➤Summary
UAEERF data breach allegations surfaced after a database linked to uaeerf.ae, the official governing body for equestrian sports in the UAE, appeared on a dark web forum. The exposed content reportedly includes highly sensitive personal and financial information, raising serious concerns about privacy, compliance, and institutional cybersecurity. The incident was published on the forum Breachforums by the threat actor sexyskin on 20.02.2026, drawing attention from security researchers and organizations worldwide. According to findings by the Kaduu team, this exposure was identified during routine monitoring of illicit marketplaces and discussion boards. This UAEERF data breach highlights how quickly confidential records can circulate once compromised, making proactive detection and response critical in today’s threat landscape ⚠️
What Happened in the Alleged UAEERF Data Breach
The alleged UAEERF data breach involves a collection of CSV files shared publicly, suggesting unauthorized access to internal systems. The leaked datasets reportedly contain UAE ID numbers, bank details, phone numbers, full names, addresses, bank names, and email addresses 😟
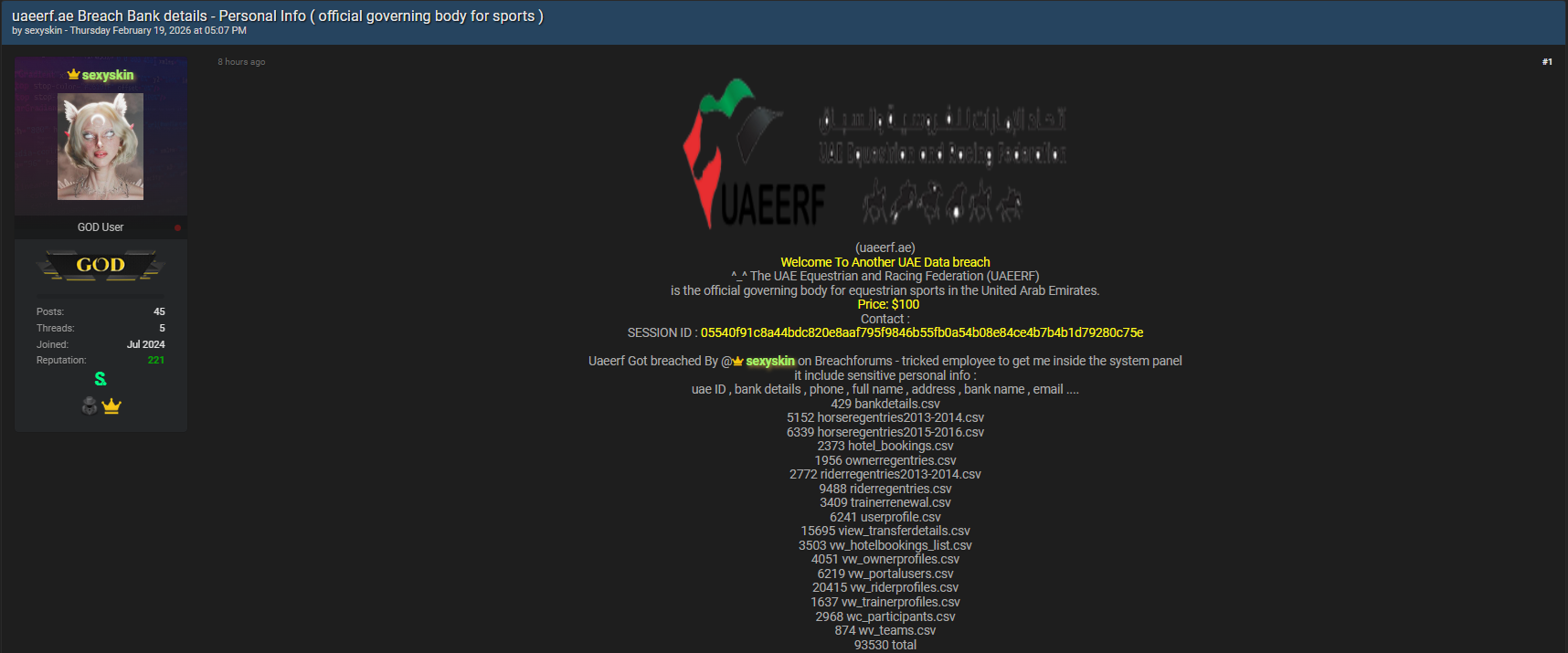
The scope of exposed data indicates a long-term aggregation rather than a single snapshot, increasing the potential risk for affected individuals.
Leaked Files and Exposed Records Overview
Below is a summary of the disclosed files, formatted for clarity and featured-snippet readiness 📊
- 429 bankdetails.csv
- 5,152 horseregentries2013-2014.csv
- 6,339 horseregentries2015-2016.csv
- 2,373 hotel_bookings.csv
- 1,956 ownerregentries.csv
- 2,772 riderregentries2013-2014.csv
- 9,488 riderregentries.csv
- 3,409 trainerrenewal.csv
- 6,241 userprofile.csv
- 15,695 view_transferdetails.csv
- 3,503 vw_hotelbookings_list.csv
- 4,051 vw_ownerprofiles.csv
- 6,219 vw_portalusers.csv
- 20,415 vw_riderprofiles.csv
- 1,637 vw_trainerprofiles.csv
- 2,968 wc_participants.csv
- 874 wv_teams.csv
This UAEERF data breach dataset volume suggests extensive historical records tied to owners, riders, trainers, and related stakeholders 🧾
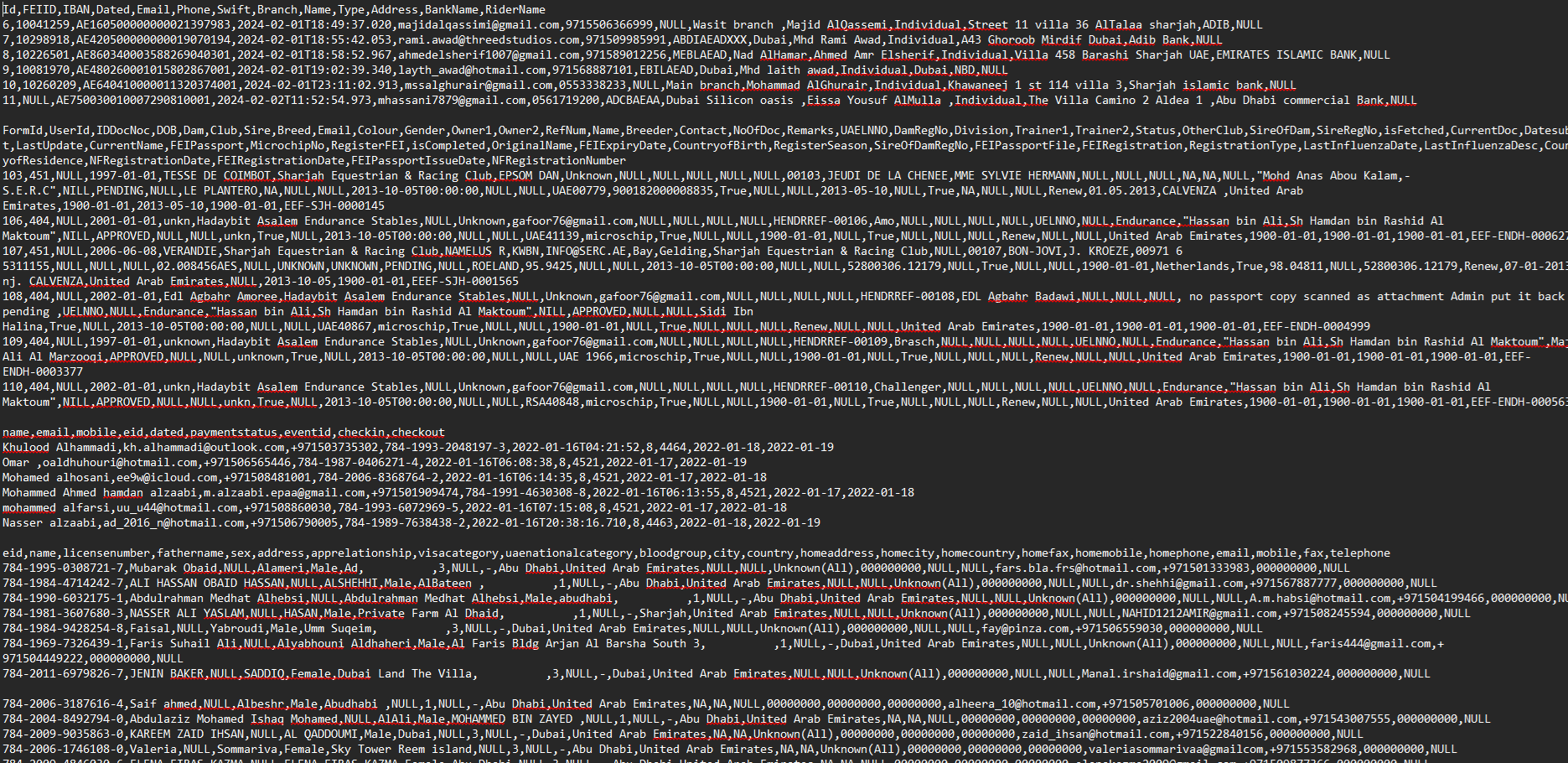
Why This UAEERF Data Breach Is High Risk
The inclusion of bank details and national identification data elevates this incident beyond a typical leak. Financial fraud, identity theft, and targeted phishing campaigns are realistic threats following such exposure 💳 One common question is: Does leaked historical data still pose a risk? The answer is yes—older records can still be exploited when combined with other breaches, enabling sophisticated social engineering attacks.
Discovery by Kaduu Dark Web Monitoring Team
The Kaduu team uncovered the database while operating a modern and effective dark web monitoring platform designed to detect emerging threats early 🔍 This discovery underscores the value of continuous surveillance across underground forums, paste sites, and marketplaces. Leveraging a robust dark web solution allows organizations to react before leaked data is widely weaponized.
Practical Checklist: How Organizations Can Respond
To reduce impact from incidents like the UAEERF data breach, security teams should follow this checklist ✅
- Monitor dark web forums continuously using trusted tools
- Validate leaked samples to assess authenticity
- Notify potentially affected users promptly
- Enforce credential resets and fraud monitoring
- Review access controls and third-party integrations
Broader Context and External Validation
Large-scale data leaks affecting sports and governmental bodies are increasingly common. Reputable platforms such as https://haveibeenpwned.com/ demonstrate how exposed credentials resurface years later, reinforcing the long-term impact of incidents like the UAEERF data breach 🌐 An industry expert once noted, “Detection speed on the dark web often determines whether a leak becomes a crisis or a controlled incident.”
Conclusion and Call to Action
The alleged UAEERF data breach serves as a clear reminder that sensitive databases tied to public institutions are prime targets for cybercriminals. Continuous monitoring, rapid response, and user awareness are no longer optional—they are essential 🔐 To stay ahead of emerging threats and learn how exposure is detected early, Discover much more in our complete guide and Request a demo NOW 🚀
Disclaimer: DarknetSearch reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
Discover how CISOs, SOC teams, and risk leaders use our platform to detect leaks, monitor the dark web, and prevent account takeover.
🚀Explore use cases →Q: What is dark web monitoring?
A: Dark web monitoring is the process of tracking your organization’s data on hidden networks to detect leaked or stolen information such as passwords, credentials, or sensitive files shared by cybercriminals.
Q: How does dark web monitoring work?
A: Dark web monitoring works by scanning hidden sites and forums in real time to detect mentions of your data, credentials, or company information before cybercriminals can exploit them.
Q: Why use dark web monitoring?
A: Because it alerts you early when your data appears on the dark web, helping prevent breaches, fraud, and reputational damage before they escalate.
Q: Who needs dark web monitoring services?
A: MSSP and any organization that handles sensitive data, valuable assets, or customer information from small businesses to large enterprises benefits from dark web monitoring.
Q: What does it mean if your information is on the dark web?
A: It means your personal or company data has been exposed or stolen and could be used for fraud, identity theft, or unauthorized access immediate action is needed to protect yourself.
Q: What types of data breach information can dark web monitoring detect?
A: Dark web monitoring can detect data breach information such as leaked credentials, email addresses, passwords, database dumps, API keys, source code, financial data, and other sensitive information exposed on underground forums, marketplaces, and paste sites.

