➤Summary
Bahrain NSA data breach allegations emerged on February 24, 2026, after a high-profile post appeared on an underground cybercrime forum claiming a massive compromise tied to Bahrain’s intelligence infrastructure. According to the listing, an alleged database belonging to the Bahrain National Security Agency was offered for sale, with a reported size of roughly 200 GB and a price tag of $2,500 worth of cryptocurrency. Claims of this magnitude immediately raise red flags for national security experts, journalists, and cybersecurity analysts alike. Government-linked data breaches differ significantly from commercial leaks due to their potential geopolitical intelligence, and human rights implications. While no official confirmation has been released, the seriousness of the allegations has already triggered widespread discussion across threat intelligence communities. This darknetsearch.com article examines what is currently known, why this alleged breach matters, and how it fits into broader cyber-espionage trends 🌍
What Is Allegedly Known About the Incident
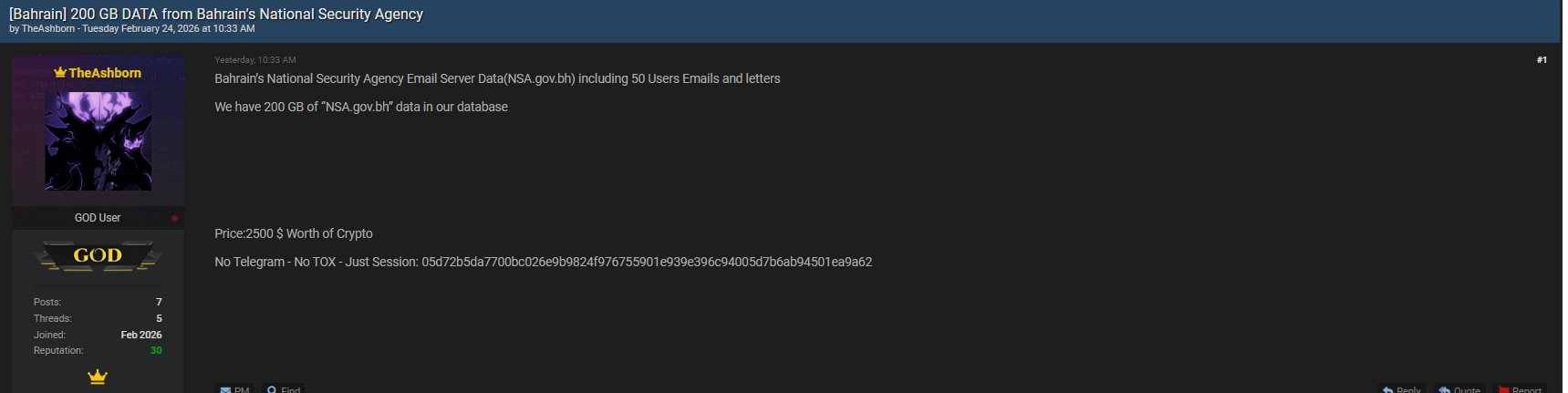
The alleged Bahrain NSA data breach was published on breachforums.as by a user operating under the alias “TheAshborn.” The post appeared on February 24, 2026, and described a database allegedly extracted from internal systems linked to Bahrain’s national security apparatus. According to the seller, the dataset totals approximately 200 GB and was offered as a single private sale for $2,500 in cryptocurrency 💰
The forum used for publication, BreachForums, is known for hosting claims involving government, corporate, and critical infrastructure leaks. While not every listing proves authentic, intelligence professionals often treat government-related disclosures with heightened caution due to their potential consequences.
The absence of a public data sample suggests an attempt to limit exposure while maximizing value.
Data Volume and Alleged Content Overview
Based on the forum description and subsequent analysis by breach monitoring platforms, the alleged Bahrain National Security Agency leak reportedly includes a wide range of sensitive materials. While full verification is still pending, descriptions indicate the data may involve internal documents, operational records, and other restricted materials. The reported size alone places this incident among larger alleged government leaks in the region 📊
A third-party breach tracking report published by HackNotice further amplified awareness of the case, noting that intelligence-related datasets often contain layered information that can remain valuable for years. You can review the contextual report here:
Timeline of the Alleged Leak
Understanding the timeline is critical when evaluating an alleged Bahrain NSA data breach. According to available information, the dataset was posted for sale on February 24, 2026. There were no prior public disclosures or warnings, which is typical for intelligence-related leaks that surface suddenly rather than through coordinated disclosures 🕵️
The seller did not specify the breach method, such as insider access or external intrusion. Historically, similar cases in the Middle East have involved a mix of credential compromise, insider threats, or misconfigured systems. Analysts caution that timeline clarity often improves only after official investigations begin or media inquiries escalate.
Why Intelligence Agency Data Is Highly Sensitive
Government and intelligence agency data differs from commercial datasets in both value and risk. In the context of the Bahrain NSA data breach, the alleged exposure could carry national security, diplomatic, and personal safety implications. Intelligence records may include operational procedures, surveillance methodologies, or internal communications that adversaries could exploit 🧠
Unlike consumer breaches, where financial fraud is the primary concern, intelligence leaks can have long-term strategic consequences. Even partial datasets can be cross-referenced with other leaks to build detailed intelligence profiles. This is why such allegations are closely monitored by international cybersecurity observers.
Who Could Be Impacted by This Alleged Breach
If confirmed, the Bahrain National Security Agency leak could impact multiple categories of individuals and institutions. Potentially affected parties may include government employees, contractors, foreign partners, and individuals referenced within internal records. Even indirect exposure can place people at risk depending on the nature of the information involved ⚠️
A common question arises in cases like this:
Does an alleged intelligence data breach mean immediate danger?
Not necessarily. Risk depends on what data was accessed, who obtains it, and how it is used. However, intelligence-related data always carries elevated long-term risk, even without immediate misuse.
Underground Forums and State-Level Breach Claims
Forums such as breachforums.as play a significant role in surfacing alleged incidents like the Bahrain NSA data breach. While these platforms are illegal, they function as early warning systems for researchers tracking emerging cyber threats. Claims involving state institutions are typically scrutinized more heavily due to their implications 🌐
Threat intelligence platforms and researchers often cross-check such listings with historical activity patterns, seller reputation, and metadata clues. Coverage and analysis from monitoring sites like darknetsearch.com help contextualize whether a listing aligns with known breach behaviors.
Price, Motivation, and Cybercrime Economics
The reported price of $2,500 in cryptocurrency is relatively modest given the alleged size and sensitivity of the dataset. Analysts suggest that pricing in intelligence-related cases does not always reflect true value but rather speed of sale or limited buyer targeting 💸
In some cases, sellers aim for fast transactions to avoid detection. In others, pricing is symbolic, intended to prove access rather than maximize profit. Understanding these dynamics is key when evaluating the credibility of the alleged Bahrain NSA data breach.
Practical Checklist for Analysts and Organizations
For journalists, researchers, or organizations monitoring this situation, a structured approach is essential:
• Track official statements from Bahraini authorities
• Monitor trusted breach intelligence platforms
• Avoid redistributing unverified data
• Cross-reference seller history and forum activity
• Follow updates from cybersecurity analysis sites
This checklist helps reduce misinformation while maintaining situational awareness 🛡️ Resources such as https://darknetsearch.com/ frequently publish updates on similar high-risk disclosures.
How This Fits Regional Cybersecurity Trends
The alleged Bahrain National Security Agency leak aligns with a broader rise in cyber incidents affecting government institutions worldwide. Over the past decade, intelligence agencies have increasingly become targets of both criminal and politically motivated actors. Digital transformation has expanded attack surfaces faster than security controls in many regions 📈
From an analytical standpoint, this case reflects growing convergence between cybercrime marketplaces and geopolitical cyber operations. Monitoring these intersections is now a core function of modern threat intelligence teams.
Conclusion and What to Watch Next
The alleged Bahrain NSA data breach represents a serious claim with potentially far-reaching implications. While verification is still pending, the reported scale, pricing, and platform of disclosure warrant close attention from cybersecurity professionals, policymakers, and media observers alike. Remaining cautious, informed, and analytical is essential as new details emerge 📌
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

