➤Summary
Cashea App data leak has sent shockwaves across Venezuela’s fintech ecosystem after confidential records allegedly surfaced on underground forums in February 2026. According to posts attributed to malconguerra2 on BreachForums, the incident involves one of the largest exposures of financial and transactional data in the country to date 🚨. The breach reportedly affects users, merchants, and internal store records tied to the popular buy-now-pay-later platform operated by Cashea App. With more than 79 million transaction history records allegedly compromised, this Venezuela data breach raises urgent questions about data protection, regulatory oversight, and user safety. Below, we break down what happened, what data was exposed, and why this Cashea App data leak matters far beyond the dark corners of cybercrime forums.
What Happened in the Cashea App Data Leak
The Cashea App data leak was allegedly disclosed on BreachForums, a well-known cybercrime marketplace, where a database dump was advertised as coming directly from Cashea’s systems. The breached date is listed as 21.02.2026, with the content shared in JSON format and a compressed size of 46.5 GB 💾. This Venezuela data breach includes store configurations, merchant profiles, and detailed transaction histories, making it particularly sensitive.

While Cashea has not publicly confirmed the incident at the time of writing, the scale alone places this Cashea App data leak among the most severe fintech exposures in Latin America.
Scope of the Compromised Data
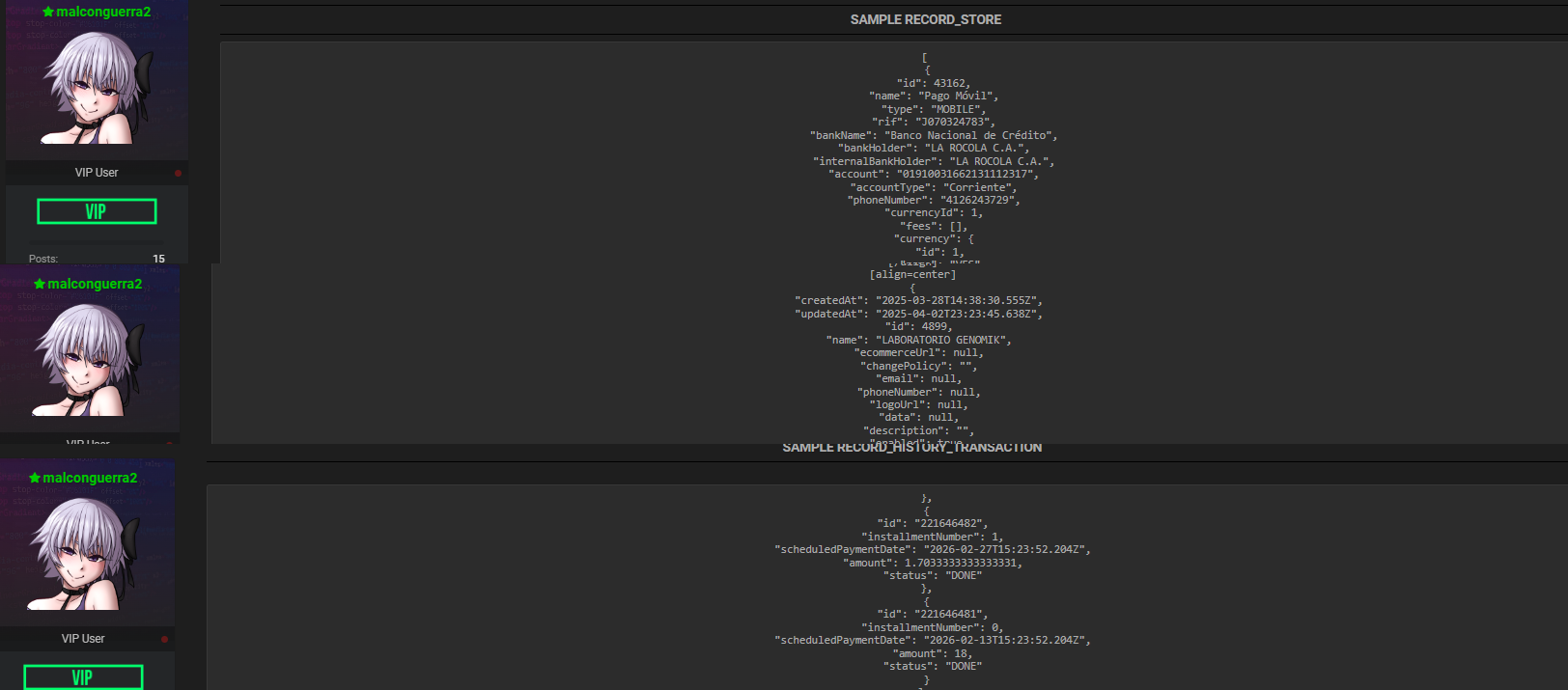
Based on sample records shared by the threat actor, the Cashea App data leak includes multiple structured datasets:
- RECORDS_STORE: 29.7 million entries containing bank details, account numbers, phone numbers, and payment methods.
- RECORDS_MERCHANTS: 15,227 merchant profiles with business identifiers, operating hours, and internal IDs.
- RECORDS_HISTORY_TRANSACTION: 79,006,942 transaction logs detailing amounts, dates, installment plans, and partial user identities 📊.
The presence of names, identification numbers, and phone data significantly increases the risk of fraud and identity abuse linked to this Venezuela data breach.
Real Examples From the Leaked Records
Sample data attributed to the Cashea App data leak shows merchant entities such as LABORATORIO GENOMIK and banking references to Banco Nacional de Crédito, including account numbers and mobile payment details. Transaction history samples include full names, national ID numbers, and precise timestamps of purchases and installment payments. This level of detail answers a critical question: Is the data exploitable? Yes—the leaked structure is clean, recent, and highly actionable for cybercriminals.
Why This Venezuela Data Breach Is So Dangerous
This Venezuela data breach is not just about volume; it’s about context. Financial transaction histories combined with personal identifiers enable phishing, SIM swapping, and targeted scams 🎯. When such datasets circulate via dark web monitoring platforms, they are often resold, enriched, and weaponized. Analysts using dark web intelligence have already flagged increased chatter around Venezuelan fintech credentials, suggesting the Cashea App data leak could have long-term ripple effects across banks, merchants, and consumers.
Checklist: How Users and Businesses Can Reduce Risk
Practical Tip – Immediate actions after a fintech breach:
- Change passwords and enable multi-factor authentication wherever possible.
- Monitor bank statements and installment plans for unauthorized activity.
- Be skeptical of payment-related calls or messages, even if they reference real transactions 📱.
- Businesses should rotate API keys and audit third-party integrations.
- Consider professional dark web solutions to detect if your data is being traded.
These steps won’t undo the Cashea App data leak, but they can significantly reduce damage.
Industry Context and Expert Insight
Cybersecurity researchers often note that fintech platforms in emerging markets are prime targets due to rapid growth and uneven security maturity. As reported by Krebs on Security, large transactional datasets are among the most valuable commodities in cybercrime because they enable repeatable fraud at scale. This perspective helps explain why the Cashea App data leak is drawing so much attention within the security community.
Learn More and Stay Protected
For ongoing updates about breaches like this Venezuela data breach, explore in-depth investigations and resources in different dark web monitoring platforms 🔍. Understanding how incidents like the Cashea App data leak unfold is the first step toward protecting your digital footprint in an increasingly hostile threat landscape.
Conclusion and Call to Action
The Cashea App data leak underscores how a single breach can expose millions to financial and identity risks overnight. Whether you are a user, merchant, or security professional, staying informed is no longer optional—it’s essential. Discover much more in our complete guide and Request a demo NOW to see how proactive monitoring can help you stay one step ahead of the next major leak 🔐.
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

