged / Under investigation
Unlike ransomware disclosures, this case appears structured as a database leak listing extensive citizen-level attributes rather than corporate internal documents. Analysts caution that underground forum claims should always be independently verified before conclusions are drawn. ⚠️
What Data Was Allegedly Compromised
Researchers reviewing shared samples report that the dataset includes structured database headers translated into English below for clarity:
| Original Field | English Translation |
| CPF | National Taxpayer ID |
| NOME | Full Name |
| TIPO_ENDERECO | Address Type |
| LOGRADOURO | Street |
| NUMERO | Address Number |
| COMPLEMENTO | Address Complement |
| BAIRRO | Neighborhood |
| CIDADE | City |
| ESTADO / UF | State |
| CEP | Postal Code |
| DT_NASCIMENTO | Date of Birth |
| NOME_MAE | Mother’s Name |
| SEXO | Gender |
| Email Address | |
| FLAG_OBITO | Deceased Indicator |
| DT_OBITO | Date of Death |
| STATUS_RECEITA_FEDERAL | Federal Tax Status |
| PCT_CARGO_SOCIETARIO | Corporate Participation |
| CBO | Occupation Code |
| QT_VEICULOS | Number of Vehicles |
| MARCA/MODELO/ANO (1–5) | Vehicle Brand, Model, Year |
| RENDA_PRESUMIDA | Estimated Income |
| FAIXA_RENDA | Income Range |
The breadth of this information suggests potential aggregation from multiple sources rather than a single application database. Exposure of identifiers like CPF combined with address and income indicators dramatically increases fraud risks. 📊
Why This Alleged Leak Is Significant
Large-scale breaches involving national identity datasets create long-term consequences because personal data cannot be easily changed. Unlike passwords, identifiers such as CPF numbers remain permanent.
Security experts highlight three primary concerns:
- Identity theft and synthetic identity creation.
- Financial fraud using income and demographic profiling.
- Targeted phishing campaigns leveraging accurate personal details.
The inclusion of vehicle ownership and socioeconomic indicators may allow attackers to craft highly personalized scams, increasing success rates compared to generic phishing attempts.
How Cybercriminal Forums Amplify Data Breaches
Dark web and underground communities play a central role in modern breach dissemination. Forums like Darkforums.su enable threat actors to:
- Sell databases to fraud groups
- Build reputation through leak publications
- Exchange verification samples
- Recruit collaborators
Threat intelligence platforms often monitor these environments to identify emerging risks early. 🌐
Verification Challenges: Alleged vs Confirmed Breaches
One critical question arises: How can organizations tell whether a breach claim is real?
The answer lies in technical validation. Analysts typically evaluate:
- Sample authenticity and structure
- Data freshness indicators
- Cross-referencing known datasets
- Metadata consistency
- Unique record patterns
At present, the Credilink data breach remains classified as alleged, meaning attribution and origin are not yet officially confirmed. Responsible reporting requires distinguishing between claims and verified incidents to avoid misinformation.
Potential Impact on Brazilian Users
If confirmed, the exposure could affect a large percentage of Brazil’s population. The dataset’s scope suggests broad demographic coverage rather than a niche customer base.
Possible impacts include:
- Unauthorized loan applications
- Account takeover attempts
- Insurance fraud
- SIM swap attacks
- Social engineering scams
Brazil has previously experienced large-scale leaks involving CPF data, making cumulative exposure an ongoing concern for privacy advocates. 🛡️
Detection and Threat Intelligence Perspective
Threat intelligence analysts emphasize proactive monitoring rather than reactive response. Continuous surveillance of underground forums allows organizations to identify emerging risks before exploitation escalates.
An authoritative overview of breach trends can be explored via the external cybersecurity resource from IBM’s security research hub: https://www.ibm.com/security/data-breach , which explains how exposed datasets evolve into fraud campaigns.
Modern monitoring systems correlate forum posts, leaked samples, and infrastructure indicators to assess credibility and urgency levels.
Practical Checklist: What Organizations Should Do Now
Organizations potentially affected should implement the following actions immediately:
✔ Conduct internal data exposure assessments
✔ Monitor credential leaks across dark web sources
✔ Notify legal and compliance teams
✔ Strengthen identity verification procedures
✔ Deploy fraud detection monitoring
✔ Educate customers about phishing risks
✔ Review third-party data-sharing practices
These steps reduce damage even before confirmation occurs.
Practical Tip for Individuals
Individuals concerned about exposure should:
- Monitor financial statements regularly
- Enable multi-factor authentication
- Avoid sharing CPF numbers unnecessarily
- Watch for targeted scam emails referencing personal details
Early vigilance significantly reduces fraud success rates. 🔐
Expert Insight
A senior threat intelligence analyst noted:
“Massive datasets become dangerous not just because they exist, but because criminals combine them with automation and AI-driven fraud techniques.”
This observation reflects a broader cybersecurity shift toward data-driven attacks rather than traditional hacking alone.
Broader Implications for Data Privacy
The alleged Credilink data breach highlights systemic risks associated with centralized data aggregation. Organizations managing identity and financial data must maintain strict governance and auditing processes.
Regulatory frameworks increasingly emphasize accountability, but enforcement challenges remain when data circulates across underground markets. The incident also underscores the importance of continuous monitoring services like those discussed at different threat intelligence solutions which help detect early signs of exposure.
Long-Term Security Lessons
Whether confirmed or disproven, incidents like this reinforce key lessons:
- Data minimization reduces breach impact.
- Monitoring underground forums is essential.
- Transparency builds user trust.
- Rapid response limits reputational damage.
Cybersecurity today extends beyond perimeter defense into intelligence-driven awareness.
Conclusion: Why Continuous Monitoring Matters
The alleged Credilink data breach demonstrates how quickly massive datasets can appear within cybercriminal ecosystems and spark global concern. Even without confirmation, the scale of the claim—243 million records—illustrates the growing industrialization of data leaks and identity exploitation.
Organizations and individuals must treat breach intelligence as an early warning signal rather than a post-incident report. Continuous monitoring, verification workflows, and user education remain essential pillars of modern cybersecurity resilience. 🚨
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

