➤Summary
The Iraq election data leak has sparked serious concern across cybersecurity communities after a forum post claimed that more than 20 million voter records linked to Iraq’s Independent High Electoral Commission (IHEC) were compromised and offered for sale online. According to a listing published on Darkforums.su by a user identified as “Shinchan,” the dataset allegedly contains extensive personal and electoral registration information collected during the November 2025 voting cycle. Reports describing the alleged IHEC data breach have quickly gained traction among analysts monitoring underground marketplaces and election infrastructure threats. As digital governance expands globally, incidents like this raise urgent questions about election security, citizen privacy, and the resilience of national databases. ⚠️
This darknetsearch.com article examines what is known so far, analyzes potential risks, and explains why the incident could represent a major turning point in election-related cyber threats.
What Was Allegedly Posted on Darkforums.su
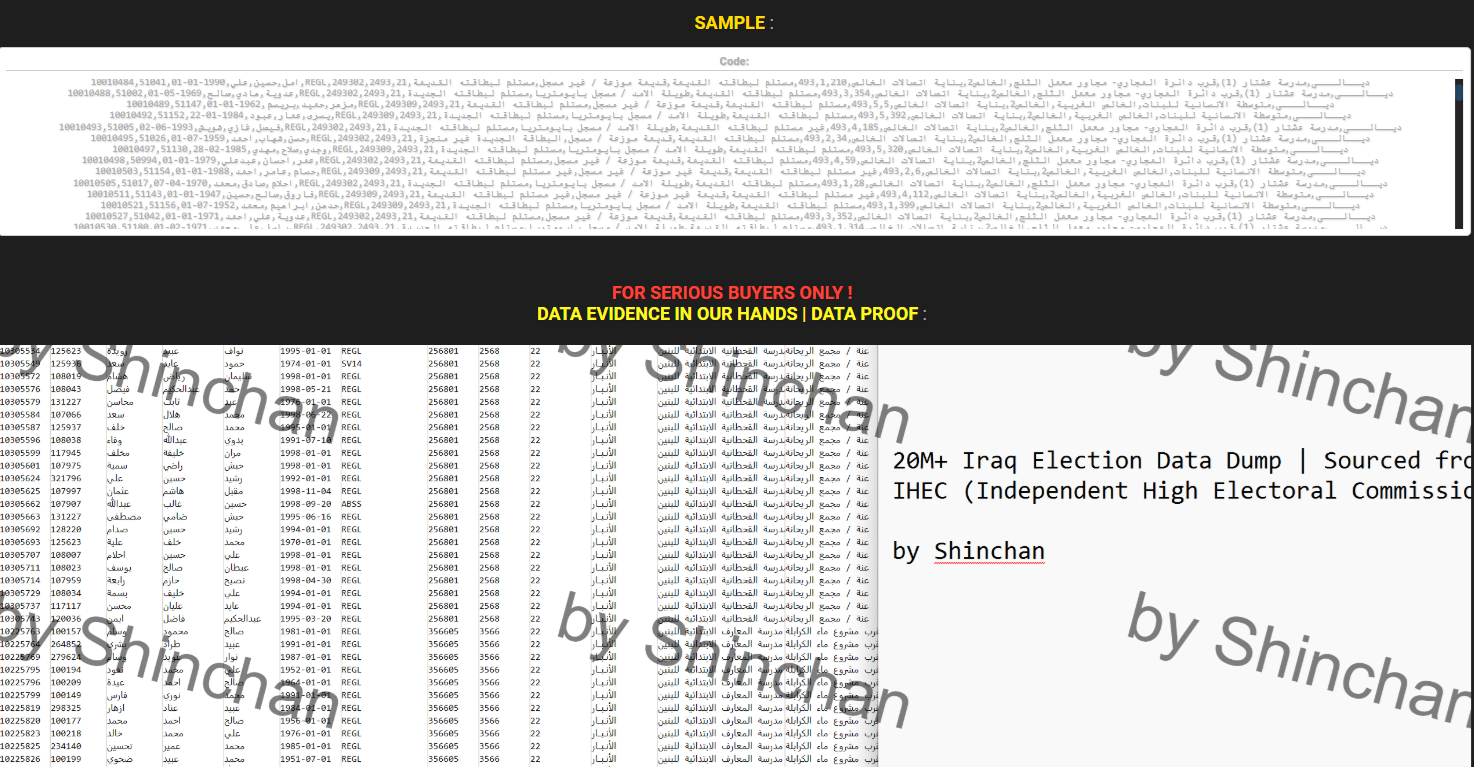
The forum listing claims access to personal election records sourced directly from Iraq’s electoral authority database. The seller states:
“we’ve got and selling personal election data from the Independent High Electoral Commission of Iraq (IHEC Iraq) available.”
According to the post, the last dataset update corresponds to vote-count information collected in November 2025. The data is not publicly downloadable; instead, buyers must contact the seller directly to negotiate pricing, a common tactic observed in cybercrime marketplaces. 🕵️♂️

Alleged compromised fields include:
- Person_ID
- Family_Registry_Number
- First, Father, and Grandfather Names
- Date_of_Birth
- Voter_Registration_Type
- Polling_Center_Number and Name
- Polling_Center_Address
- Governorate Administrative IDs
- Registration Center details
- Voter card status and production status
- Voting sequence identifiers
The breadth of fields suggests a structured administrative export rather than a simple scraped dataset, which is why researchers are treating the Iraq election data leak claim seriously despite limited independent verification.
Why Election Databases Are High-Value Targets
Election systems store uniquely sensitive datasets combining identity, location, and civic participation information. Unlike financial breaches, voter data cannot easily be replaced. Once exposed, the information may remain exploitable for years. 🎯
Cybercriminals value election databases because they enable:
- Identity fraud and impersonation
- Targeted phishing campaigns
- Political influence operations
- Social engineering against government employees
- Large-scale profiling of populations
The alleged IHEC data breach fits a broader global pattern where public institutions increasingly become targets due to centralized citizen data repositories.
Quick Facts About the Alleged Dataset
| Category | Details |
| Source Claimed | IHEC Iraq |
| Records | 20M+ voters |
| Forum | Darkforums.su |
| Seller | Shinchan |
| Status | For sale |
| Pricing | Private negotiation |
| Latest Data | November 2025 |
| This structured overview helps analysts quickly assess the potential scope and credibility indicators surrounding the leak. |
How Analysts Verify Claims Like This
When a dataset appears on underground forums, investigators follow a consistent verification workflow. The process does not rely solely on the seller’s claims.
Typical validation steps include:
- Sampling small data fragments.
- Comparing formats with known government schemas.
- Checking record consistency across regions.
- Identifying duplicates or synthetic entries.
- Monitoring reposts across marketplaces.
Security researchers often collaborate through intelligence-sharing platforms and sources like https://darknetsearch.com/ to track emerging threats and confirm legitimacy signals.
A practical example of monitoring resources can be found at:
- https://darknetsearch.com/marketplace-monitoring
- https://darknetsearch.com/dark-web-leak-analysis
These internal research hubs help map evolving cybercrime ecosystems.
Potential National Security and Privacy Risks
If verified, the Iraq election data leak could represent one of the largest exposures of voter information in the region. The risks extend beyond individual privacy. 🌍
Key impacts may include:
- Exposure of millions of citizens’ personal identifiers
- Increased disinformation targeting during future elections
- Manipulation attempts against polling infrastructure
- Loss of public trust in democratic institutions
- Long-term identity exploitation campaigns
Election-related breaches are particularly sensitive because they combine governance legitimacy with personal data protection. Even unconfirmed leaks can erode confidence if communication from authorities is delayed.
The Role of Underground Forums in Data Sales
Cybercrime forums act as decentralized marketplaces where reputation functions as currency. Sellers typically provide credibility through past transactions or partial previews.
Darkforums.su is part of a broader ecosystem where stolen datasets circulate before reaching brokers or ransomware groups. Analysts tracking the alleged IHEC data breach noticed familiar patterns:
- Limited public previews
- Direct-contact pricing
- Claims of exclusive access
- Time-based urgency messaging
These tactics create scarcity pressure to attract buyers quickly.
Researchers frequently cross-reference listings using investigative platforms and datasets aggregated at https://darknetsearch.com/ to identify duplicate leaks or recycled claims.
Could This Data Be Used for Political Manipulation?
Yes — and this is one of the most serious concerns.
Question: Can voter data leaks influence elections even without hacking voting machines?
Answer: Absolutely. Detailed voter information enables psychological targeting and tailored misinformation campaigns.
With geographic and demographic identifiers included, malicious actors could design messaging aimed at specific governorates or communities. This turns raw data into a strategic asset rather than merely stolen information. 📊
Experts in public sector threat intelligence warn that election datasets significantly amplify influence operations when combined with social media analytics.
Incident Response Considerations for Authorities
Government agencies facing a suspected leak must act quickly even before confirmation. Early action limits damage and reassures citizens.
Recommended incident response priorities include:
- Immediate forensic investigation
- Database access audits
- Credential rotation
- Public transparency updates
- Coordination with cybersecurity agencies
Communication strategy is crucial. Silence often increases speculation more than disclosure does. Authorities should also evaluate compliance with relevant Cybersecurity laws and regulations governing citizen data protection and breach notification.
Practical Checklist for Organizations Monitoring the Case
🔎 Security Monitoring Checklist:
- Track mentions of Iraq election datasets across forums.
- Monitor identity fraud spikes regionally.
- Verify reused datasets appearing under different names.
- Watch phishing campaigns referencing voter registration.
- Update threat intelligence feeds regularly.
Organizations using election-related datasets should also reassess vendor access controls and third-party integrations.
Broader Cybersecurity Context
The alleged 20 million Iraq voter database for sale highlights a growing trend: government datasets are increasingly monetized rather than leaked publicly. Attackers now prefer controlled sales that maximize profit while minimizing exposure. 💻
A report from the European Union Agency for Cybersecurity emphasizes that public-sector databases remain among the fastest-growing breach categories globally, largely due to legacy systems and complex administrative integrations.
As digital identity programs expand worldwide, election authorities must balance accessibility with robust security architecture.
Expert Perspective
Cybersecurity analysts frequently stress that election systems must be treated as critical infrastructure. One researcher summarized the issue succinctly:
“Election data breaches don’t just expose information — they challenge institutional legitimacy.”
This perspective explains why the Iraq election data leak discussion has extended beyond technical forums into geopolitical risk analysis.
What Happens Next?
At the time of writing, independent verification remains limited, and official confirmation from IHEC has not been publicly released. However, cybersecurity teams continue monitoring marketplace activity for proof samples or secondary resales — indicators that often confirm authenticity.
If validated, the alleged IHEC data breach could trigger international cooperation efforts involving digital forensics, law enforcement, and election security specialists. Governments worldwide are increasingly studying such incidents to strengthen defensive frameworks before future electoral cycles. 🔐
Conclusion: A Wake-Up Call for Election Security
Whether fully verified or not, the Iraq election data leak demonstrates how sensitive democratic infrastructure has become a prime cybercrime target. The incident underscores the importance of proactive monitoring, strong data governance, and rapid response planning. Election authorities, cybersecurity teams, and policymakers must treat voter databases as critical assets requiring continuous protection.
Understanding how underground markets operate and how data flows after breaches is essential for reducing long-term risks. Continuous monitoring, improved transparency, and coordinated defense strategies will determine whether similar incidents can be prevented in the future.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

