➤Summary
Healthcare data breach detection has become increasingly critical following reports of an alleged database leak connected to Hong Kong’s www.ha.org.hk, the official website of the Hospital Authority. According to information circulating on underground cybercrime forums, sensitive healthcare-related data may have been exposed and shared publicly on the dark web. The incident highlights how medical institutions remain prime targets for cybercriminals seeking valuable personal and identity records.
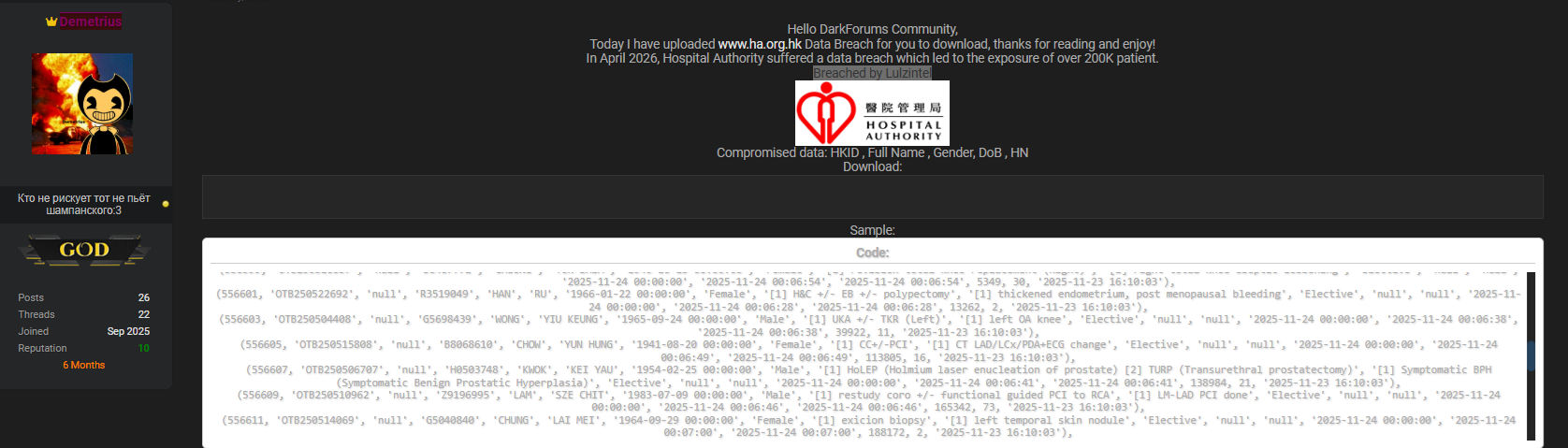
The dataset was reportedly posted on Darkforums.su by a threat actor using the alias Demetrius, with a publication date of 02 April 2026, and allegedly attributed to a group known as Lulzintel. If verified, the exposure could represent a serious privacy concern due to the sensitivity of healthcare identifiers and personal records 🏥. The event also reinforces the growing importance of dark web monitoring for businesses and proactive threat intelligence powered by a reliable dark search engine.
Overview of the Alleged HA.org.hk Leak
Early reports suggest that the exposed dataset contains highly sensitive personal details typically associated with healthcare registration systems. The compromised information allegedly includes:
| Data Field | Description |
| HKID | Hong Kong Identity Card number |
| Full Name | Patient identification details |
| Gender | Personal demographic data |
| Date of Birth (DoB) | Identity verification element |
| HN | Hospital Number or patient reference |
| Healthcare databases are particularly valuable to attackers because they combine identity, demographic, and institutional identifiers in a single record. Unlike passwords, medical identifiers cannot easily be changed, making breaches long-lasting in impact. |
| Cybersecurity analysts emphasize that healthcare-related datasets frequently appear in underground markets where identity fraud actors aggregate records for resale. Using a dark search engine, researchers often trace such postings back to forums like Darkforums.su, where leaked material circulates among threat communities 🔎. |
Why Healthcare Databases Are Prime Targets
Medical organizations hold some of the most comprehensive personal datasets in existence. A single patient record may include identifiers sufficient for identity theft, insurance fraud, or targeted phishing campaigns.
Healthcare breaches differ from traditional corporate incidents because:
- Data remains valid for years or decades.
- Patients cannot replace identity numbers easily.
- Records enable social engineering attacks.
- Trust in healthcare institutions amplifies attacker success rates.
This explains why healthcare data breach detection systems are now a priority for hospitals worldwide. SecurityWeek and global cybersecurity bodies consistently report healthcare as one of the most attacked sectors due to its operational urgency and legacy infrastructure.
When attackers obtain identity-linked data, they often combine it with publicly available information to create convincing impersonation schemes. Businesses supporting healthcare ecosystems increasingly rely on dark web monitoring for businesses to identify exposures before exploitation spreads ⚠️.
The Role of Dark Web Forums in Data Distribution
Darkforums.su, where the alleged dataset appeared, represents a typical marketplace-style forum used by cybercriminals. Threat actors publish sample records, negotiate access, or distribute databases freely to gain reputation within underground communities.
A dark search engine allows analysts to scan hidden services, onion sites, and closed forums for keywords related to leaked organizations or datasets. These tools significantly improve incident response timelines by detecting exposures early.
Organizations leveraging platforms such as https://darknetsearch.com/ gain visibility into hidden online environments where conventional search engines cannot operate. This type of monitoring helps cybersecurity teams identify early indicators of compromise before breaches escalate into public crises 💻.
Modern dark web monitoring for businesses combines automated crawling, threat intelligence analysis, and behavioral tracking to identify threat actors distributing stolen datasets.
Potential Risks Associated With the Exposed Data
If the alleged leak proves authentic, several risks may arise:
- Identity theft using HKID numbers
- Medical fraud or insurance abuse
- Targeted phishing against patients
- Social engineering attacks against healthcare staff
- Credential stuffing using correlated datasets
Healthcare records are uniquely dangerous because attackers can impersonate both patients and institutions simultaneously.
According to guidance from the U.S. Department of Health & Human Services cybersecurity resources healthcare organizations must implement continuous monitoring and rapid breach response strategies to reduce exposure risks.
The presence of hospital identifiers like HN numbers suggests attackers could attempt system-specific impersonation campaigns targeting medical communication channels 📊.
How Healthcare Data Breach Detection Works
Healthcare data breach detection involves identifying unauthorized exposure of patient information across open internet sources and hidden networks.
Key detection components include:
- Automated scanning using a dark search engine
- Data pattern recognition for medical identifiers
- Monitoring underground forums and marketplaces
- Threat actor attribution tracking
- Real-time alerting systems
These systems analyze leaked datasets to verify authenticity and determine scope. Advanced platforms also correlate breach data with known cybercrime campaigns.
Organizations integrating healthcare data breach detection into their security operations gain earlier warning signals, enabling faster containment and notification procedures.
Question: Does an Alleged Leak Mean a Confirmed Breach?
Question: Does a database appearing on a dark web forum confirm that a healthcare organization was hacked?
Answer: No. A listing alone does not confirm authenticity. Data may originate from older leaks, third-party systems, or fabricated samples. Verification requires forensic investigation and official confirmation.
Security experts stress cautious interpretation until validated evidence emerges. However, early monitoring remains essential because attackers often exploit publicity regardless of authenticity 🌐.
Practical Checklist for Healthcare Organizations
Healthcare entities and partners can strengthen resilience using this checklist ✅:
- Deploy dark web monitoring for businesses continuously.
- Monitor forums using a dark search engine.
- Encrypt patient identifiers at rest and in transit.
- Implement strict access controls for medical databases.
- Conduct regular vulnerability assessments.
- Train staff against phishing and impersonation attempts.
- Establish incident response workflows.
- Monitor third-party vendors handling healthcare data.
These measures reduce exposure windows and improve response readiness following suspected leaks.
Broader Industry Impact and Lessons Learned
The alleged HA.org.hk incident illustrates a wider trend: healthcare organizations are increasingly targeted due to data richness and operational dependency on digital systems.
Attackers understand that hospitals prioritize patient care, which sometimes delays security patching or infrastructure upgrades. As a result, threat actors exploit vulnerabilities faster than organizations can respond.
Cybersecurity specialists increasingly advocate layered defenses combining endpoint security, identity protection, and continuous dark web monitoring for businesses. Integrating these controls creates visibility across both internal networks and external threat landscapes 🚨.
Platforms such as Darknetsearch.com enable organizations to detect leaked credentials, track threat actor discussions, and analyze emerging risks tied to healthcare ecosystems.
Expert Insight: Why Healthcare Breaches Have Long-Term Consequences
A cybersecurity analyst summarized the issue:
“Healthcare breaches are not short-term events; they create identity risks lasting decades.”
Unlike financial breaches, medical data exposure cannot simply be reset. Patient trust, regulatory compliance, and institutional reputation remain affected long after disclosure.
Healthcare data breach detection therefore shifts security strategy from reactive cleanup toward predictive intelligence models that identify threats before harm occurs 🔐.
Conclusion: Proactive Monitoring Is the New Healthcare Security Standard
The alleged HA.org.hk database leak demonstrates how sensitive healthcare information continues to attract cybercriminal attention across dark web forums. Whether confirmed or still under investigation, such incidents reinforce the importance of proactive monitoring, rapid verification, and continuous threat intelligence.
Organizations that adopt healthcare data breach detection alongside dark web monitoring for businesses gain critical visibility into hidden threat ecosystems. Leveraging a powerful dark search engine enables earlier detection of leaked datasets and reduces the likelihood of large-scale exploitation.
Healthcare cybersecurity is no longer limited to firewalls and compliance checklists—it requires active intelligence gathering beyond the visible internet. Institutions that invest in proactive defense protect not only data but also patient trust and organizational credibility 🛡️.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

