➤Summary
The CIMB Bank data leak allegedly posted on an underground cybercrime forum has sparked serious concerns across Southeast Asia’s banking ecosystem. On March 2, 2026, a Breachforums.as user known as datasource claimed to be selling a database containing approximately 1,200,000 customer records tied to CIMB Bank Malaysia. While official confirmation has not yet been publicly issued, the listing highlights growing threats facing digital banking infrastructures worldwide. Financial institutions increasingly rely on online systems storing vast amounts of personal and transactional information, making them prime targets for cybercriminal groups. The alleged exposure demonstrates how quickly sensitive financial datasets can surface within underground markets and why early data breach detection mechanisms are essential to reduce potential damage. ⚠️
Overview of the Alleged Incident
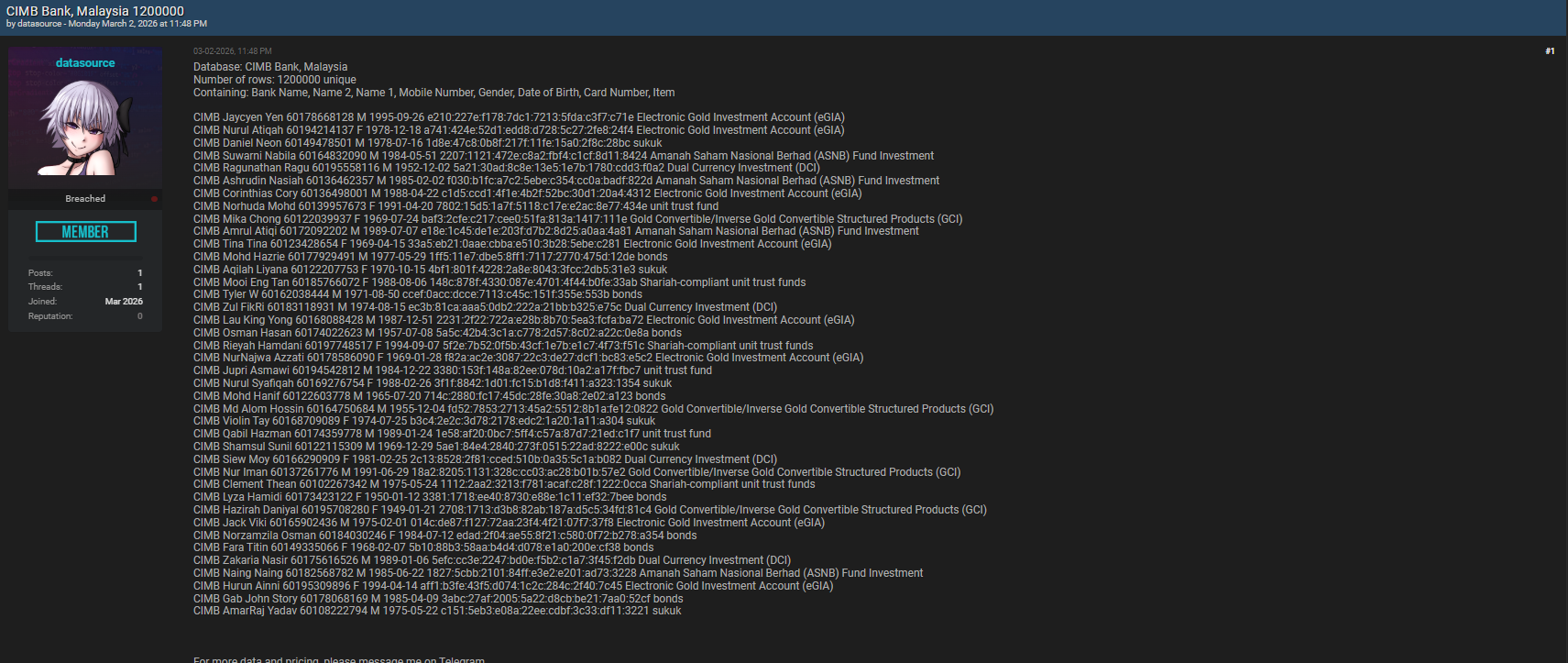
According to the forum listing, the dataset allegedly originates from CIMB Bank Malaysia and includes structured customer information extracted from internal systems. The seller published sample fields and offered access to the full database, suggesting monetization through private negotiations.
The post states the compromised dataset contains:
- Bank Name
- Name 1 (First Name)
- Name 2 (Additional Name)
- Mobile Number
- Gender
- Date of Birth
- Card Number
- Item (record classification)
If verified, this information represents highly sensitive personally identifiable and financial data. Such records are particularly valuable within cybercrime ecosystems because they enable identity verification bypasses and targeted fraud campaigns. Analysts using dark web intelligence techniques often treat these listings as early indicators of potential institutional compromise. 💻
Why Banking Data Is Highly Valuable to Attackers
Financial institutions remain among the most targeted sectors globally. Unlike general consumer databases, banking datasets combine identity details with payment-related information, dramatically increasing resale value.
Attackers seek financial records for several reasons:
- Direct financial fraud opportunities
- Account takeover attempts
- Phishing personalization
- Synthetic identity creation
- Long-term resale in underground markets
The alleged CIMB Bank data leak reflects a broader shift where attackers prioritize verified banking identities over passwords alone. A single validated record may circulate across multiple criminal marketplaces for years.
According to cybersecurity guidance published by the World Economic Forum, financial services organizations face some of the highest cyberattack rates due to digital transformation and interconnected systems.
Understanding the Data Structure and Risks
Below is a simplified breakdown of the allegedly compromised dataset and associated risks:
| Data Field | Risk Level | Potential Abuse |
| Full Name | High | Identity impersonation |
| Mobile Number | High | SIM swapping attacks |
| Date of Birth | High | Verification bypass |
| Card Number | Critical | Payment fraud |
| Gender | Medium | Profile enrichment |
| Bank Name | Medium | Targeted scams |
| When multiple identifiers appear together, attackers can reconstruct complete digital identities. This significantly increases phishing success rates and financial fraud probability. | ||
| Security researchers frequently observe that banking leaks quickly transition from private sale to mass exploitation once buyers validate authenticity. |
The Growing Threat to Financial Institutions
Cyberattacks targeting banks have evolved beyond ransomware or system disruption. Today’s attackers focus heavily on silent data extraction.
The financial sector cybersecurity landscape faces several persistent challenges:
- Legacy infrastructure integration
- Third-party vendor risks
- API vulnerabilities
- Insider threat exposure
- Delayed patch management
A single exposed dataset can undermine customer trust more severely than operational downtime. Trust remains the core currency of banking institutions, making reputational damage a major consequence. 🔐
How Underground Forums Accelerate Cybercrime
Cybercrime forums like Breachforums.as function as marketplaces connecting sellers and buyers of stolen data. Listings typically follow a predictable lifecycle:
- Initial teaser post
- Sample data release
- Private buyer negotiations
- Bulk resale distribution
- Public leak escalation
Organizations monitoring underground environments through a darkweb monitoring platform can detect references to their brand early and respond before widespread exploitation occurs.
Proactive monitoring solutions help identify leaked assets and compromised credentials circulating in hidden networks.
Question: Does a Leak Listing Guarantee the Data Is Real?
Short answer: No, but it must always be treated seriously.
Some sellers exaggerate claims to attract buyers. However, many high-profile breaches first appeared on underground forums before confirmation. Security teams therefore investigate every credible listing as a potential incident until proven otherwise.
Cybersecurity analysts recommend immediate verification steps once a listing references institutional data assets. 🧠
Practical Checklist for Incident Response
Organizations facing potential exposure should follow this response checklist:
✅ Validate sample data authenticity
✅ Audit access logs and database activity
✅ Rotate authentication credentials
✅ Notify internal cybersecurity teams
✅ Begin forensic investigation
✅ Monitor fraud indicators across customer accounts
Early containment significantly reduces downstream financial losses and regulatory consequences.
Role of Continuous Monitoring and Intelligence
Modern cybersecurity no longer relies solely on perimeter defense. Continuous intelligence gathering across underground ecosystems provides critical early warnings.
Institutions adopting proactive monitoring approaches benefit from:
- Faster breach discovery
- Reduced response time
- Improved regulatory compliance
- Enhanced customer protection
Platforms integrating external intelligence feeds — like insights discussed on https://darknetsearch.com/solutions — allow banks to detect exposure indicators before attackers weaponize stolen information.
Additionally, combining monitoring with automated alerts improves visibility across evolving threat landscapes.
Broader Implications for the Banking Industry
The alleged CIMB Bank data leak illustrates systemic risks affecting digital banking worldwide:
- Increased dependence on online services
- Expanding customer data repositories
- Sophisticated cybercriminal economies
- Rising regulatory expectations
Financial regulators globally now emphasize proactive threat intelligence as a mandatory capability rather than an optional enhancement.
A cybersecurity expert from IBM Security once noted:
“The speed of detection often determines the true cost of a breach.”
This reinforces why prevention alone is insufficient without continuous visibility into external threat environments.
Practical Tips for Customers
If banking data exposure is suspected, individuals should take precautionary actions:
- Monitor bank statements daily
- Enable transaction alerts
- Avoid unknown SMS links
- Change online banking passwords
- Contact the bank immediately if suspicious activity appears
Consumers play a critical role in minimizing fraud impact after potential incidents. 📱
Long-Term Cybersecurity Lessons
Even without official confirmation, the reported incident demonstrates several enduring cybersecurity lessons:
- Sensitive data must be encrypted at rest and in transit
- Continuous monitoring is essential
- Threat intelligence shortens response time
- Transparency strengthens public trust
Organizations adopting proactive risk management models consistently experience lower breach impact compared to reactive approaches.
Conclusion: Why This Alleged Leak Matters
The alleged CIMB Bank data leak involving 1.2 million records underscores how rapidly sensitive financial data can enter cybercriminal markets. Whether ultimately verified or disproven, the listing highlights the growing sophistication of attackers targeting banking infrastructures.
Financial institutions must evolve from reactive security toward intelligence-driven defense models capable of identifying risks beyond organizational boundaries. Continuous monitoring, rapid investigation, and proactive protection strategies are now fundamental requirements for safeguarding customer trust. 🚨
As cyber threats continue evolving, organizations that prioritize visibility and preparedness will remain resilient in an increasingly hostile digital landscape.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

